|
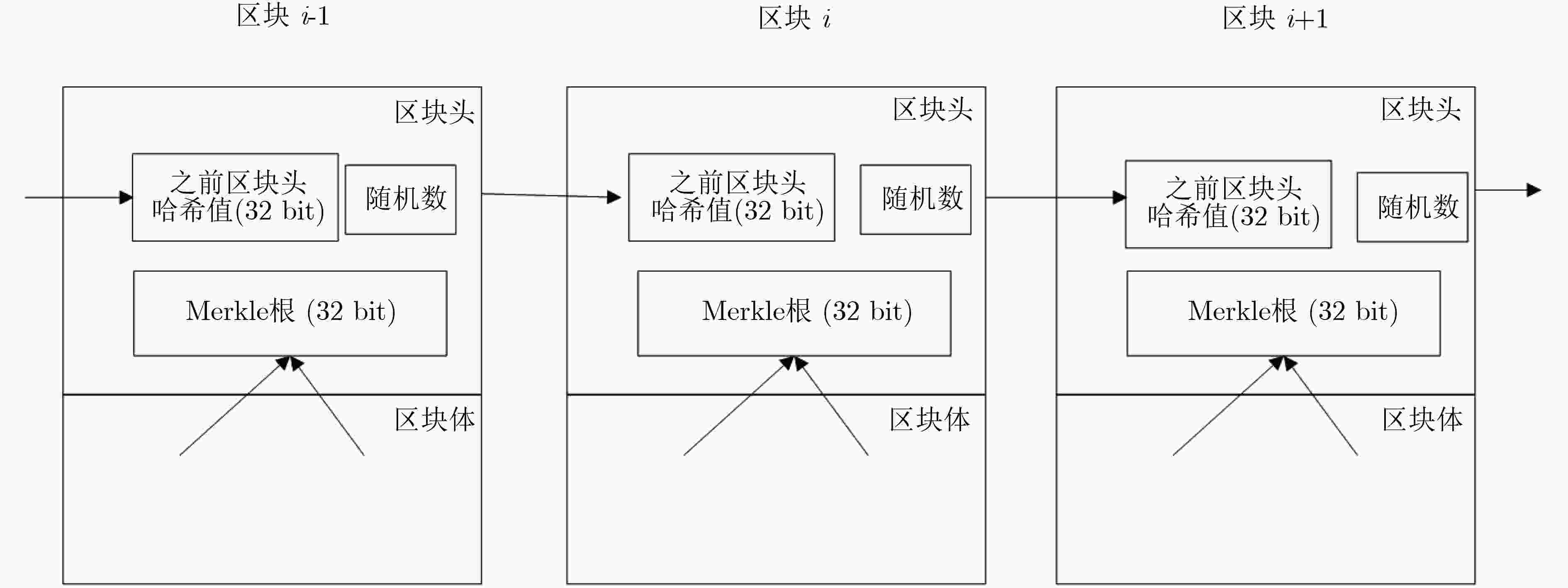
NAKAMOTO S. Bitcoin: A peer-to-peer electronic cash system[EB/OL]. https://bitcoin.org/bitcoin.pdf, 2008.
|
|
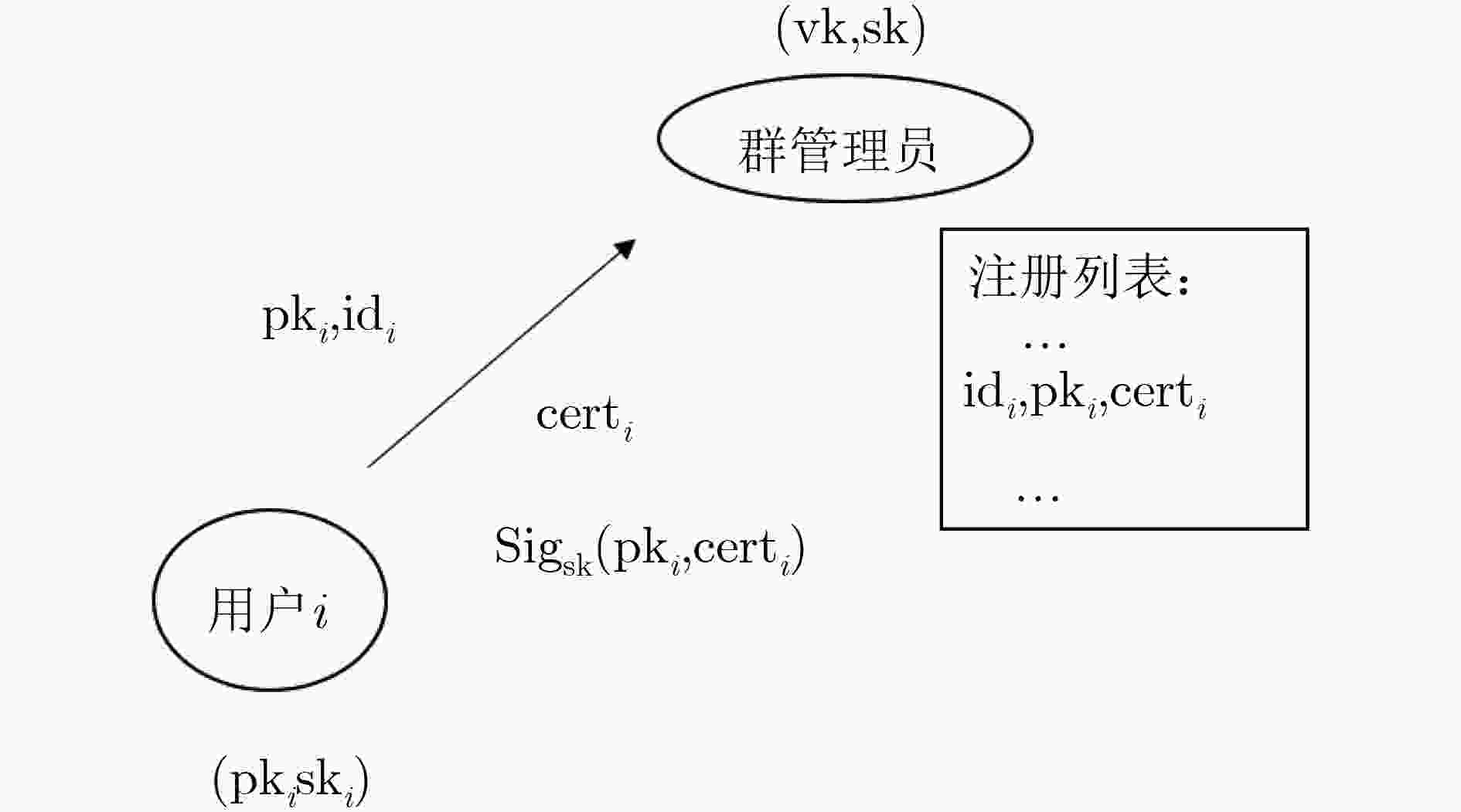
曹素珍, 王斐, 郎晓丽, 等. 基于无证书的多方合同签署协议[J]. 电子与信息学报, 2019, 41(11): 2691–2698. doi: 10.11999/JEIT190166CAO Suzhen, WANG Fei, LANG Xiaoli, et al. Multi-party contract signing protocol based on certificateless[J]. Journal of Electronics &Information Technology, 2019, 41(11): 2691–2698. doi: 10.11999/JEIT190166
|
|
NARAYANAN A, BONNEAU J, FELTEN E, et al. Bitcoin and Cryptocurrency Technologies: A Comprehensive Introduction[M]. Princeton University Press, 2016.
|
|
牛淑芬, 王金风, 王伯彬, 等. 区块链上基于B+树索引结构的密文排序搜索方案[J]. 电子与信息学报, 2019, 41(10): 2409–2415. doi: 10.11999/JEIT190038NIU Shufen, WANG Jinfeng, WANG Bobin, et al. Ciphertext sorting search scheme based on b+ tree index structure on blockchain[J]. Journal of Electronics &Information Technology, 2019, 41(10): 2409–2415. doi: 10.11999/JEIT190038
|
|
邹均, 张海宁, 唐屹, 等. 区块链技术指南[M]. 北京: 机械工业出版社, 2016: 97–99.ZOU Jun, ZHANG Haining, TANG Yi, et al. Guidelines for Blockchain Technology[M]. Beijing: China Machine Press, 2016: 97–99.
|
|
CHAUM D, FIAT A, and NAOR M. Untraceable Electronic Cash[M]. GOLDWASSER S. Advances in Cryptology — CRYPTO’ 88. New York: Springer, 1990: 319–327. doi: 10.1007/0-387-34799-2_25.
|
|
CHAUM D and VAN HEYST E. Group Signatures[M]. DAVIES D W. Advances in Cryptology — EUROCRYPT ’91. Berlin: Springer, 1991: 257–265. doi: 10.1007/3-540-46416-6_22.
|
|
GROTH J and SAHAI A. Efficient non-interactive proof systems for bilinear groups[C]. The 27th Annual International Conference on the Theory and Applications of Cryptographic Techniques, Istanbul, Turkey, 2008: 415–432. doi: 10.1007/978-3-540-78967-3_24.
|
|
CHAUM D L. Untraceable electronic mail, return addresses, and digital pseudonyms[J]. Communications of the ACM, 1981, 24(2): 84–90. doi: 10.1145/358549.358563
|
|
BONNEAU J, NARAYANAN A, MILLER A, et al. Mixcoin: Anonymity for Bitcoin with Accountable Mixes[M]. CHRISTIN N and SAFAVI-NAINI R. Financial Cryptography and Data Security. Berlin: Springer, 2014: 486–504. doi: 10.1007/978-3-662-45472-5_31.
|
|
VALENTA L and ROWAN B. BLIndcoin: Blinded, accountable mixes for bitcoin[C]. 2015 International Conference on Financial Cryptography and Data Security, San Juan, USA, 2015: 112–126. doi: 10.1007/978-3-662-48051-9_9.
|
|
MAXWELL G. Coinjoin: Bitcoin privacy for the real world[EB/OL]. Post on Bitcoin Forum. https://bitcointalk.org/index.php?topic=279249.0, 2013.
|
|
RUFFING T, MORENO-SANCHEZ P, and KATE A. CoinShuffle: Practical decentralized coin mixing for bitcoin[C]. The 19th European Symposium on Research in Computer Security, Wroclaw, Poland, 2014: 345–364. doi: 10.1007/978-3-319-11212-1_20.
|
|
RUFFING T, MORENO-SANCHEZ P, and KATE A. P2P mixing and unlinkable bitcoin transactions[C]. The 24th Annual Network and Distributed System Security Symposium, San Diego, USA, 2017: 824.
|
|
RUFFING T and MORENO-SANCHEZ P. Valueshuffle: Mixing confidential transactions for comprehensive transaction privacy in bitcoin[C]. 2017 International Conference on Financial Cryptography and Data Security, Sliema, Malta, 2017: 133–154.
|
|
CHANDRAN N, GROTH J, and SAHAI A. Ring signatures of sub-linear size without random oracles[C]. The 34th International Colloquium on Automata, Languages, and Programming, Wrocław, Poland, 2007: 423–434.
|
|
BERGAN T, ANDERSON O, DEVIETTI J, et al. CryptoNote v 2.0[J]. https://cryptonote.org/whitepaper.pdf, 2013.
|
|
LIU J K, WEI V K, and WONG D S. Linkable spontaneous anonymous group signature for ad hoc groups[C]. The 9th Australasian Conference on Information Security and Privacy, Sydney, Australia, 2004: 325–335. doi: 10.1007/978-3-540-27800-9_28.
|
|
MIERS I, GARMAN C, GREEN M, et al. Zerocoin: Anonymous distributed e-cash from bitcoin[C]. 2013 IEEE Symposium on Security and Privacy, Berkeley, USA, 2013: 397–411.
|
|
BEN SASSON E, CHIESA A, GARMAN C, et al. Zerocash: Decentralized anonymous payments from bitcoin[C]. 2014 IEEE Symposium on Security and Privacy, San Jose, USA, 2014: 459–474.
|
|
BEN-SASSON E, CHIESA A, TROMER E, et al. Succinct non-interactive zero knowledge for a von Neumann architecture[C]. The 23rd USENIX Conference on Security Symposium, Berkeley, USA, 2014: 781–796.
|
|
PEDERSEN T P. Non-interactive and information-theoretic Secure Verifiable Secret Sharing[M]. FEIGENBAUM J. Annual International Cryptology— CRYPTO ’91. Berlin: Springer, 1991: 129–140. doi: 10.1007/3-540-46766-1_9.
|
|
FUJISAKI E and SUZUKI K. Traceable ring signature[C]. The 10th International Conference on Practice and Theory in Public-Key Cryptography, Beijing, China, 2007: 181–200. doi: 10.1007/978-3-540-71677-8_13.
|
|
GROTH J. Fully anonymous group signatures without random oracles[C]. The 13th International Conference on the Theory and Application of Cryptology and Information Security, Kuching, Malaysia, 2007: 164–180. doi: 10.1007/978-3-540-76900-2_10.
|
|
ZHOU Sujing and LIN Dongdai. Shorter Verifier-local Revocation Group Signatures from Bilinear Maps[M]. POINTCHEVAL D, MU Yi, and CHEN Kefei. Cryptology and Network Security. Berlin: Springer, 2006: 126–143. doi: 10.1007/11935070_8.
|
|
BONEH D and BOYEN X. Short Signatures without Random Oracles[M]. CACHIN C and CAMENISCH J L. Advances in Cryptology - EUROCRYPT 2004. Berlin: Springer, 2004: 56–73. doi: 10.1007/978-3-540-24676-3_4.
|





 下载:
下载:


 下载:
下载:
