Efficient and Verifiable Ciphertext Retrieval Scheme Based on Trusted Execution Environment
-
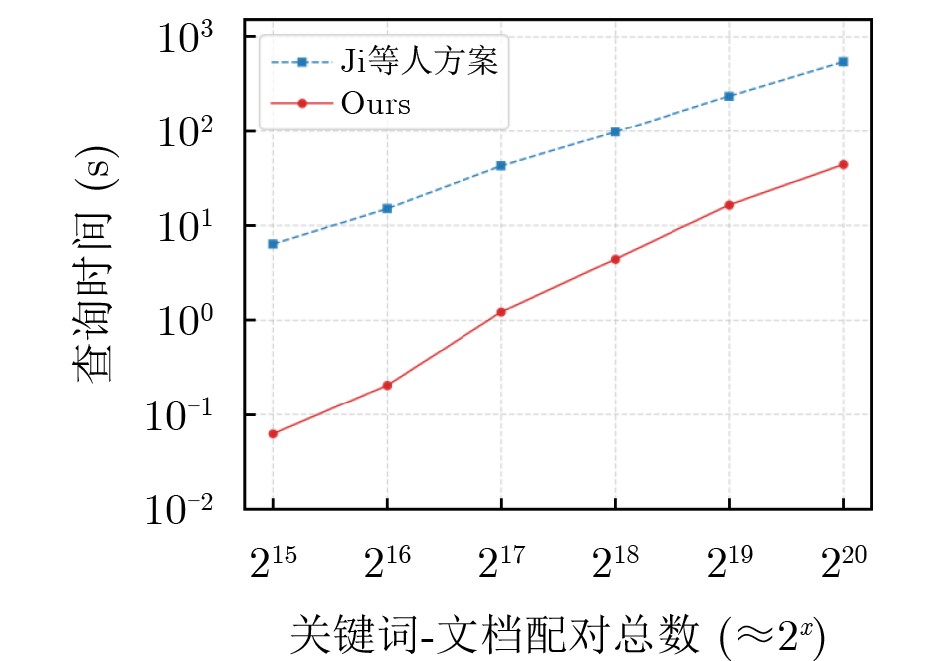
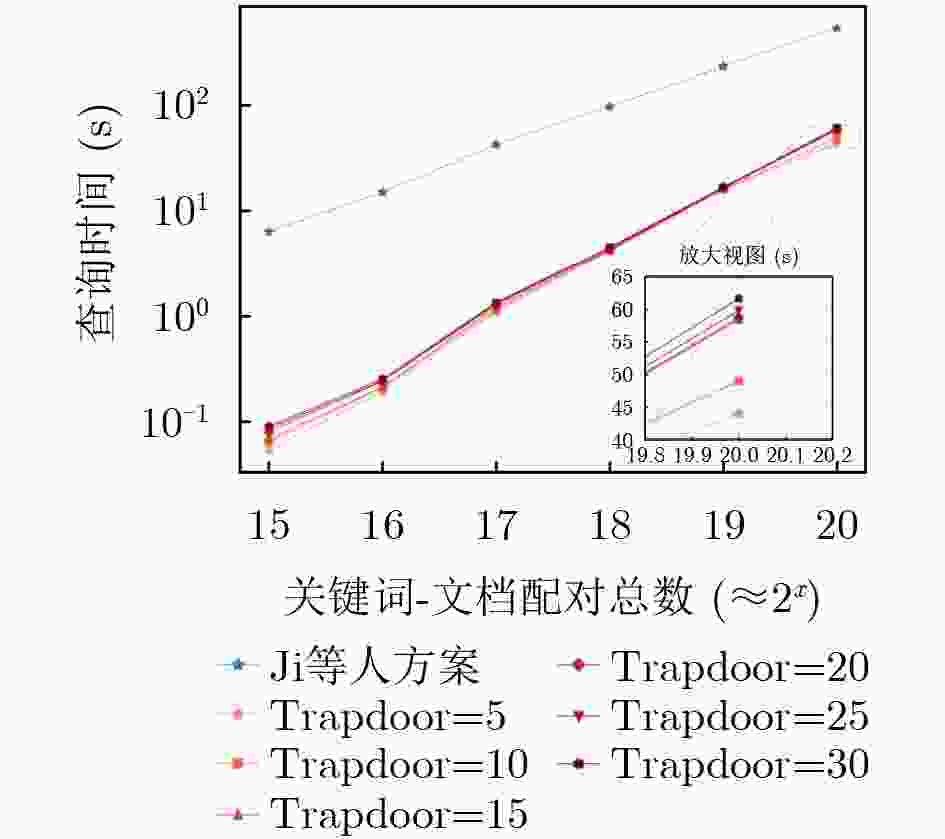
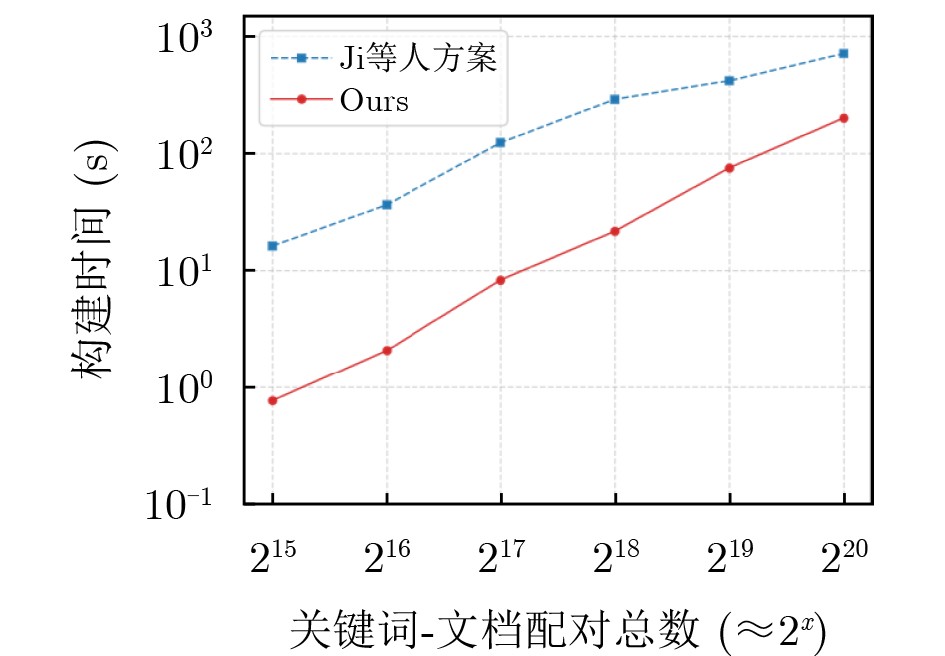
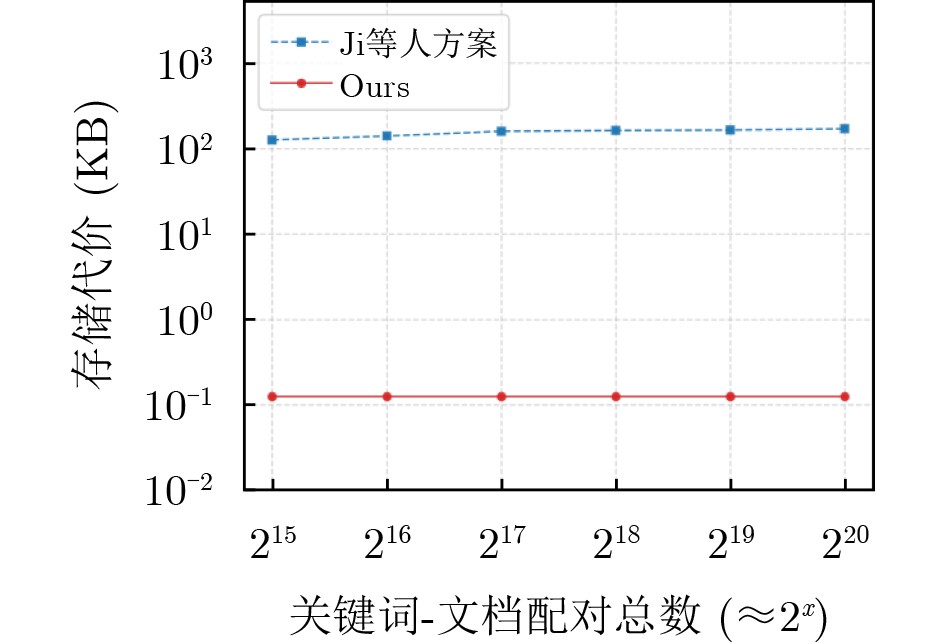
摘要: 密文检索(Ciphertext Retrieval)机制能够实现密态数据上的检索功能。对称可搜索加密(Symmetric Searchable Encryption, SSE)是密文检索的一个重要分支。然而,出于节省算力等特定因素的考虑,云服务器有可能会返回错误或不完整的结果。此外,攻击者也能利用搜索与访问模式的泄露信息还原出关键字内容。因此,在实现搜索结果可验证性的同时,保护搜索模式和访问模式的隐私,是很有必要和有意义的。但现有支持搜索模式和访问模式隐私的可验证SSE方案普遍需要关键字遍历机制且其验证机制的运行效率不尽理想。这些情况使得数据用户面临较高的计算成本和通信开销。针对上述性能瓶颈,该文提出一种基于可信执行环境(Trusted Execution Environment, TEE)的高效可验证密文检索方案。为提升密文检索等效率,该方案借助硬件级安全隔离与不经意数据重排的协同实现关键字陷门尺寸独立于关键字字典的规模。同时,通过嵌入随机数以及盲化多项式常数项方式验证返回结果的正确性。得益于上述设计,该方案在效率层面取得了显著提升。具体而言,其一,该方案使得关键字陷门规模仅与查询关键字数量相关,而与全局字典规模无关,有效降低计算和通信成本;其二,该方案仅需存储两个随机数即可实现可验证功能,大幅降低用户本地存储开销。其三,数据用户与单服务器单轮交互中获取检索结果以及对称同态加密机制的应用等技术进一步提升了运行效率。此外,TEE中的密态计算弱化了对TEE的安全假设和信任程度。在通过模拟游戏方式完成对方案安全性的证明之后,该文对所提出的方案进行了综合的性能评估,评估结果证实了该方案效率上显著优于其他具备相同功能的方案。Abstract: The ciphertext retrieval mechanism enables retrieval functionality over encrypted data. Symmetric Searchable Encryption (SSE) is a critical branch of ciphertext retrieval. However, due to considerations such as saving computing power, cloud servers may return incorrect or incomplete results. Moreover, attackers can also exploit these leaked information from search and access patterns to reconstruct the keyword details. Therefore, it is necessary and meaningful to protect the privacy of search and access patterns while achieving result verifiability. Nevertheless, existing verifiable SSE schemes that support search and access pattern privacy typically rely on keyword traversal mechanisms and their verification mechanisms are inefficient, which impose high computational and communication overheads on users. To address the above performance bottlenecks, this paper introduces an efficient and verifiable ciphertext retrieval scheme based on Trusted Execution Environment (TEE). To improve the efficiency of ciphertext retrieval, this scheme employs the collaborative implementation of hardware-level security isolation and oblivious data rearrangement to achieve keyword trapdoor size independent of the size of the keyword dictionary. Meanwhile, the correctness of the returned results is verified by embedding random numbers and blinding polynomial constant terms. Thanks to these designs, the scheme achieves significant efficiency improvements. Specifically, firstly, this scheme ensures that the size of keyword trapdoors depends solely on the number of query keywords, not the global dictionary size, effectively minimizing communication and computational costs. Secondly, this scheme requires storing only two random numbers to enable verifiability, substantially minimizing local storage overhead for users. Thirdly, the adoption of techniques, such as enabling data users to retrieve results via single-server and single-round interaction and leveraging symmetric homomorphic encryption, further enhances operational efficiency. Additionally, confidential computing within TEE weakens the security assumptions and trust level towards TEE. After formally proving the security of the proposed scheme using simulation-based methods, this paper has conducted a comprehensive performance evaluation. The evaluation results confirm that this scheme is significantly more efficient than other schemes with the same functionalities.
-
1 加密数据的构建$ \boldsymbol{D}\boldsymbol{B}\boldsymbol{B}\boldsymbol{u}\boldsymbol{i}\boldsymbol{l}\boldsymbol{d} $
输入:$ \boldsymbol{\lambda } $和$ \boldsymbol{D}\boldsymbol{B} $ 输出:$ \boldsymbol{E}\boldsymbol{D}\boldsymbol{B}\boldsymbol{t}\boldsymbol{r}\boldsymbol{e}\boldsymbol{e} $,$ \boldsymbol{P}\boldsymbol{M} $,$ \boldsymbol{V}\boldsymbol{K} $和$ \boldsymbol{S}\boldsymbol{K} $ $ \boldsymbol{E}\boldsymbol{D}\boldsymbol{B}\leftarrow \boldsymbol{\varnothing } $ 参数选择 设关键字字典$ \boldsymbol{W} $的大小为$ \boldsymbol{m} $ 选择一个随机数$ \boldsymbol{\beta } $和一个随机数$ \boldsymbol{\theta } $ 随机选择两个哈希函数$ {\boldsymbol{H}\colon \{\mathbf{0},\mathbf{1}\}}^{\boldsymbol{*}}\rightarrow {\mathbb{Z}}_{\boldsymbol{p}} $ 随机抽样一个私钥为$ \boldsymbol{k} $的伪随机函数$ \boldsymbol{F} $ 初始化一个私钥为$ \boldsymbol{s}\boldsymbol{k} $的对称同态加密算法$ \boldsymbol{A}\boldsymbol{S}\boldsymbol{H}\boldsymbol{E}=(\boldsymbol{S}\boldsymbol{e}\boldsymbol{t}\boldsymbol{u}\boldsymbol{p},\boldsymbol{E}\boldsymbol{n}\boldsymbol{c},\boldsymbol{D}\boldsymbol{e}\boldsymbol{c}) $ 具体步骤 1 $ \boldsymbol{L}={\{|\boldsymbol{D}\boldsymbol{B}\left({\boldsymbol{w}}_{\boldsymbol{i}}\right)|\}}_{\boldsymbol{m}\boldsymbol{a}\boldsymbol{x}} $ 2 对于每个关键字$ {\boldsymbol{w}}_{\boldsymbol{i}}\in \boldsymbol{W} $,执行下面的算法: 3 $ {\boldsymbol{k}}_{{{\boldsymbol{w}}_{\boldsymbol{i}}}}\leftarrow \boldsymbol{F}\left(\boldsymbol{k},{\boldsymbol{w}}_{\boldsymbol{i}}\right) $ 4 $ {\boldsymbol{P}}_{{{\boldsymbol{w}}_{\boldsymbol{i}}}}\left(\boldsymbol{x}\right)={\boldsymbol{x}}^{\boldsymbol{L}-\left| \boldsymbol{D}\boldsymbol{B}\left({\boldsymbol{w}}_{\boldsymbol{i}}\right)\right| }{(\boldsymbol{x}-\boldsymbol{\beta })\prod }_{\boldsymbol{i}\boldsymbol{d}\in \boldsymbol{D}\boldsymbol{B}\left({\boldsymbol{w}}_{\boldsymbol{i}}\right)}(\boldsymbol{x}-(\boldsymbol{i}\boldsymbol{d}||\boldsymbol{H}\left(\boldsymbol{i}\boldsymbol{d}\right)))=\displaystyle\sum\nolimits _{\boldsymbol{j}=\mathbf{0}}^{\boldsymbol{j}=\boldsymbol{L}+\mathbf{1}}{{{\boldsymbol{\tau }}_{\boldsymbol{i}\boldsymbol{j}}}\boldsymbol{x}}^{\boldsymbol{j}} $ 5 $ {\boldsymbol{E}\boldsymbol{D}\boldsymbol{B}}_{{{\boldsymbol{w}}_{\boldsymbol{i}}}}={\boldsymbol{E}\boldsymbol{n}\boldsymbol{c}}_{\boldsymbol{s}\boldsymbol{k}}\left({\boldsymbol{P}}_{{{\boldsymbol{w}}_{\boldsymbol{i}}}}\left(\boldsymbol{x}\right)-\boldsymbol{H}({\boldsymbol{w}}_{\boldsymbol{i}}||\boldsymbol{\theta })\right)={{\displaystyle\sum\nolimits _{\boldsymbol{j}=\mathbf{0}}^{\boldsymbol{L}+\mathbf{1}}}\boldsymbol{E}\boldsymbol{n}\boldsymbol{c}}_{\boldsymbol{h}\boldsymbol{p}\boldsymbol{k}}\left({\boldsymbol{\tau }}_{\boldsymbol{i}\boldsymbol{j}}\right){\boldsymbol{x}}^{\boldsymbol{j}} $ 6 $ \boldsymbol{E}\boldsymbol{D}\boldsymbol{B}\leftarrow (({\boldsymbol{k}}_{{{\boldsymbol{w}}_{\mathbf{1}}}},{\boldsymbol{E}\boldsymbol{D}\boldsymbol{B}}_{{{\boldsymbol{w}}_{\mathbf{1}}}}),{\boldsymbol{k}}_{{{\boldsymbol{w}}_{\mathbf{2}}}},{\boldsymbol{E}\boldsymbol{D}\boldsymbol{B}}_{{{\boldsymbol{w}}_{\mathbf{2}}}}),\cdots ,({\boldsymbol{k}}_{{{\boldsymbol{w}}_{\boldsymbol{m}}}},{\boldsymbol{E}\boldsymbol{D}\boldsymbol{B}}_{{{\boldsymbol{w}}_{\boldsymbol{m}}}})) $和$ \boldsymbol{V}\boldsymbol{K}\leftarrow \boldsymbol{\beta },\boldsymbol{\theta } $ 7 初始化Path ORAM二叉树结构EDBtree; 8 PM$ \leftarrow $随机将每个关键字映射到一条路径; 9 对每个关键字对应的多项式执行: 10 将多项式加密为数据块; 11 将数据块插入到关键字映射路径上的对应桶中; 12 使用虚拟块(dummy blocks)将每个桶填充至大小S; 13 返回加密数据库$ \boldsymbol{E}\boldsymbol{D}\boldsymbol{B}\boldsymbol{t}\boldsymbol{r}\boldsymbol{e}\boldsymbol{e} $,$ \boldsymbol{P}\boldsymbol{M} $,$ \boldsymbol{V}\boldsymbol{K} $和私钥$ \boldsymbol{S}\boldsymbol{K}=\left(\boldsymbol{k},\boldsymbol{s}\boldsymbol{k}\right) $; 14 上传$ \boldsymbol{E}\boldsymbol{D}\boldsymbol{B}\boldsymbol{t}\boldsymbol{r}\boldsymbol{e}\boldsymbol{e} $到云服务器的不可信环境; 15 通过安全信道上传PM到云服务器的Enclave。 2 关键字陷门生成$ \boldsymbol{T}\boldsymbol{r}\boldsymbol{a}\boldsymbol{p}\boldsymbol{d}\boldsymbol{o}\boldsymbol{o}\boldsymbol{r} $
输入:$ \boldsymbol{s}\boldsymbol{k} $和被询问的关键字集合$ \boldsymbol{Q} $ 输出:关键字陷门$ \boldsymbol{T}\boldsymbol{o}\boldsymbol{k}\boldsymbol{e}\boldsymbol{n} $ 1 对于$ {\boldsymbol{w}}_{\boldsymbol{i}}\in \boldsymbol{Q} $,执行下面的循环: 2 $ {\boldsymbol{k}}_{{{\boldsymbol{w}}_{\boldsymbol{i}}}\boldsymbol{'}}\leftarrow \boldsymbol{F}\left(\boldsymbol{k},{\boldsymbol{w}}_{\boldsymbol{i}}\right) $。 3 返回关键字陷门$ \boldsymbol{T}\boldsymbol{o}\boldsymbol{k}\boldsymbol{e}\boldsymbol{n}=\{{\boldsymbol{k}}_{{{\boldsymbol{w}}_{\mathbf{1}}}\boldsymbol{'}},{\boldsymbol{k}}_{{{\boldsymbol{w}}_{\mathbf{2}}}\boldsymbol{'}},\cdots ,{\boldsymbol{k}}_{{{\boldsymbol{w}}_{\boldsymbol{n}}}\boldsymbol{'}}\} $ 4 通过与TEE建立的安全信道上传到Enclave中 3 搜索过程$ \boldsymbol{S}\boldsymbol{e}\boldsymbol{a}\boldsymbol{r}\boldsymbol{c}\boldsymbol{h} $
输入:$ \mathbf{EDBtree} $,和$ \boldsymbol{T}\boldsymbol{o}\boldsymbol{k}\boldsymbol{e}\boldsymbol{n} $ 输出:搜索结果$ \boldsymbol{R} $ 云服务器 // Enclave 1 $ \boldsymbol{R}\leftarrow \{\} $ 2 解析$ \boldsymbol{T}\boldsymbol{o}\boldsymbol{k}\boldsymbol{e}\boldsymbol{n}=\{{\boldsymbol{k}}_{{{\boldsymbol{w}}_{\mathbf{1}}}\boldsymbol{'}}{\boldsymbol{k}}_{{{\boldsymbol{w}}_{\mathbf{2}}}\boldsymbol{'}},\cdots ,{\boldsymbol{k}}_{{{\boldsymbol{w}}_{\boldsymbol{n}}}\boldsymbol{'}}\} $ 3 对于$ {\boldsymbol{k}}_{{{\boldsymbol{w}}_{\boldsymbol{i}}}\boldsymbol{'}} $执行: 4 如果$ {\boldsymbol{k}}_{{{\boldsymbol{w}}_{\boldsymbol{i}}}\boldsymbol{'}} $对应的多项式数据块不在STASH中,执行: 5 从PM中读取对应的路径PATH; 6 Enclave调用Path ORAM的Access (PATH, EDBtree)接口,从不可信环境中读取EDBtree中PATH路径上的密文数据块; 7 解密数据块并得到$ {\boldsymbol{k}}_{{{\boldsymbol{w}}_{\boldsymbol{i}}}\boldsymbol{'}} $对应的加密多项式; 8 计算$ {\boldsymbol{E}\boldsymbol{n}\boldsymbol{c}}_{\boldsymbol{s}\boldsymbol{k}}(\mathbb{P}\left(\boldsymbol{x}\right)\boldsymbol{'})={\boldsymbol{E}\boldsymbol{D}\boldsymbol{B}}_{{{\boldsymbol{w}}_{\mathbf{1}}}\boldsymbol{'}} $+···+$ {\boldsymbol{E}\boldsymbol{D}\boldsymbol{B}}_{{{\boldsymbol{w}}_{\boldsymbol{i}}}\boldsymbol{'}} $+···+$ {\boldsymbol{E}\boldsymbol{D}\boldsymbol{B}}_{{{\boldsymbol{w}}_{\boldsymbol{n}}}\boldsymbol{'}} $ $ \text{=}{\boldsymbol{E}\boldsymbol{n}\boldsymbol{c}}_{\boldsymbol{s}\boldsymbol{k}}(\left({\boldsymbol{P}}_{{{\boldsymbol{w}}_{\mathbf{1}}}\boldsymbol{'}}\left(\boldsymbol{x}\right)-\boldsymbol{H}({\boldsymbol{w}}_{\mathbf{1}}||\boldsymbol{\theta })\right)+\cdots +\left({\boldsymbol{P}}_{{{\boldsymbol{w}}_{\boldsymbol{n}}}\boldsymbol{'}}\left(\boldsymbol{x}\right)-\boldsymbol{H}({\boldsymbol{w}}_{\boldsymbol{n}}||\boldsymbol{\theta })\right)) $ 9 将搜索结果$ {\boldsymbol{E}\boldsymbol{n}\boldsymbol{c}}_{\boldsymbol{s}\boldsymbol{k}}\left(\mathbb{P}\left(\boldsymbol{x}\right)\boldsymbol{'}\right) $返回给数据用户。 数据用户 10 数据用户通过解密密钥$ \boldsymbol{s}\boldsymbol{k} $计算出明文$ \mathbb{P}{\left(\boldsymbol{x}\right)}^{\boldsymbol{'}}={\boldsymbol{D}\boldsymbol{e}\boldsymbol{c}}_{\boldsymbol{s}\boldsymbol{k}}\left({\boldsymbol{E}\boldsymbol{n}\boldsymbol{c}}_{\boldsymbol{s}\boldsymbol{k}}\left(\mathbb{P}{\left(\boldsymbol{x}\right)}^{\boldsymbol{'}}\right)\right)=\left({\boldsymbol{P}}_{{{\boldsymbol{w}}_{\mathbf{1}}}\boldsymbol{'}}\left(\boldsymbol{x}\right)-\boldsymbol{H}({\boldsymbol{w}}_{\mathbf{1}}||\boldsymbol{\theta })\right)+\cdots +$
$\left({\boldsymbol{P}}_{{{\boldsymbol{w}}_{\boldsymbol{n}}}\boldsymbol{'}}\left(\boldsymbol{x}\right)-\boldsymbol{H}({\boldsymbol{w}}_{\boldsymbol{n}}||\boldsymbol{\theta })\right) $11 对于$ {\boldsymbol{w}}_{\boldsymbol{i}}\in \boldsymbol{Q}=({\boldsymbol{w}}_{\mathbf{1}},{\boldsymbol{w}}_{\mathbf{2}},\cdots ,{\boldsymbol{w}}_{\boldsymbol{n}}) $,数据用户通过$ \boldsymbol{V}\boldsymbol{K} $获得$ \mathbb{P}\left(\boldsymbol{x}\right)=\mathbb{P}{\left(\boldsymbol{x}\right)}^{\boldsymbol{'}}+\boldsymbol{H}({\boldsymbol{w}}_{\mathbf{1}}||\boldsymbol{\theta })+\cdots +\boldsymbol{H}({\boldsymbol{w}}_{\boldsymbol{n}}||\boldsymbol{\theta }) $ 12 如果$ {\mathbb{P}}_{\boldsymbol{\alpha }}\left(\boldsymbol{\beta }\right)\neq \mathbf{0} $,数据用户拒绝搜索结果。如果验证通过,则数据用户计算出多项式$ \mathbb{P}\left(\boldsymbol{x}\right) $的根,然后从中找到符合格式$ \boldsymbol{i}\boldsymbol{d}||\boldsymbol{H}\left(\boldsymbol{i}\boldsymbol{d}\right) $的有效根并将其添加到结果$ \boldsymbol{R} $中。 算法模拟 输入:$ {\mathcal{L}}_{\boldsymbol{I}}\boldsymbol{'}=(\boldsymbol{m},\boldsymbol{L},\boldsymbol{n}) $ 输出:$ \boldsymbol{E}\boldsymbol{D}\boldsymbol{B} $和$ \boldsymbol{T}\boldsymbol{o}\boldsymbol{k}\boldsymbol{e}\boldsymbol{n} $ 加密数据$ \mathit{E}\mathit{D}\mathit{B} $的生成: 1 $ \boldsymbol{E}\boldsymbol{D}\boldsymbol{B}\leftarrow \boldsymbol{\varnothing } $ 2 对于$ \boldsymbol{i}\in [\mathbf{1},\boldsymbol{m}] $,执行下面的算法: 3 选择随机数$ {\boldsymbol{k}}_{{{\boldsymbol{w}}_{\boldsymbol{i}}}} $并记录元组$ (\boldsymbol{i},{\boldsymbol{k}}_{{{\boldsymbol{w}}_{\boldsymbol{i}}}}) $到表格$ \boldsymbol{T} $中 4 选择$ \boldsymbol{L} $+1个随机数$ {\boldsymbol{\eta }}_{\boldsymbol{j}} $得到$ {\boldsymbol{E}\boldsymbol{D}\boldsymbol{B}}_{{{\boldsymbol{w}}_{\boldsymbol{i}}}}=\displaystyle\sum\nolimits_{\boldsymbol{j}=\mathbf{1}}^{\boldsymbol{L}+\mathbf{1}}{\boldsymbol{\eta }}_{\boldsymbol{j}}{\boldsymbol{x}}^{\boldsymbol{j}} $ 5 生成$ \boldsymbol{E}\boldsymbol{D}\boldsymbol{B}=(({\boldsymbol{k}}_{{{\boldsymbol{w}}_{\mathbf{1}}}},{\boldsymbol{E}\boldsymbol{D}\boldsymbol{B}}_{\mathbf{1}}),{\boldsymbol{k}}_{{{\boldsymbol{w}}_{\mathbf{2}}}},{\boldsymbol{E}\boldsymbol{D}\boldsymbol{B}}_{\mathbf{2}}),\cdots , $
$({\boldsymbol{k}}_{{{\boldsymbol{w}}_{\boldsymbol{m}}}},{\boldsymbol{E}\boldsymbol{D}\boldsymbol{B}}_{\boldsymbol{m}})) $生成陷门$ \mathit{T}\mathit{o}\mathit{k}\mathit{e}\mathit{n} $ 6 对于$ \boldsymbol{i}\in [\mathbf{1},\boldsymbol{n}] $,执行下面的循环: 7 从$ \boldsymbol{T} $中根据索引选出$ {\boldsymbol{k}}_{{{\boldsymbol{w}}_{\boldsymbol{i}}}} $ 8 返回关键字陷门$ \boldsymbol{T}\boldsymbol{o}\boldsymbol{k}\boldsymbol{e}\boldsymbol{n}=\{{\boldsymbol{k}}_{{{\boldsymbol{w}}_{\mathbf{1}}}},{\boldsymbol{k}}_{{{\boldsymbol{w}}_{\mathbf{2}}}},\cdots ,{\boldsymbol{k}}_{{{\boldsymbol{w}}_{\boldsymbol{n}}}}\} $ 表 1 搜索模式和访问模式隐藏的可验证多关键字可搜索加密机制比较
方案 计算代价 本地通讯代价 本地存储代价 加法同态加密机制 初始化 陷门生成 搜索阶段 初始化 搜索 Wu方案[18] $ \mathrm{O}(\mathrm{mL}) $ $ \mathrm{O}(\mathrm{m}) $ $ \mathrm{O}(\mathrm{mL}) $ $ \mathrm{O}(\mathrm{mL}) $ $ \mathrm{O}(\mathrm{mL}) $ $ \mathrm{O}(1) $ 公钥加密 Ji方案[19] $ \mathrm{O}(\mathrm{mL}) $ $ \mathrm{O}(\mathrm{m}) $ $ \mathrm{O}(\mathrm{mL}) $ $ \mathrm{O}(\mathrm{mL}) $ $ \mathrm{O}(\mathrm{mL}) $ $ \mathrm{O}(\mathrm{m}) $ 对称机制 我们的方案 $ \mathrm{O}(\mathrm{mL}) $ $ \mathrm{O}(\mathrm{n}) $ $ \mathrm{n*O}(\mathrm{log}\mathrm{N}) $ $ \mathrm{O}(\mathrm{mL}) $ $ \mathrm{O}(\mathrm{log}\mathrm{L}) $ $ \mathrm{O}(1) $ 对称机制 $ \mathrm{m} $是关键字字典集合的大小;$ \mathrm{L} $是包含关键字文档标识集合大小的最大值;$ \mathrm{n} $是要搜索关键字集合的大小;$ \mathrm{N} $是Path ORAM桶的数量。 -
[1] SINGH A and CHATTERJEE K. Cloud security issues and challenges: A survey[J]. Journal of Network and Computer Applications, 2017, 79: 88–115. doi: 10.1016/j.jnca.2016.11.027. [2] 张玉清, 王晓菲, 刘雪峰, 等. 云计算环境安全综述[J]. 软件学报, 2016, 27(6): 1328–1348. doi: 10.13328/j.cnki.jos.005004.ZHANG Yuqing, WANG Xiaofei, LIU Xuefeng, et al. Survey on cloud computing security[J]. Journal of Software, 2016, 27(6): 1328–1348. doi: 10.13328/j.cnki.jos.005004. [3] RAGHAVENDRA S, REDDY C S, GEETA C M, et al. Survey on data storage and retrieval techniques over encrypted cloud data[J]. International Journal of Computer Science and Information Security, 2016, 14(9): 718. (查阅网上资料, 未找到本条文献信息, 请确认). [4] 王祥宇, 马鑫迪, 梁岩荣, 等. 开放大数据安全存储与检索系统[J]. 网络空间安全科学学报, 2024, 2(3): 13–26. doi: 10.20172/j.issn.2097-3136.240302.WANG Xiangyu, MA Xindi, LIANG Yanrong, et al. Secure storage and retrieval system for open big data[J]. Journal of Cybersecurity, 2024, 2(3): 13–26. doi: 10.20172/j.issn.2097-3136.240302. [5] 迟佳琳, 冯登国, 张敏, 等. 隐私保护密文检索技术研究进展[J]. 电子与信息学报, 2024, 46(5): 1546–1569. doi: 10.11999/JEIT231300.CHI Jialin, FENG Dengguo, ZHANG Min, et al. Advances in privacy-preserving ciphertext retrieval[J]. Journal of Electronics & Information Technology, 2024, 46(5): 1546–1569. doi: 10.11999/JEIT231300. [6] LI Feng, MA Jianfeng, MIAO Yinbin, et al. A survey on searchable symmetric encryption[J]. ACM Computing Surveys, 2024, 56(5): 119. doi: 10.1145/3617991. [7] WANG Na, ZHOU Wen, HAN Qingyun, et al. A lightweight privacy-preserving ciphertext retrieval scheme based on edge computing[J]. IEEE Transactions on Cloud Computing, 2024, 12(4): 1273–1290. doi: 10.1109/TCC.2024.3461732. [8] DOU Haochen, DAN Zhenwu, XU Peng, et al. Dynamic searchable symmetric encryption with strong security and robustness[J]. IEEE Transactions on Information Forensics and Security, 2024, 19: 2370–2384. doi: 10.1109/TIFS.2024.3350330. [9] GAO Nan, FAN Kai, WANG Haoyang, et al. Dynamic multi-user authorization in ciphertext retrieval with proxy re-encryption[J]. IEEE Transactions on Dependable and Secure Computing, 2025, 22(6): 5918–5930. doi: 10.1109/TDSC.2025.3577208. [10] WU Axin, YANG Anjia, LUO Weiqi, et al. Enabling traceable and verifiable multi-user forward secure searchable encryption in hybrid cloud[J]. IEEE Transactions on Cloud Computing, 2023, 11(2): 1886–1898. doi: 10.1109/tcc.2022.3170362. [11] OYA S and KERSCHBAUM F. Hiding the access pattern is not enough: Exploiting search pattern leakage in searchable encryption[C]. Proceedings of the 30th USENIX Security Symposium, 2021. (查阅网上资料, 未找到对应的出版地信息, 请确认). [12] CASH D, GRUBBS P, PERRY J, et al. Leakage-abuse attacks against searchable encryption[C]. Proceedings of the 22nd ACM SIGSAC Conference on Computer and Communications Security, Denver Colorado, USA, 2015: 668–679. doi: 10.1145/2810103.2813700. [13] LIU Chang, ZHU Liehuang, WANG Mingzhong, et al. Search pattern leakage in searchable encryption: Attacks and new construction[J]. Information Sciences, 2014, 265: 176–188. doi: 10.1016/j.ins.2013.11.021. [14] WANG Yunling, SUN Shifeng, WANG Jianfeng, et al. Achieving searchable encryption scheme with search pattern hidden[J]. IEEE Transactions on Services Computing, 2022, 15(2): 1012–1025. doi: 10.1109/TSC.2020.2973139. [15] SONG Qiyang, LIU Zhuotao, CAO Jiahao, et al. SAP-SSE: Protecting search patterns and access patterns in searchable symmetric encryption[J]. IEEE Transactions on Information Forensics and Security, 2021, 16: 1795–1809. doi: 10.1109/tifs.2020.3042058. [16] SHANG Zhiwei, OYA S, PETER A, et al. Obfuscated access and search patterns in searchable encryption[C]. Proceedings of the 28th Annual Network and Distributed System Security Symposium, 2021: 1–18. (查阅网上资料, 未找到对应的出版地信息, 请确认). [17] YANG Yunbo, HU Yiwei, DONG Xiaolei, et al. OpenSE: Efficient verifiable searchable encryption with access and search pattern hidden for cloud-IoT[J]. IEEE Internet of Things Journal, 2024, 11(8): 13793–13809. doi: 10.1109/jiot.2023.3337336. [18] WU Axin, FENG Dengguo, ZHANG Min, et al. Efficient verifiable searchable encryption with search and access pattern privacy[J]. Security and Safety, 2025, 4: 2024022. doi: 10.1051/sands/2024022. [19] JI Licheng, LI Jiguo, ZHANG Yicheng, et al. Verifiable searchable symmetric encryption over additive homomorphism[J]. IEEE Transactions on Information Forensics and Security, 2025, 20: 1320–1332. doi: 10.1109/TIFS.2025.3526062. [20] LI Mengyuan, YANG Yuheng, CHEN Guoxing, et al. SoK: Understanding design choices and pitfalls of trusted execution environments[C]. Proceedings of the 19th ACM Asia Conference on Computer and Communications Security, Singapore, Singapore, 2024: 1600–1616. doi: 10.1145/3634737.3644993. [21] SUN H and JAFAR S A. The capacity of private information retrieval[J]. IEEE Transactions on Information Theory, 2017, 63(7): 4075–4088. doi: 10.1109/TIT.2017.2689028. [22] FERREIRA B, PORTELA B, OLIVEIRA T, et al. Boolean searchable symmetric encryption with filters on trusted hardware[J]. IEEE Transactions on Dependable and Secure Computing, 2022, 19(2): 1307–1319. doi: 10.1109/TDSC.2020.3012100. [23] FUHRY B, BAHMANI R, BRASSER F, et al. HardIDX: Practical and secure index with SGX[C]. Proceedings of the 31st Annual IFIP WG 11.3 Conference on Data and Applications Security and Privacy XXXI, Philadelphia, USA, 2017. doi: 10.1007/978-3-319-61176-1_22. [24] JIANG Qin, CHANG E C, QI Yong, et al. Rphx: Result pattern hiding conjunctive query over private compressed index using Intel SGX[J]. IEEE Transactions on Information Forensics and Security, 2022, 17: 1053–1068. doi: 10.1109/TIFS.2022.3144877. [25] WU Haotian, PENG Zhe, XIAO Jiang, et al. HeX: Encrypted rich queries with forward and backward privacy using trusted hardware[J]. IEEE Transactions on Dependable and Secure Computing, 2025, 22(4): 3751–3765. doi: 10.1109/TDSC.2025.3540958. [26] JIANG Qin, QI Yong, QI Saiyu, et al. Pbsx: A practical private boolean search using Intel SGX[J]. Information Sciences, 2020, 521: 174–194. doi: 10.1016/j.ins.2020.02.031. [27] TINOCO A, GAO Sixiang, and SHI E. ENIGMAP: External-memory oblivious map for secure enclaves[C]. Proceedings of the 32nd USENIX Conference on Security Symposium, Anaheim, USA, 2023: 226. [28] YE Zikai, WANG Xiangyu, LIU Zesen, et al. OBIR-tree: An efficient oblivious index for spatial keyword queries on secure enclaves[J]. Proceedings of the ACM on Management of Data, 2025, 3(1): 58. doi: 10.1145/3709708. [29] WANG Tao, WANG Jingyi, YANG Qiliang, et al. An efficient verifiable searchable encryption scheme with aggregating authorization for blockchain-enabled IoT[J]. IEEE Internet of Things Journal, 2022, 9(20): 20666–20680. doi: 10.1109/JIOT.2022.3175859. [30] 黄一才, 李森森, 郁滨. 云环境下对称可搜索加密研究综述[J]. 电子与信息学报, 2023, 45(3): 1134–1146. doi: 10.11999/JEIT211572.HUANG Yicai, LI Sensen, and YU Bin. A survey of symmetric searchable encryption in cloud environment[J]. Journal of Electronics & Information Technology, 2023, 45(3): 1134–1146. doi: 10.11999/JEIT211572. [31] WANG Jiafan and CHOW S S M. Unus pro omnibus: Multi-client searchable encryption via access control[C]. Proceedings of the 31st Annual Network and Distributed System Security Symposium, San Diego, USA, 2024: 1–18. [32] ZHU Xiaojie, ZHOU Jiancong, DAI Yueyue, et al. A verifiable and efficient symmetric searchable encryption scheme for dynamic dataset with forward and backward privacy[J]. IEEE Transactions on Dependable and Secure Computing, 2025, 22(3): 2741–2755. doi: 10.1109/TDSC.2024.3521423. [33] ZHANG Yupeng, KATZ J, and PAPAMANTHOU C. All your queries are belong to us: The power of file-injection attacks on searchable encryption[C]. Proceedings of the 25th USENIX Conference on Security Symposium, Austin, USA, 2016: 707–720. [34] QUAN Yue, FAN Kai, WANG Haoyang, et al. DMASP: Dynamic multi-keyword searchable encryption for protected access and search patterns with differential privacy[C]. Proceedings of 2024 IEEE 23rd International Conference on Trust, Security and Privacy in Computing and Communications, Sanya, China, 2024: 1423–1429. doi: 10.1109/TrustCom63139.2024.00197. [35] LIU Gang, XIAO Zheng, LI Kenli, et al. HM-ORAM: A lightweight crash-consistent ORAM framework on hybrid memory system[J]. ACM Transactions on Storage, 2025, 21(2): 16. doi: 10.1145/3715009. [36] PAPADIMITRIOU A, BHAGWAN R, CHANDRAN N, et al. Big data analytics over encrypted datasets with seabed[C]. Proceedings of the 12th USENIX Symposium on Operating Systems Design and Implementation, Savannah, USA, 2016: 587–602. [37] SAVVAS S, KHANDELWAL D, and EUGSTER P. Efficient confidentiality-preserving data analytics over symmetrically encrypted datasets[J]. Proceedings of the VLDB Endowment, 2020, 13(8): 1290–1303. doi: 10.14778/3389133.3389144. [38] STEFANOV E, VAN DIJK M, SHI E, et al. Path ORAM: An extremely simple oblivious RAM protocol[J]. Journal of the ACM (JACM), 2018, 65(4): 18. doi: 10.1145/3177872. [39] KISSNER L and SONG D. Privacy-preserving set operations[C]. Proceedings of the 25th Annual International Cryptology Conference on Advances in Cryptology, Santa Barbara, USA, 2005: 241–257. doi: 10.1007/11535218_15. [40] YANG Lei, MEI Qiaozhu, ZHENG Kai, et al. Query log analysis of an electronic health record search engine[J]. AMIA Annual Symposium Proceedings, 2011, 2011: 915–924. (查阅网上资料, 请核对文献类型及格式). -






 下载:
下载:



 下载:
下载:
