A Survey for Cloud Application Programming Interface Security: Threats and Protection
-
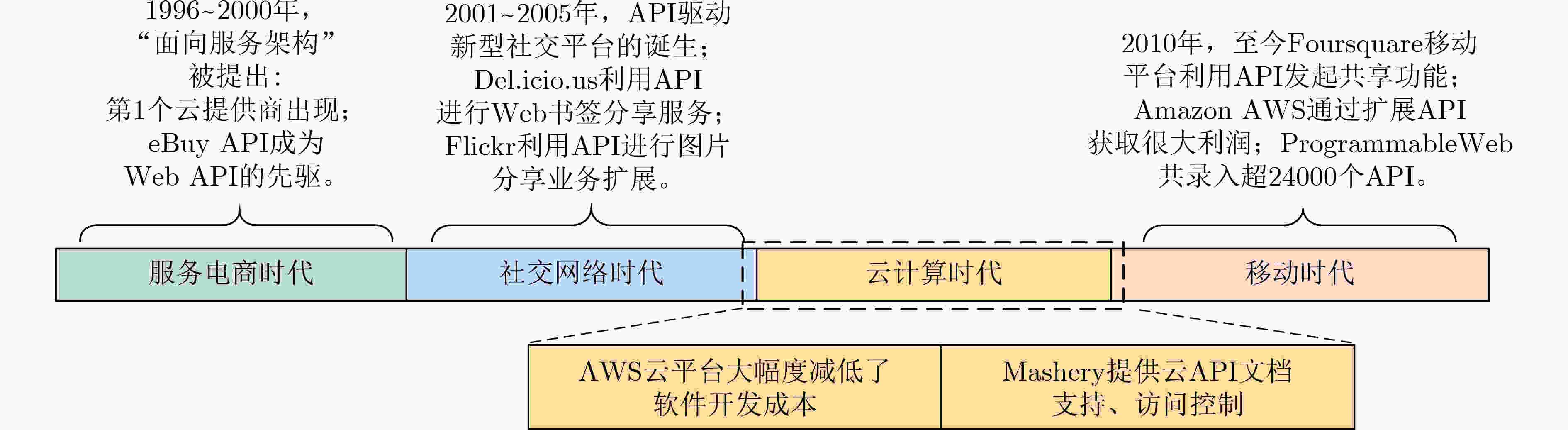
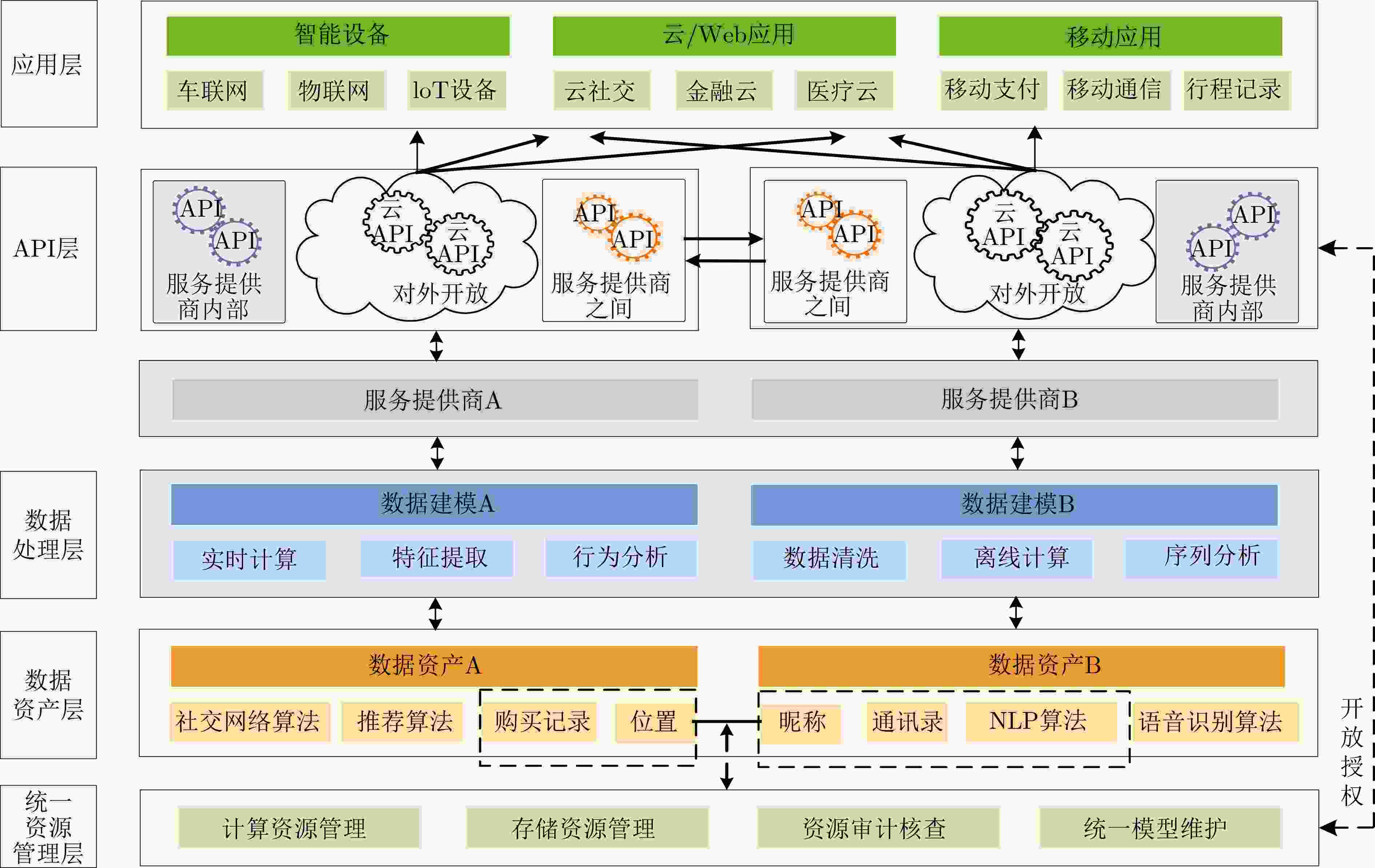
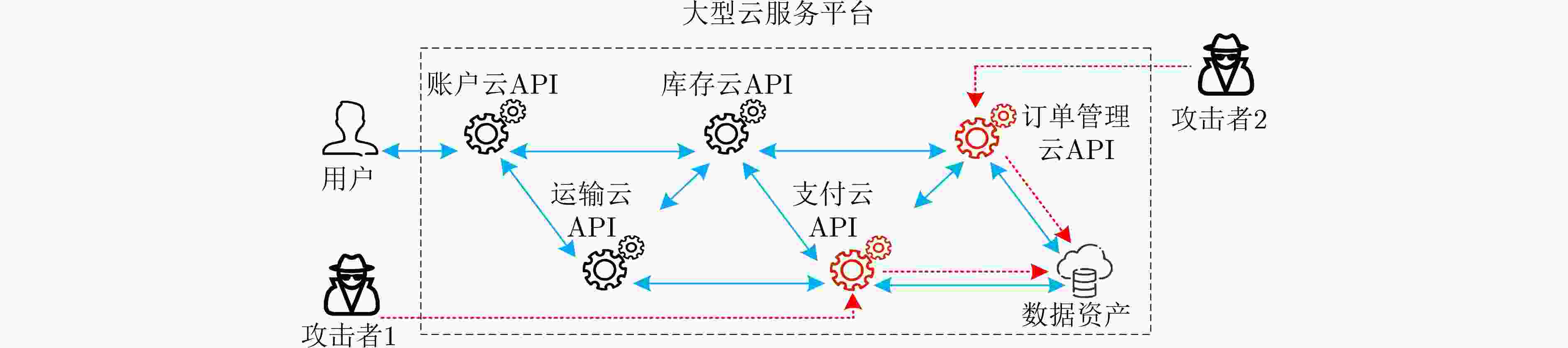
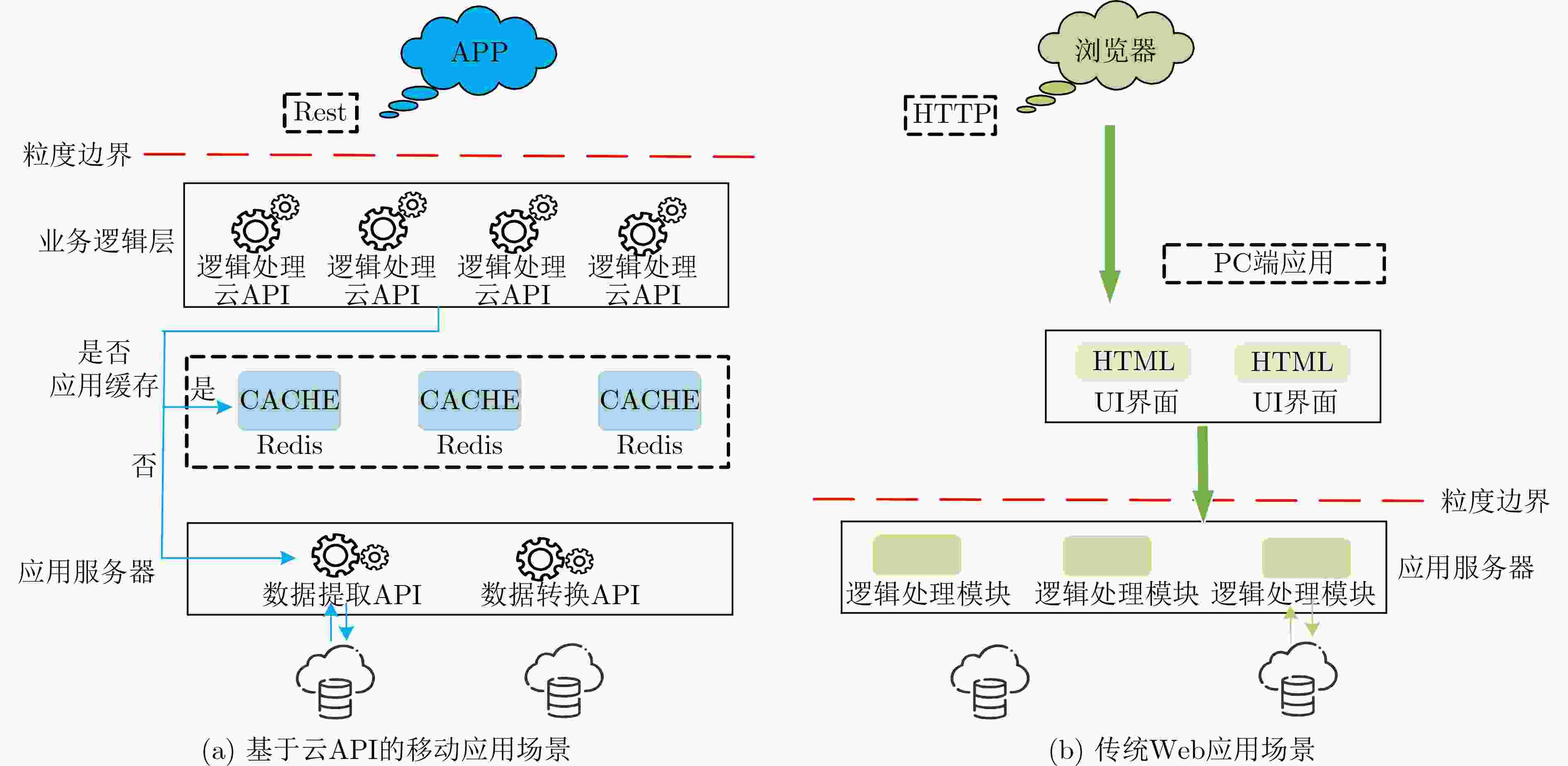
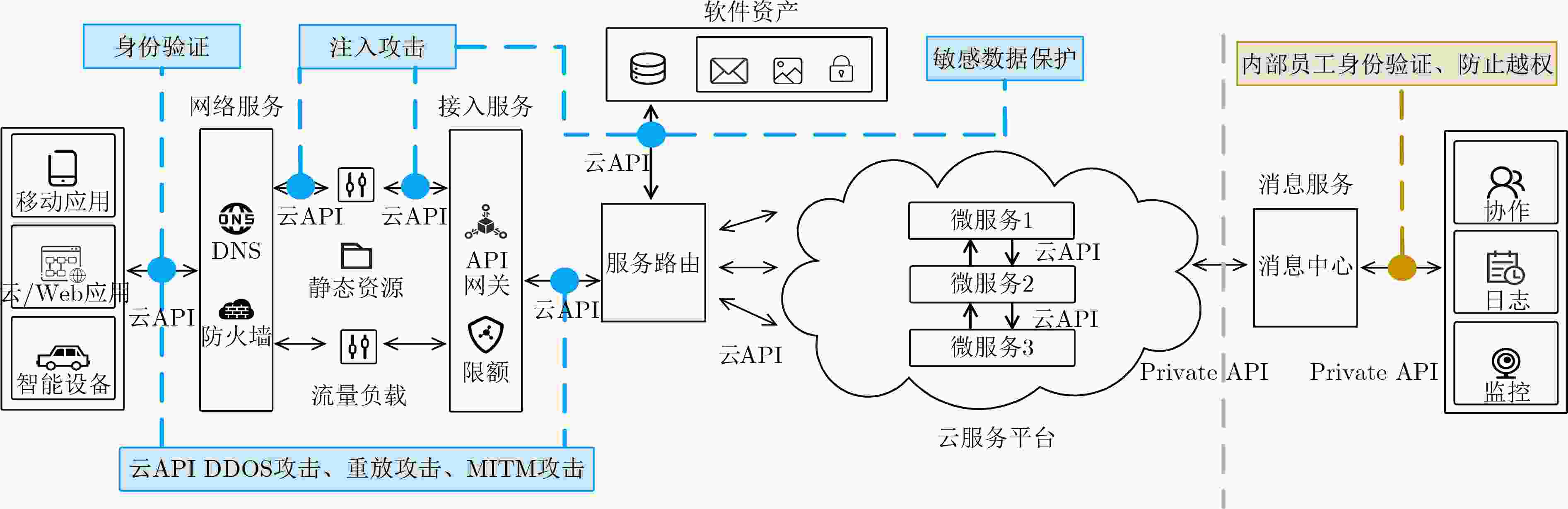
摘要: 云时代,云应用程序编程接口(API)是服务交付、能力复制和数据输出的最佳载体。然而,云API在开放服务和数据的同时,增加了暴露面和攻击面,攻击者通过数据劫持和流量分析等技术获取目标云API的关键资源,能够识别用户的身份和行为,甚至直接造成背后系统的瘫痪。当前,针对云API的攻击类型繁多,威胁与防护方法各异,缺乏对现有攻击和防护方法的系统总结。该文梳理了云API安全研究中云API面临的威胁和防护方法,分析了云API的演化历程和类别划分;讨论了云API的脆弱性以及云API安全研究的重要性;提出了云API安全研究框架,涵盖身份验证、云API分布式拒绝服务(DDoS)攻击防护、重放攻击防护、中间人(MITM)攻击防护、注入攻击防护和敏感数据防护6个方面相关研究工作综述。在此基础上,探讨了增加人工智能(AI)防护的必要性。最后给出了云API防护的未来挑战和发展趋势。Abstract: In the cloud era, cloud Application Programming Interface (API) is the best carrier for service delivery, capability replication and data output. However, cloud API increases the exposure and attack surface of cloud application while opening up services and data. Through data hijacking, traffic analysis and other technologies, attackers can obtain the key resources of the target cloud API, so as to identify the identity and behavior of users, or even directly cause the paralysis of the underlying system. Currently, there are many types of attacks against cloud APIs, and their threats and protection methods are different. However, the existing researches lack a systematic summary for cloud API attack and protection methods. In this paper, a detail survey on the threats and protection methods faced by cloud API is conducted. Firstly, the evolution and the classification of cloud API are analyzed. The vulnerability of cloud API and the importance of cloud API security research are then discussed. Furthermore, a systematical cloud API security research framework is proposed, which covers six aspects: identity authentication, cloud API Distributed Denial of Service (DDoS) attack protection, replay attack protection, Man-In-The-Middle (MITM) attack protection, injection attack protection and sensitive data protection. In addition, the necessity of Artificial Intelligence (AI) protection for cloud API is discussed. Finally, the future challenges and development trends of cloud API protection are presented.
-
表 1 基于应用范围分类的云API特点比较
API类别 部署方式 应用范围 访问机制 延展性 安全性能 Private API VPC网络 服务提供商内部 有效 一般 高 Partner API VPC网络/公共互联网 服务提供商之间 有效 好 一般 Public API 公共互联网 任何用户 不足 好 低、易受攻击 表 2 抗重放方案比较
表 3 MITM防护方案比较
MITM防护方案 攻击目标类型 攻击场景 模型/方法 防护机制 Bruschi等人[33] ARP缓存中毒 封闭 S-ARP 可信主机分发密钥 Limmaneewichid等人[38] 目标IP替换 封闭 P-ARP 哈希函数隐藏IP地址 Lootah等人[34] ARP缓存中毒 封闭 T-ARP 集中发行票据认证 Trabelsi等人[35] ARP请求应答超时 封闭 有状态ARP应答 添加“等待”条目 Ataullah等人[39] ARP无状态性攻击 封闭 ES-ARP 广播ARP请求和应答 Ariyapperuma等人[40] 数据真实性受损 开放 DNSSEC 哈希函数加密数字签名 Kales等人[36] 恶意证书干扰 开放 伪造证书检验 补充中央审计日志 Soghoian等人[37] 恶意证书替换 开放 证书锁定 证书中的公钥提前内置 表 4 两类防护方案对比
攻击类别 传统云API安全 AI驱动云API安全 身份验证 令牌、密钥 历史信息自学习 云API DDoS攻击 负载均衡、速率限制 流量数据计算、源验证 重放攻击 抗重放因子 暂无 MITM攻击 传输介质检验 暂无 注入攻击 参数化查询、正则化检验 暂无 敏感数据保护 加密(SSL, TLS) 敏感数据学习、提取 -
[1] 艾瑞咨询有限公司. 2020年中国人工智能API经济白皮书[R]. 艾瑞咨询系列研究报告, 2020.IResearch Consulting Croup. White paper on API economy of China's artificial intelligence[R]. IResearch Consulting Series Research Reports, 2020. [2] TAN Wei, FAN Yushun, GHONEIM A, et al. From the service-oriented architecture to the Web API economy[J]. IEEE Internet Computing, 2016, 20(4): 64–68. doi: 10.1109/MIC.2016.74 [3] ESPINHA T, ZAIDMAN A, and GROSS H G. Web API growing pains: Loosely coupled yet strongly tied[J]. Journal of Systems and Software, 2015, 100: 27–43. doi: 10.1016/j.jss.2014.10.014 [4] BOUGUETTAYA A, SINGH M, HUHNS M, et al. A service computing manifesto: The next 10 years[J]. Communications of the ACM, 2017, 60(4): 64–72. doi: 10.1145/2983528 [5] HUSSAIN F, HUSSAIN R, NOYE B, et al. Enterprise API security and GDPR compliance: Design and implementation perspective[J]. IT Professional, 2020, 22(5): 81–89. doi: 10.1109/MITP.2020.2973852 [6] ARCURI A, FRASER G, and JUST R. Private API access and functional mocking in automated unit test generation[C]. 2017 IEEE International Conference on Software Testing, Verification and Validation, Tokyo, Japan, 2017: 126–137. [7] OWASP. OWASP top ten 2017[EB/OL]. https://www.owasp.org/index.php/Top_10-2017_Top_10, 2017. [8] BOZKURT M, HARMAN M, and HASSOUN Y. Testing Web services: A survey[R]. Technical Reports TR-10-01, 2010. [9] ESPINHA T, ZAIDMAN A, and GROSS H G. Web API fragility: How robust is your mobile application?[C]. The 2nd ACM International Conference on Mobile Software Engineering and Systems, Florence, Italy, 2015: 12–21. [10] 刘奇旭, 邱凯丽, 王乙文, 等. 面向OAuth2.0授权服务API的账号劫持攻击威胁检测[J]. 通信学报, 2019, 40(6): 40–50. doi: 10.11959/j.issn.1000-436x.2019144LIU Qixu, QIU Kaili, WANG Yiwen, et al. Account hijacking threat attack detection for OAuth2.0 authorization API[J]. Journal on Communications, 2019, 40(6): 40–50. doi: 10.11959/j.issn.1000-436x.2019144 [11] DIG D and JOHNSON R. How do APIs evolve? A story of refactoring[J]. Journal of Software Maintenance and Evolution:Research and Practice, 2006, 18(2): 83–107. doi: 10.1002/smr.328 [12] SETIADI D R I M, NAJIB A F, RACHMAWANTO E H, et al. A comparative study MD5 and SHA1 algorithms to encrypt REST API authentication on mobile-based application[C]. 2019 International Conference on Information and Communications Technology, Yogyakarta, Indonesia, 2019: 206–211. [13] SKLAVOS N and KOUFOPAVLOU O. Implementation of the SHA-2 hash family standard using FPGAs[J]. The Journal of Supercomputing, 2005, 31(3): 227–248. doi: 10.1007/s11227-005-0086-5 [14] GORSKI P L, ACAR Y, IACONO L L, et al. Listen to developers! A participatory design study on security warnings for cryptographic APIs[C]. The 2020 CHI Conference on Human Factors in Computing Systems, Honolulu, USA, 2020: 1–13. [15] Angular University. JWT: The complete guide to JSON web tokens[EB/OL]. https://blog.angular-university.io/angular-jwt/, 2022. [16] KARUNANITHI M D and KIRUTHIKA B. Single sign-on and single log out in identity[C]. The International Conference on Nanoscience, Engineering and Technology, Chennai, India, 2011: 607–611. [17] FUJII H and TSURUOKA Y. SV-2FA: Two-factor user authentication with SMS and voiceprint challenge response[C]. The 8th International Conference for Internet Technology and Secured Transactions, London, UK, 2013: 283–287. [18] VAN OORSCHOT P C. Computer Security and the Internet: Tools and Jewels[M]. Cham: Springer, 2020: 1–25. [19] NOKOVIC B, DJOSIC N, and LI W O. API security risk assessment based on dynamic ML models[C]. The 14th International Conference on Innovations in Information Technology, Al Ain, United Arab Emirates, 2020: 247–252. [20] BERA P, SAHA A, and SETUA S K. Denial of service attack in software defined network[C]. The 5th International Conference on Computer Science and Network Technology, Changchun, China, 2016: 497–501. [21] DE B. API Management[M]. Berkeley: Apress, 2017: 15–28. [22] IMPERVA. Bot defense for API security data sheet[EB/OL]. https://resources.distilnetworks.com/data-sheets/bot-defense-for-apis, 2018. [23] NETACEA. Bot detection and mitigation with machine learning[EB/OL]. https://www.netacea.com/bot-detection, 2018. [24] HARGUINDEGUY B. Artificial intelligence and machine learning: A new approach to API security[EB/OL]. https://www.pingidentity.com/en/company/blog/posts/2018/artificial-intelligence-machine-learning-a-new-approach-to-api-Security.html, 2018. [25] ZHU Minghui and MARTÍNEZ S. On the performance analysis of resilient networked control systems under replay attacks[J]. IEEE Transactions on Automatic Control, 2014, 59(3): 804–808. doi: 10.1109/TAC.2013.2279896 [26] GRUSCHKA N and LUTTENBERGER N. Protecting web services from DoS attacks by SOAP message validation[C]. The IFIP TC-11 21st International Information Security Conference, Karlstad, Sweden, 2006: 171–182. [27] JENSEN M, GRUSCHKA N, and HERKENHöNER R. A survey of attacks on web services[J]. Computer Science-Research and Development, 2009, 24(4): 185–197. doi: 10.1007/s00450-009-0092-6 [28] DE RYCK P, DESMET L, PIESSENS F, et al. Primer on client-side web security[M]. Cham: Springer, 2014: 105–109. [29] 肖斌斌, 徐雨明. 基于双重验证的抗重放攻击方案[J]. 计算机工程, 2017, 43(5): 115–120,128. doi: 10.3969/j.issn.1000-3428.2017.05.019XIAO Binbin and XU Yuming. Scheme of anti-replay attacks based on two-factor authentication[J]. Computer Engineering, 2017, 43(5): 115–120,128. doi: 10.3969/j.issn.1000-3428.2017.05.019 [30] 王育红, 夏安祥, 林国庆, 等. 抗重放攻击方案在工程中的应用[J]. 网络安全技术与应用, 2021(4): 8–10. doi: 10.3969/j.issn.1009-6833.2021.04.006WANG Yuhong, XIA Anxiang, LIN Guoqing, et al. Application of anti-replay attack scheme in engineering[J]. Network Security Technology &Application, 2021(4): 8–10. doi: 10.3969/j.issn.1009-6833.2021.04.006 [31] CONTI M, DRAGONI N, and LESYK V. A survey of man in the middle attacks[J]. IEEE Communications Surveys & Tutorials, 2016, 18(3): 2027–2051. doi: 10.1109/COMST.2016.2548426 [32] NAQASH T, UBAID F B, ISHFAQ A, et al. Protecting DNS from cache poisoning attack by using secure proxy[C]. 2012 International Conference on Emerging Technologies, Islamabad, Pakistan, 2012: 1–5. [33] BRUSCHI D, ORNAGHI A, and ROSTI E. S-ARP: A secure address resolution protocol[C]. The 19th Annual Computer Security Applications Conference, Las Vegas, USA, 2003: 66–74. [34] LOOTAH W, ENCK W, and MCDANIEL P. TARP: Ticket-based address resolution protocol[J]. Computer Networks, 2007, 51(15): 4322–4337. doi: 10.1016/j.comnet.2007.05.007 [35] TRABELSI Z and EL-HAJJ W. Preventing ARP attacks using a fuzzy-based stateful ARP cache[C]. 2007 IEEE International Conference on Communications, Glasgow, UK, 2007: 1355–1360. [36] KALES D, OMOLOLA O, and RAMACHER S. Revisiting user privacy for certificate transparency[C]. 2019 IEEE European Symposium on Security and Privacy, Stockholm, Sweden, 2019. [37] SOGHOIAN C and STAMM S. Certified lies: Detecting and defeating government interception attacks against SSL (short paper)[C]. The 15th International Conference on Financial Cryptography and Data Security, Gros Islet, St. Lucia, 2011: 250–259. [38] LIMMANEEWICHID P and LILAKIATSAKUN W. P-ARP: A novel enhanced authentication scheme for securing ARP[C]. The 2011 International Conference on Telecommunication Technology and Applications, Singapore, Singapore, 2011: 83–87. [39] ATAULLAH M and CHAUHAN N. ES-ARP: An efficient and secure address resolution protocol[C]. 2012 IEEE Students' Conference on Electrical, Electronics and Computer Science, Bhopal, India, 2012: 1–5. [40] ARIYAPPERUMA S and MITCHELL C J. Security vulnerabilities in DNS and DNSSEC[C]. The 2rd International Conference on Availability, Reliability and Security, Vienna, Austria, 2007: 335–342. [41] KINGTHORIN. OWASP SQL injection[EB/OL]. https://owasp.org/www-community/attacks/SQL_Injection#, 2021. [42] ZHONG Weilin and REZOS. Code injection software attack[EB/OL]. https://owasp.org/www-community/attacks/Code_Injection, 2021. [43] RAJARAM A K, BABU B C, and KUMAR R C K. API based security solutions for communication among web services[C]. The 15th International Conference on Advanced Computing, Chennai, India, 2013: 571–575. [44] YANG Dawei, GAO Yang, HE Wei, et al. Design and achievement of security mechanism of API gateway platform based on microservice architecture[J]. Journal of Physics:Conference Series, 2021, 1738: 012046. doi: 10.1088/1742-6596/1738/1/012046 [45] ATLIDAKIS V, GODEFROID P, and POLISHCHUK M. Checking security properties of cloud service REST APIs[C]. The 13th International Conference on Software Testing, Validation and Verification, Porto, Portugal, 2020: 387–397. [46] MENG Shanshan, YANG Xiaohui, SONG Yubo, et al. Android’s sensitive data leakage detection based on API monitoring[C]. The International Conference on Cyberspace Technology, Beijing, China, 2014: 1–4. [47] PANETTA K. Gartner top 10 strategic technology for 2020[EB/OL]. https://www.gartner.com, 2020. [48] GRENT H, AKIMOV A, and ANICHE M. Automatically identifying parameter constraints in complex Web APIs: A case study at Adyen[C]. The IEEE/ACM 43rd International Conference on Software Engineering: Software Engineering in Practice, Madrid, ES, 2021: 71–80. [49] KROMKOWSKI P, LI Shaoran, ZHAO Wenxi, et al. Evaluating statistical models for network traffic anomaly detection[C]. 2019 Systems and Information Engineering Design Symposium, Charlottesville, USA, 2019: 1–6. [50] BAYE G, HUSSAIN F, ORACEVIC A, et al. API security in large enterprises: Leveraging machine learning for anomaly detection[C]. 2021 International Symposium on Networks, Computers and Communications, Dubai, United Arab Emirates, 2021: 1–6. [51] SHI Yi, SAGDUYU Y E, DAVASLIOGLU K, et al. Active deep learning attacks under strict rate limitations for online API calls[C]. 2018 IEEE International Symposium on Technologies for Homeland Security, Woburn, USA, 2018: 1–6. -





 下载:
下载:


 下载:
下载:
