A Noise Injection Scheme Resistant to Massive MIMO Eavesdropper in IoT
-
摘要:
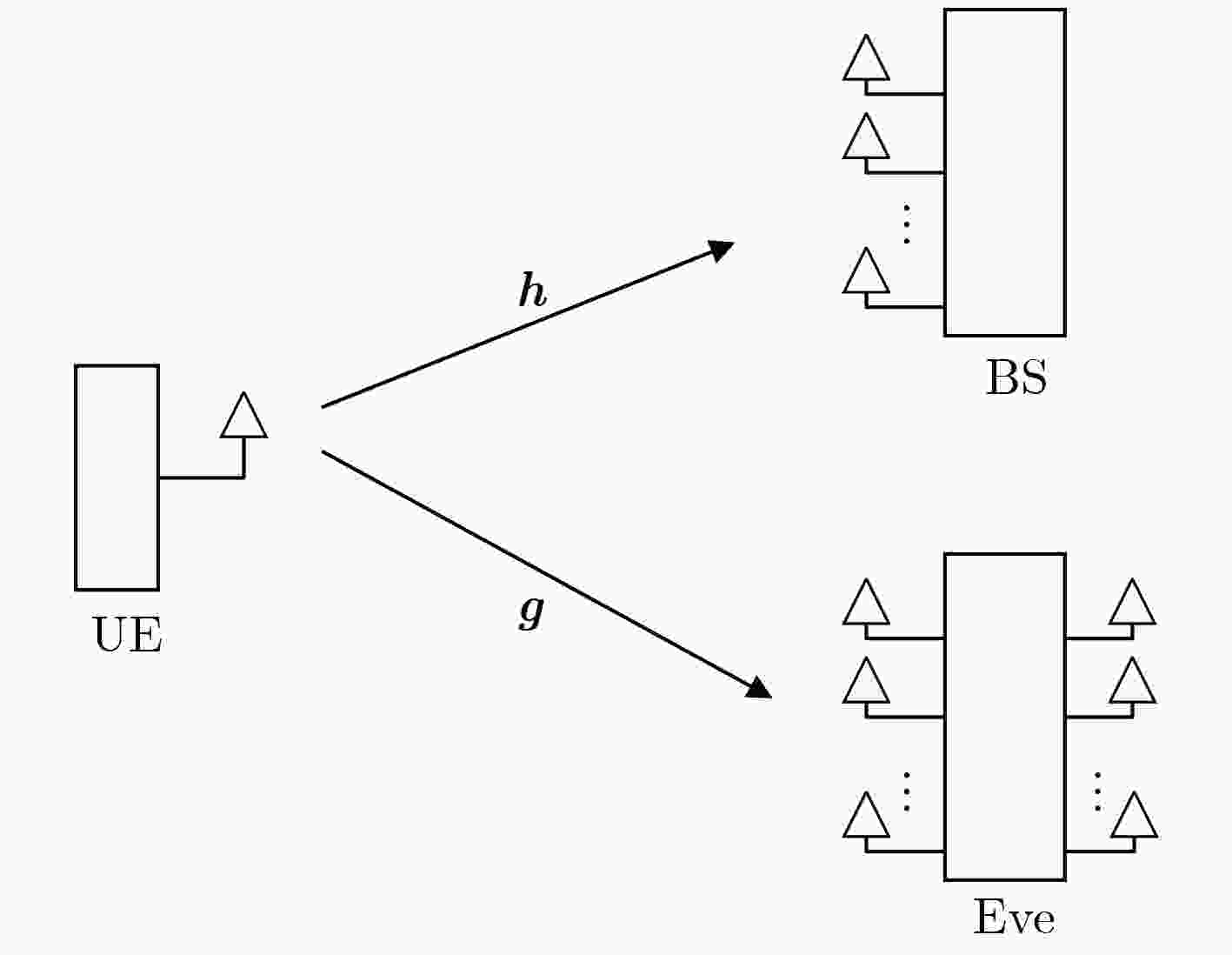
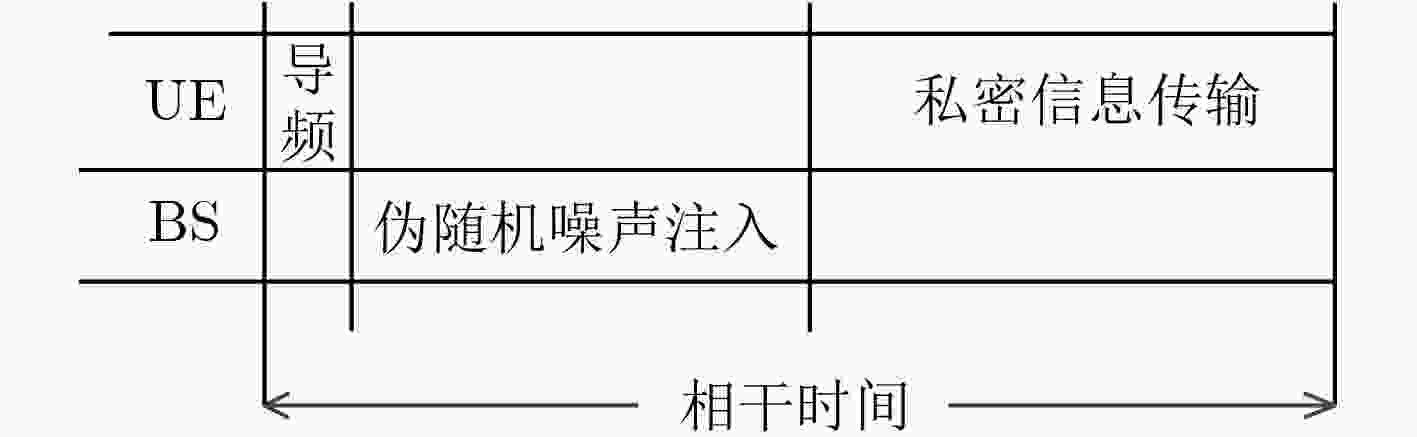
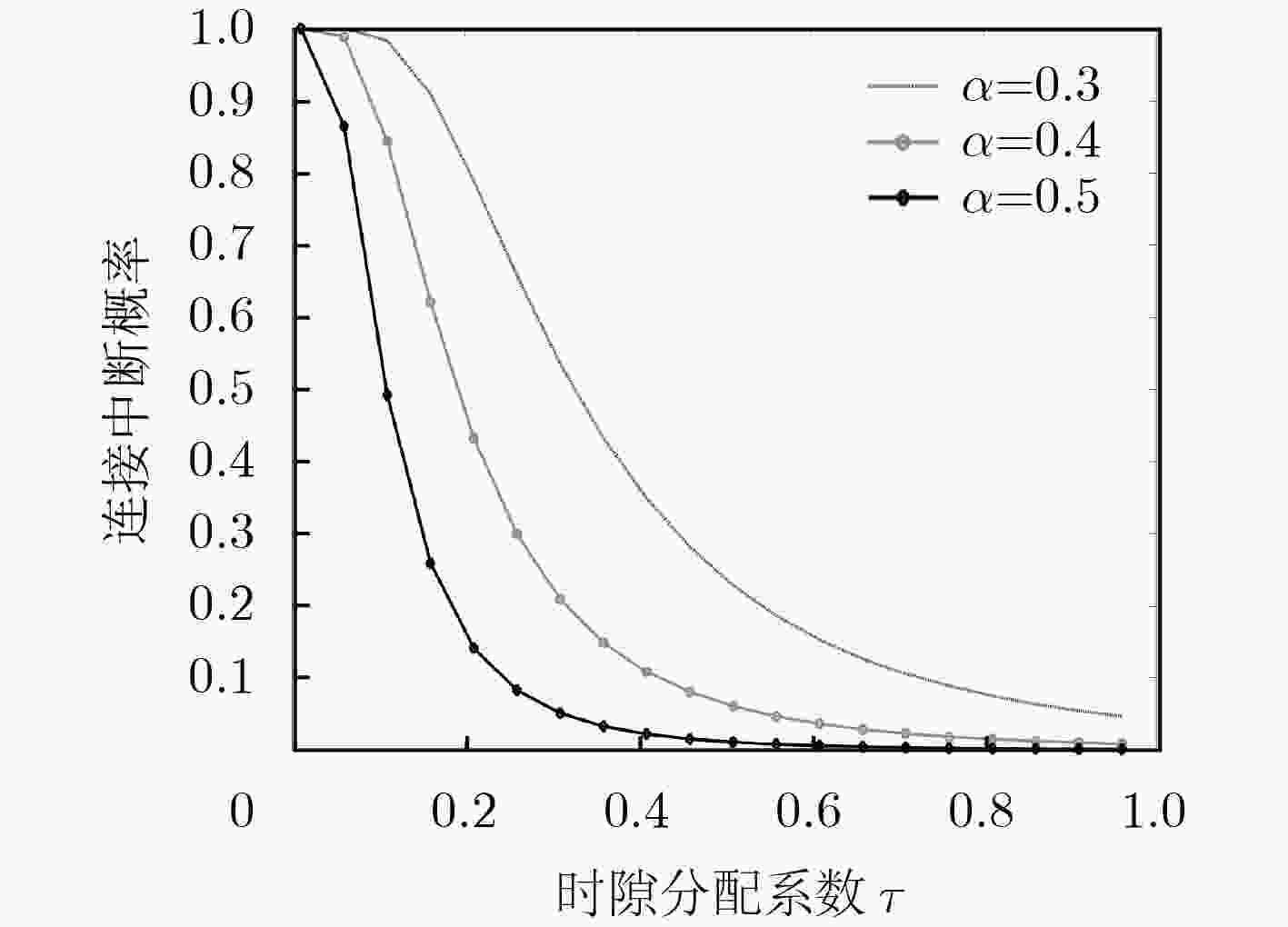
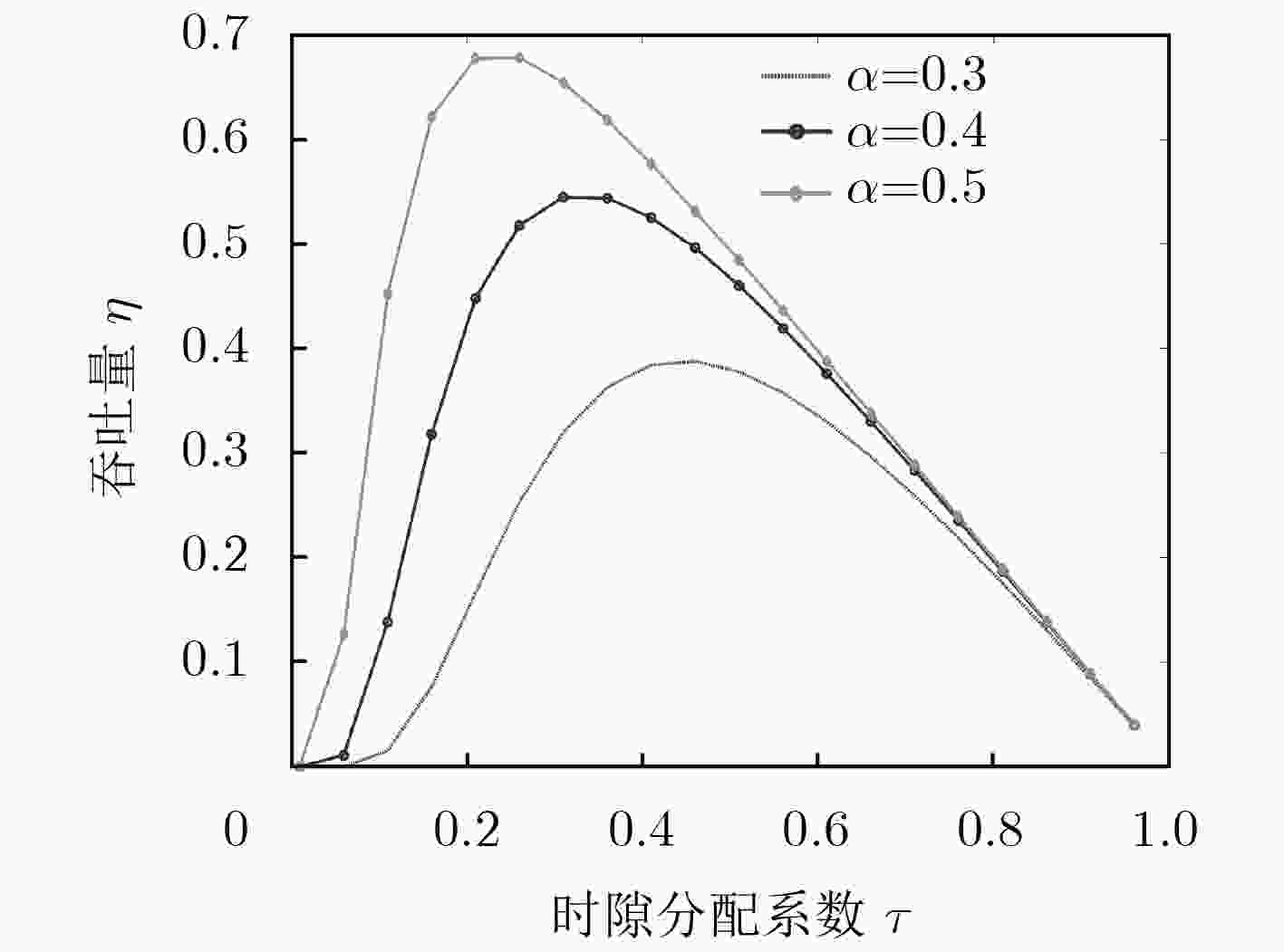
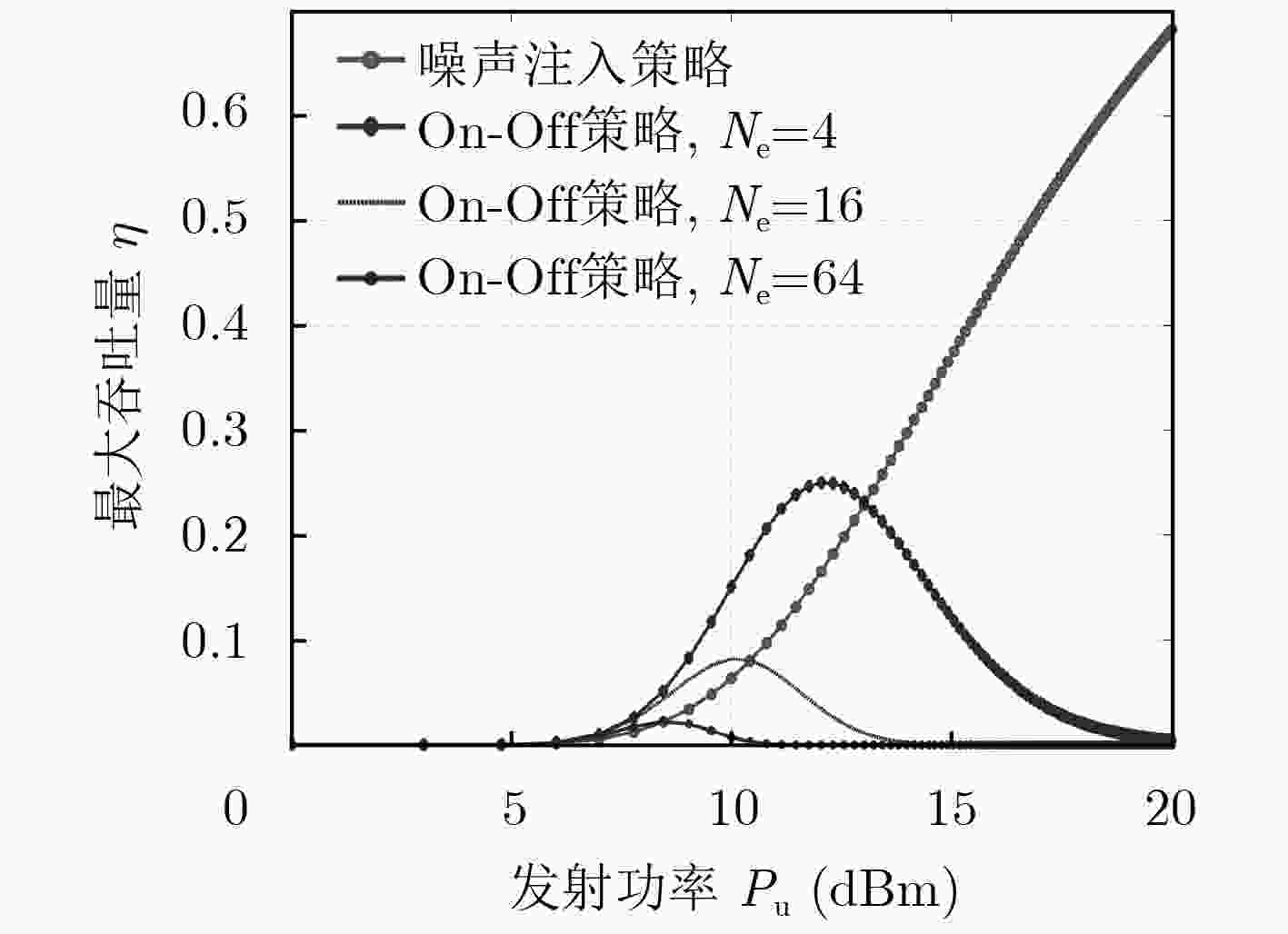
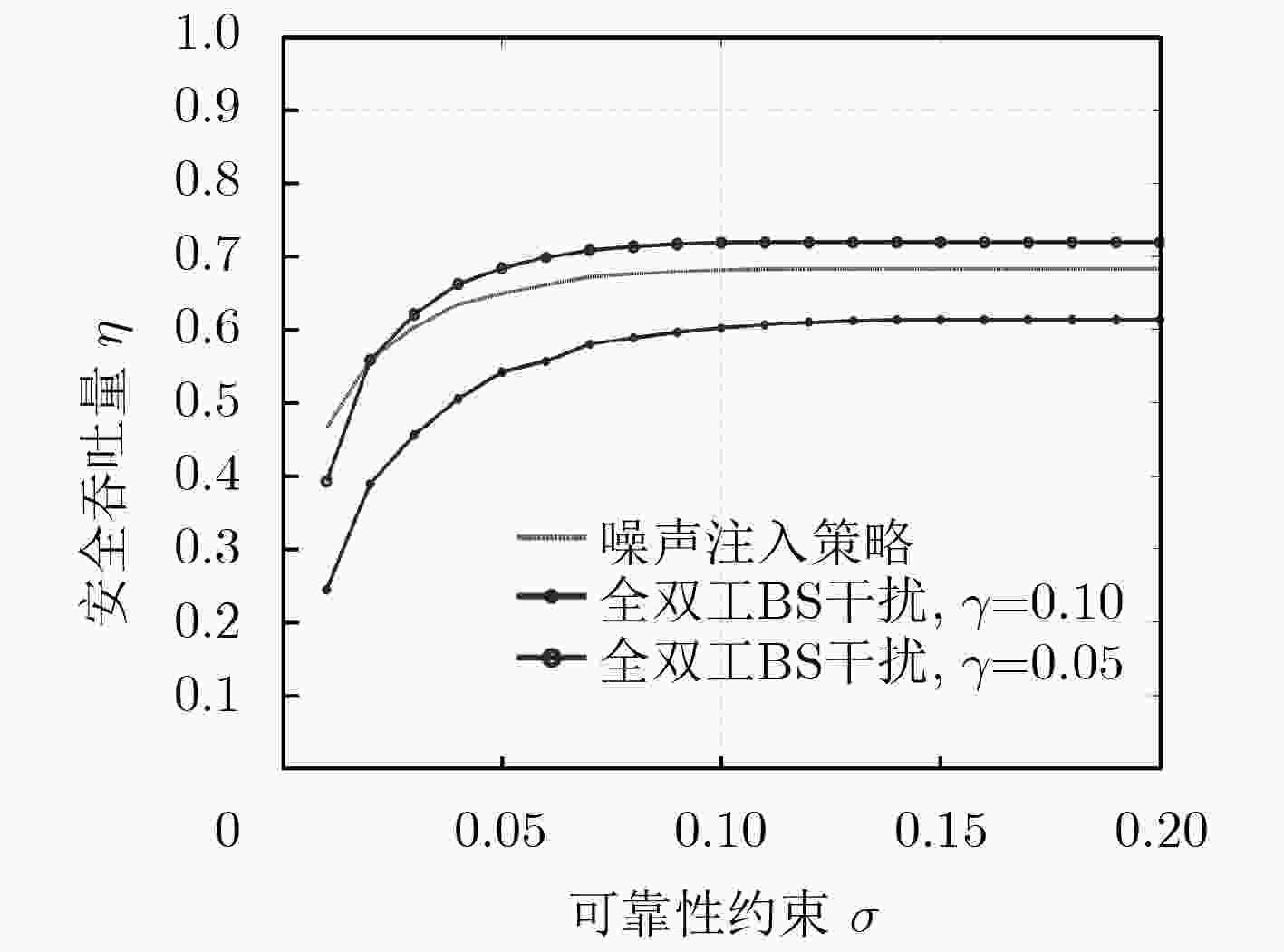
物联网中无线传输的安全难题是制约其发展的重要瓶颈,物联网终端受限的计算能力与硬件配置以及配备大规模天线阵列的窃听者给物理层安全技术带来了新的挑战。针对该问题,该文提出一种可对抗大规模天线阵列窃听者的轻量级噪声注入策略。首先,对所提出的噪声注入策略进行介绍,并分析了该策略的安全性;然后,基于该策略得到了系统吞吐量的闭式表达式,并对时隙分配系数和功率分配系数进行优化设计。理论和仿真结果表明,通过对物联网系统参数进行设计,所提出的噪声注入策略能够实现私密信息的安全传输。
Abstract:The security issue of wireless transmission becomes a significant bottleneck in the development of Internet of Things (IoT). The limited computing capability and hardware configuration of IoT terminals and eavesdroppers equipped with massive Multiple-Input Multiple-Output (MIMO) bring new challenges to physical layer security technology. To solve this problem, a lightweight noise injection scheme is proposed that can combat massive MIMO eavesdropper. Firstly, the proposed noise injection scheme is introduced, along with the corresponding secrecy analysis. Then, the close-formed expression of the throughput is derived based on the proposed scheme. Furthermore, the slot allocation coefficient and power allocation coefficient are optimized. The analytical and simulation results show that the proposed noise injection scheme can achieve the security of private information transmission by designing of the IoT system parameters.
-
Key words:
- Internet of Things (IoT) /
- Physical layer security /
- Noise injection
-
AKPAKWU G A, SILVA B J, HANCKE G P, et al. A survey on 5G networks for the internet of things: Communication technologies and challenges[J]. IEEE Access, 2017, 99(6): 3619–3647. doi: 10.1109/ACCESS.2017.2779844 MASSEY J L. An introduction to contemporary cryptology[J]. Proceedings of the IEEE, 1988, 76(5): 533–549. doi: 10.1109/5.4440 黄开枝, 张波. 异构密集网中一种抗多窃听者的协作安全波束成形方案[J]. 电子与信息学报, 2017, 39(7): 1673–1680. doi: 10.11999/JEIT161152HUANG Kaizhi and ZHANG Bo. Cooperative secrecy beamforming scheme resistant to multi-eavesdroppers in dense heterogeneous networks[J]. Journal of Electronics &Information Technology, 2017, 39(7): 1673–1680. doi: 10.11999/JEIT161152 LI Yiqing, JIANG Miao, ZHANG Qi, et al. Secure beamforming in downlink MISO non-orthogonal multiple access systems[J]. IEEE Transactions on Vehicular Technology, 2017, 66(8): 7563–7567. doi: 10.1109/TVT.2017.2658563 DENG Yansha, WANG Lifeng, YUAN Jinhong, et al. Artificial-noise aided secure transmission in large scale spectrum sharing networks[J]. IEEE Transactions on Communications, 2016, 64(5): 2116–2129. doi: 10.1109/TCOMM.2016.2544300 LIU Chenxi, YANG Nan, MALANEY R, et al. Artificial-noise-aided transmission in multi-antenna relay wiretap channels with spatially random eavesdroppers[J]. IEEE Transactions on Wireless Communications, 2016, 15(11): 7444–7456. doi: 10.1109/TWC.2016.2602337 MUKHERJEE A. Physical-layer security in the internet of things: Sensing and communication confidentiality under resource constraints[J]. Proceedings of the IEEE, 2015, 103(10): 1747–1761. doi: 10.1109/JPROC.2015.2466548 XU Qian, REN Pinyi, SONG Houbing, et al. Security enhancement for IoT communications exposed to eavesdroppers with uncertain locations[J]. IEEE Access, 2016, 4: 2840–2853. doi: 10.1109/ACCESS.2016.2575863 KIM J and CHOI J P. Cancellation-based friendly jamming for physical layer security[C]. IEEE Global Communications Conference, Washington, USA, 2016: 16655354. Al-NAHARI A. Physical layer security using massive multiple-input and multiple-output: Passive and active eavesdroppers[J]. IET Communications, 2016, 10(1): 50–56. doi: 10.1049/iet-com.2015.0216 WU Yongpeng, SCHOBER R, NG D W K, et al. Secure massive MIMO transmission with an active eavesdropper[J]. IEEE Transactions on Information Theory, 2016, 62(7): 3880–3900. doi: 10.1109/TIT.2016.2569118 WANG Chao and WANG Huiming. Robust joint beamforming and jamming for secure AF networks: Low-Complexity design[J]. IEEE Transactions on Vehicular Technology, 2015, 64(5): 2192–2198. doi: 10.1109/TVT.2014.2334640 HE Biao, SHE Yechao, and LAU V K N. Artificial noise injection for securing single-antenna systems[J]. IEEE Transactions on Vehicular Technology, 2017, 66(10): 9577–9581. doi: 10.1109/TVT.2017.2703159 黄开枝, 许耘嘉, 丁大钊, 等. 非理想情况下K层密集异构蜂窝网的安全性能分析[J]. 电子与信息学报, 2017, 39(10): 2456–2463. doi: 10.11999/JEIT161376HUANG Kaizhi, XU Yunjia, DING Dazhao, et al. Secrecy performance analysis of K-tier dense heterogeneous cellular networks with imperfect channel state information[J]. Journal of Electronics &Information Technology, 2017, 39(10): 2456–2463. doi: 10.11999/JEIT161376 ZHANG Yuanyu, SHEN Yulong, WANG Hua, et al. On secure wireless communications for IoT under eavesdropper collusion[J]. IEEE Transactions on Automation Science & Engineering, 2016, 13(3): 1281–1293. doi: 10.1109/TASE.2015.2497663 ZHOU Xiangyun, MEKAT M R, MAHAM B, et al. Rethinking the secrecy outage formulation: A secure transmission design perspective[J]. IEEE Communications Letters, 2011, 15(3): 302–304. doi: 10.1109/LCOMM.2011.011811.102433 HE Biao and ZHOU Xiangyun. Secure on-off transmission design with channel estimation errors[J]. IEEE Transactions on Information Forensics & Security, 2013, 8(12): 1923–1936. doi: 10.1109/TIFS.2013.2284754 ZHU Fengchao, GAO Feifei, YAO Minli, et al. Joint information and jamming-beamforming for physical layer security with full duplex base station[J]. IEEE Transactions on Signal Processing, 2014, 62(24): 6391–6401. doi: 10.1109/TSP.2014.2364786 -





 下载:
下载:






 下载:
下载:
