Fast-flux Botnet Detection Method Based on Spatiotemporal Feature of Network Traffic
-
摘要:
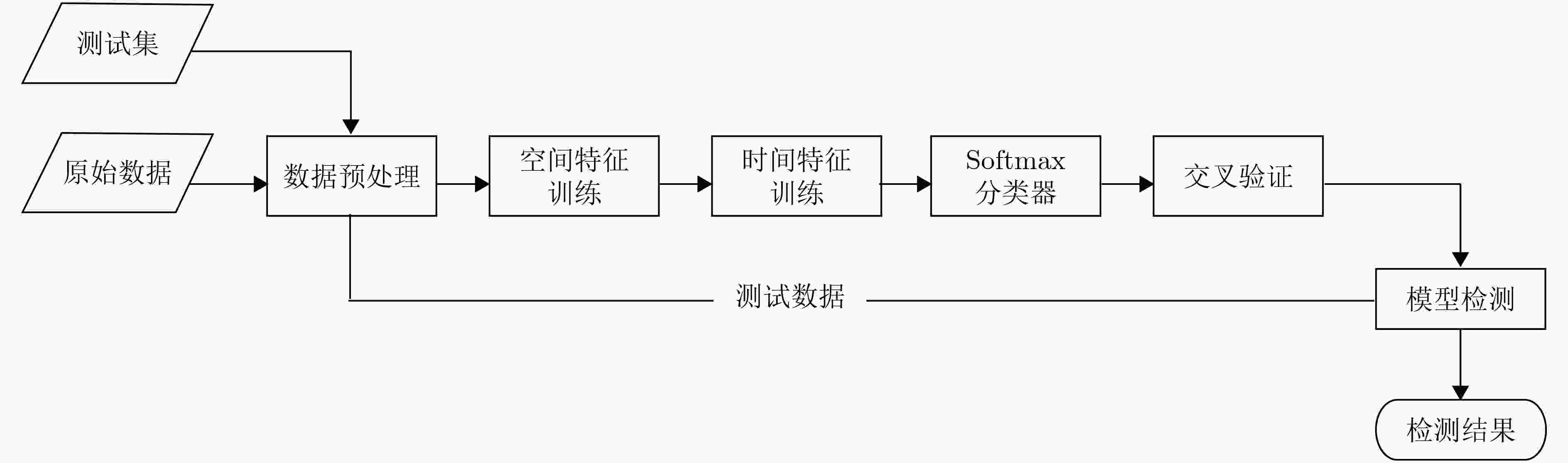
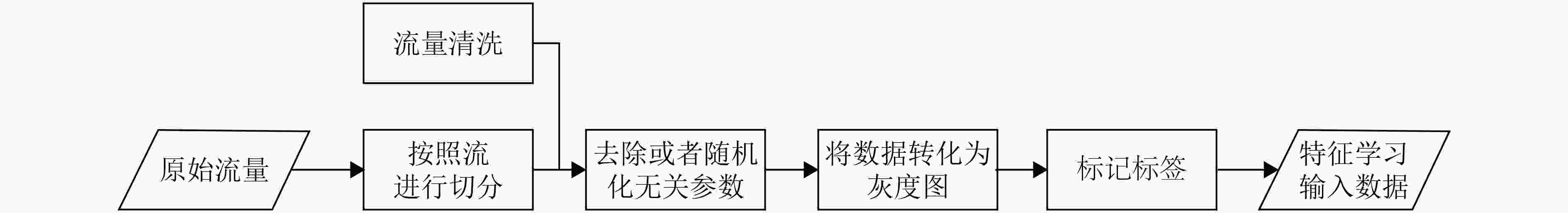
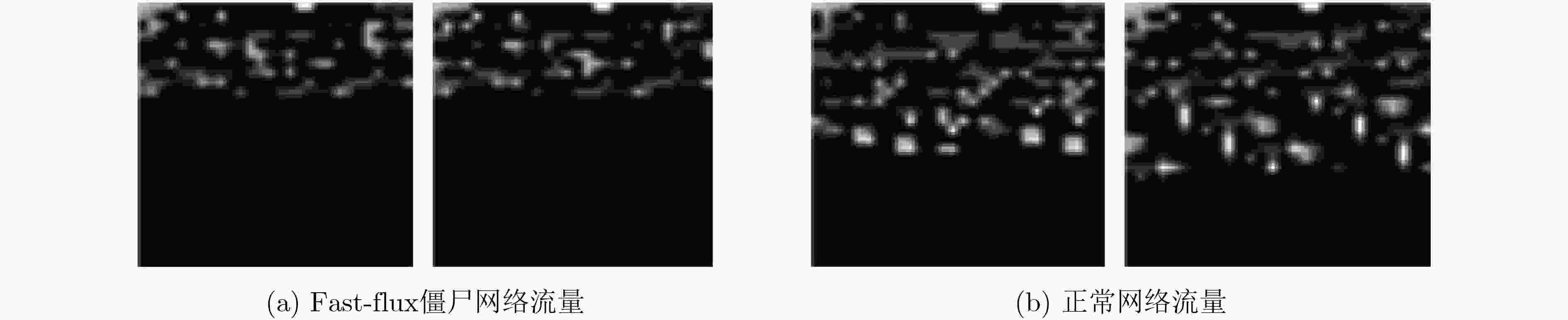
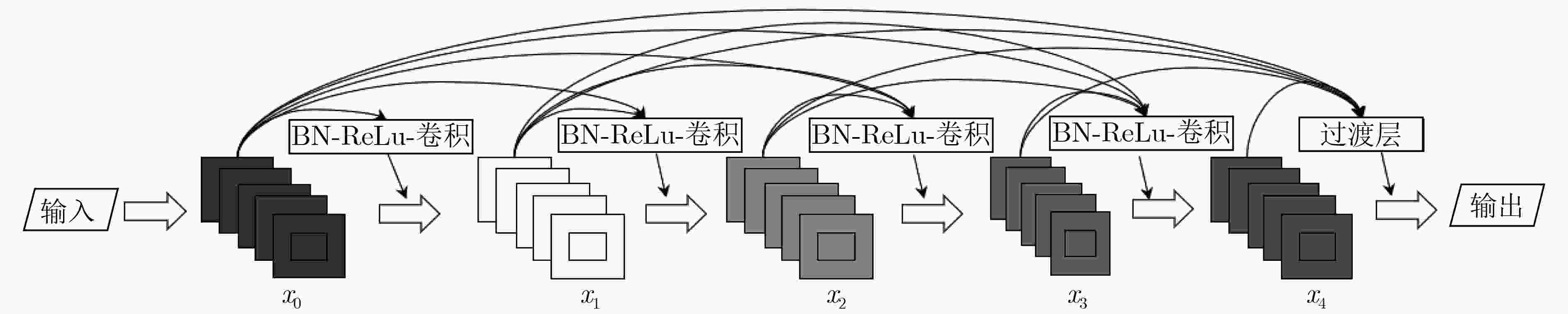
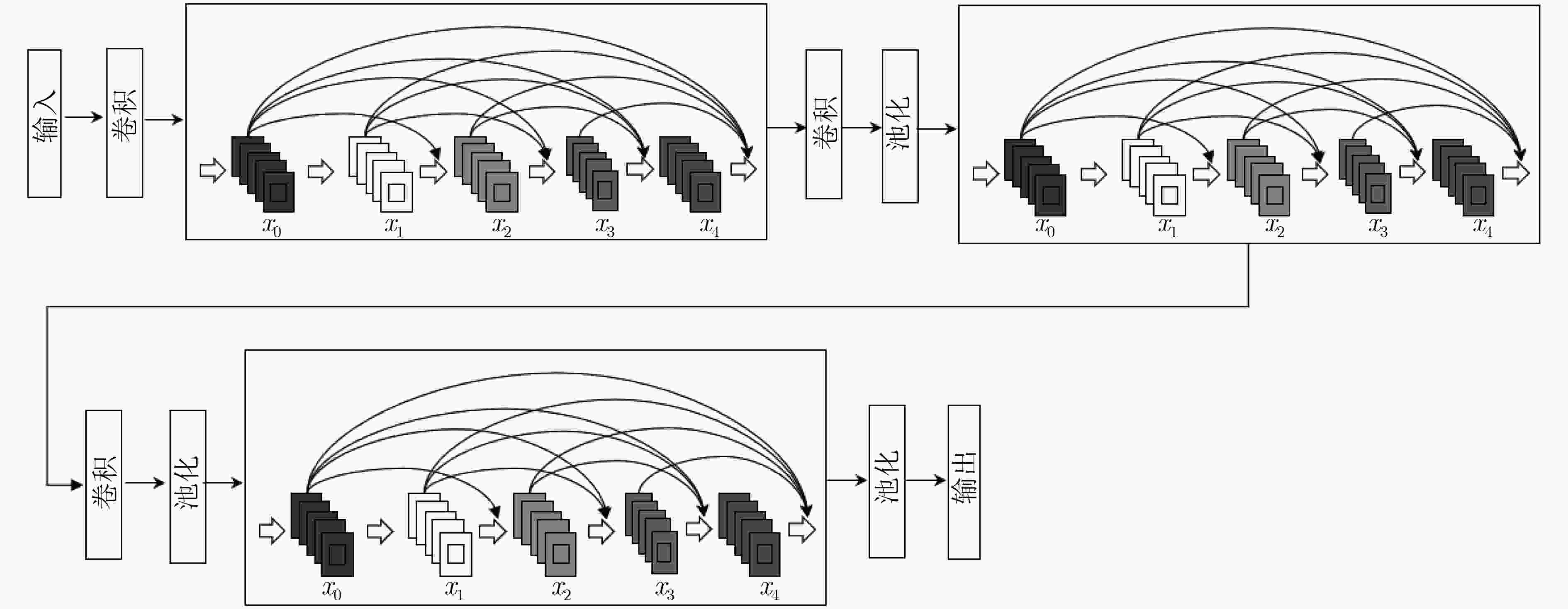
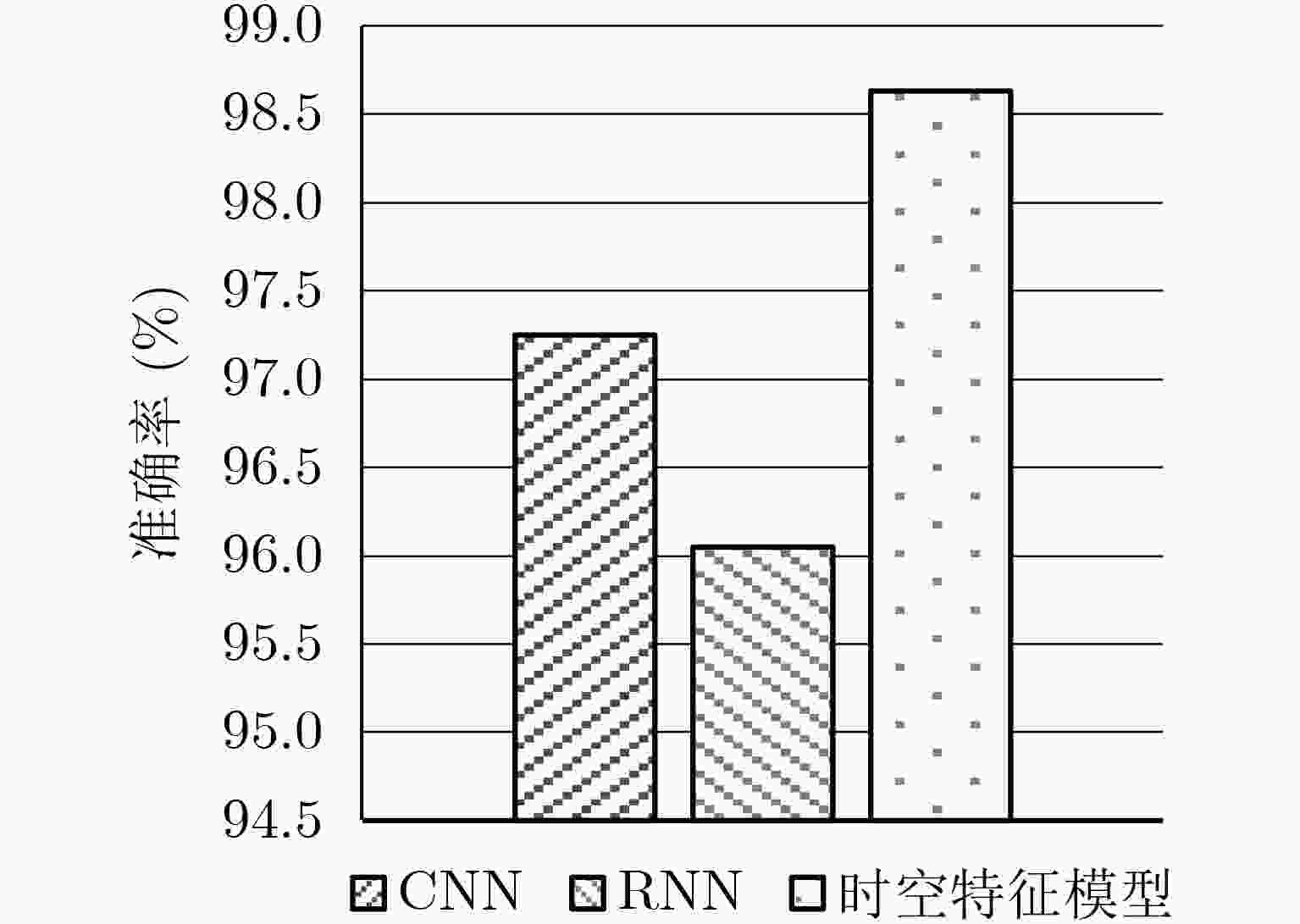
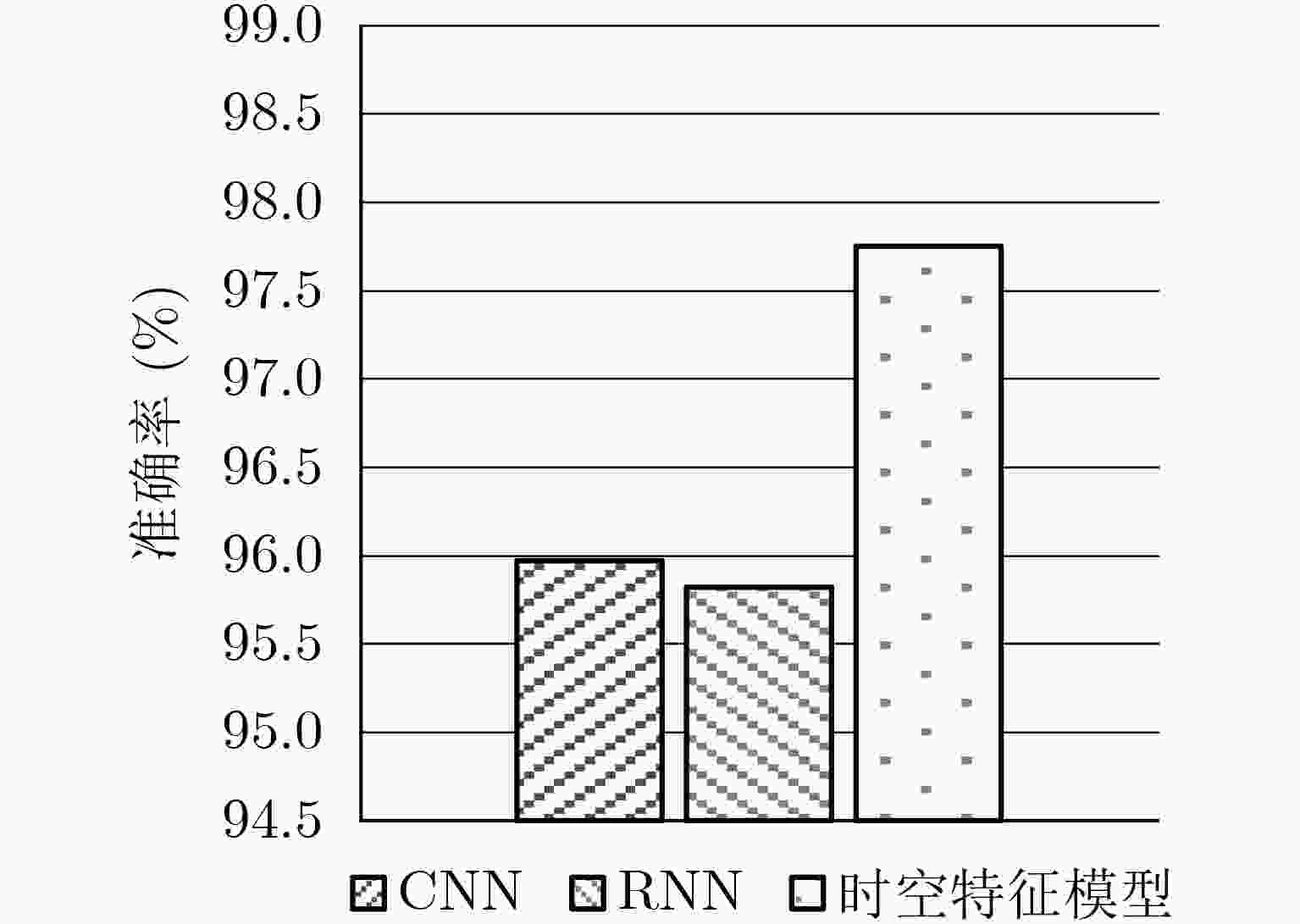
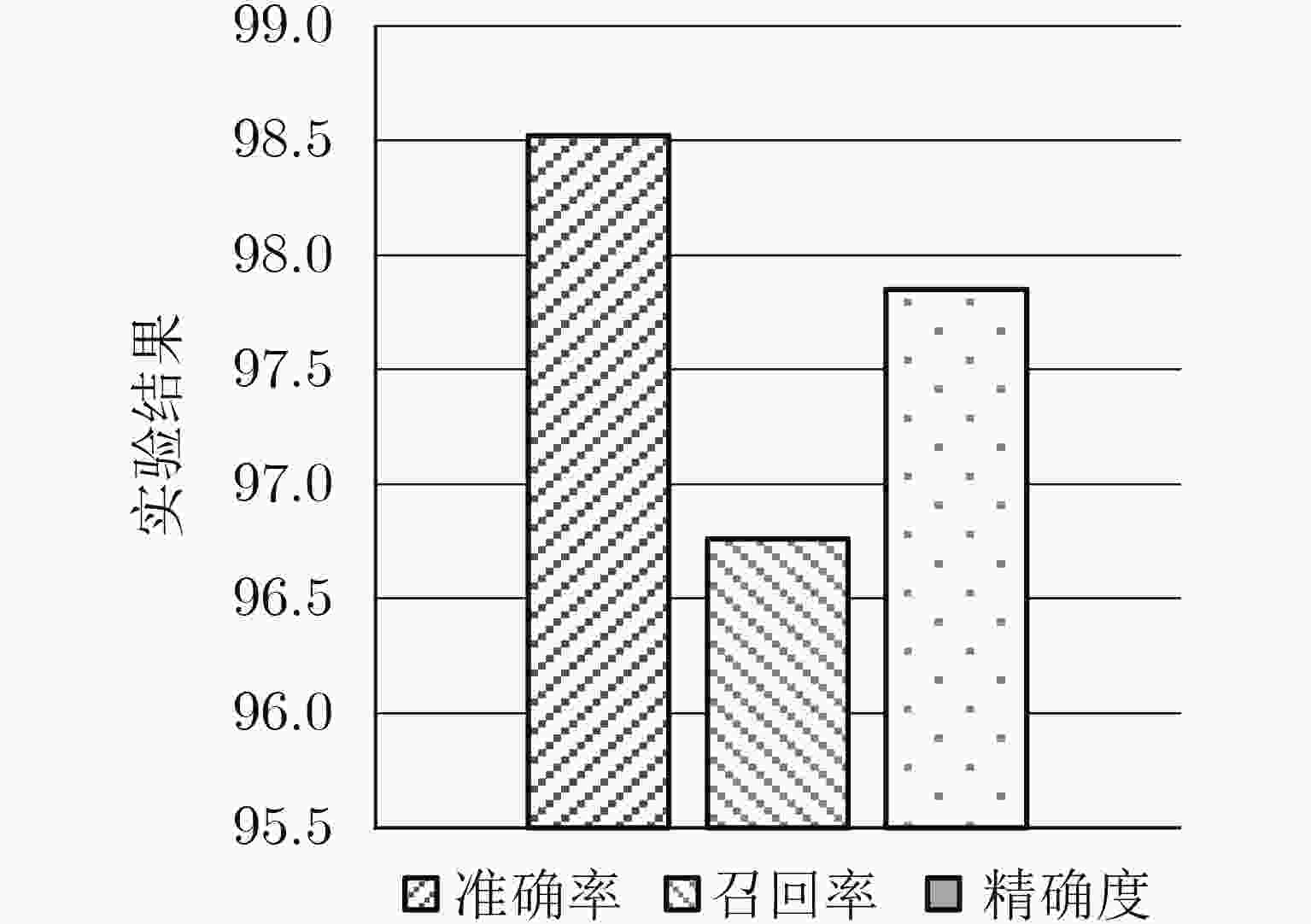
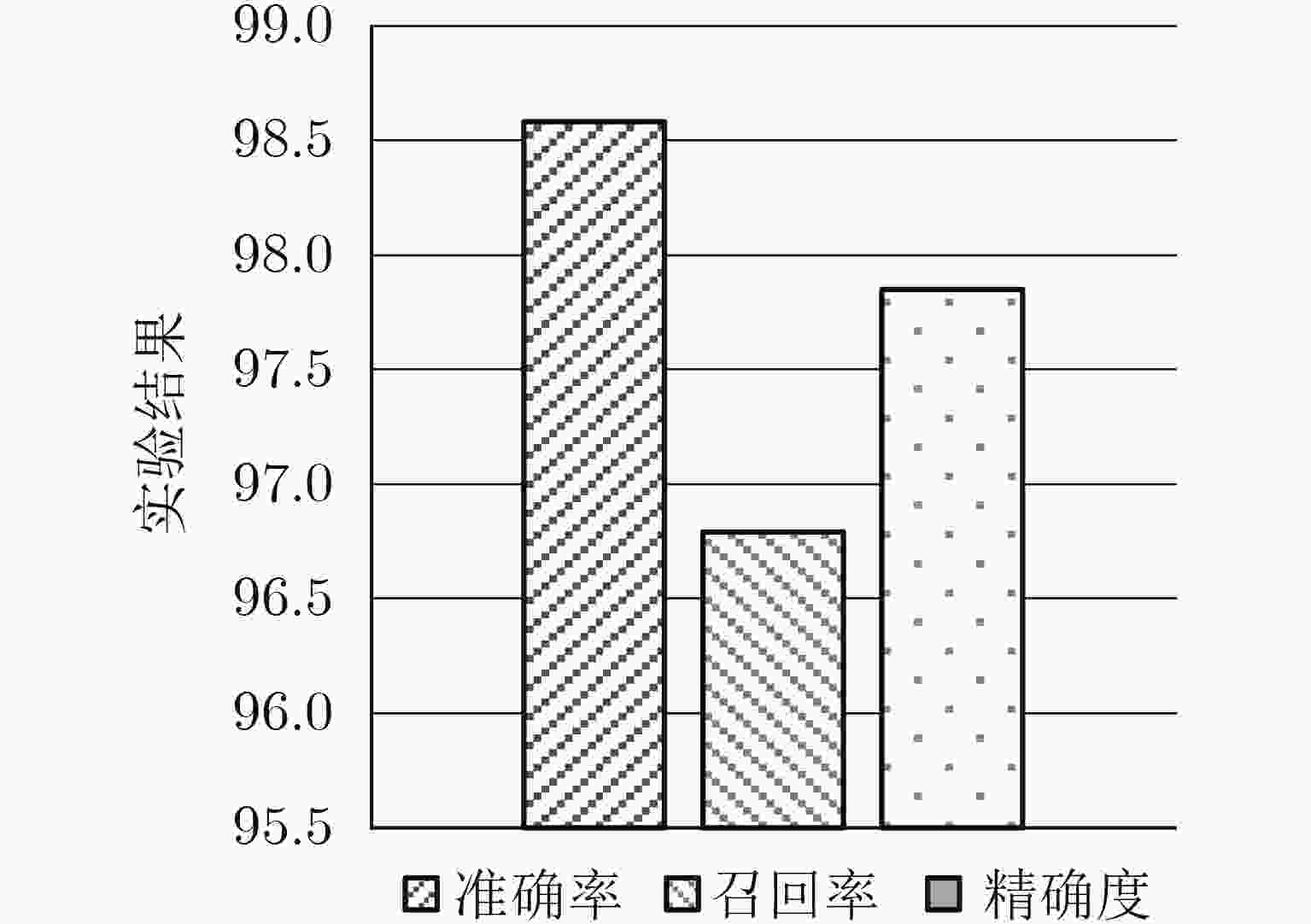
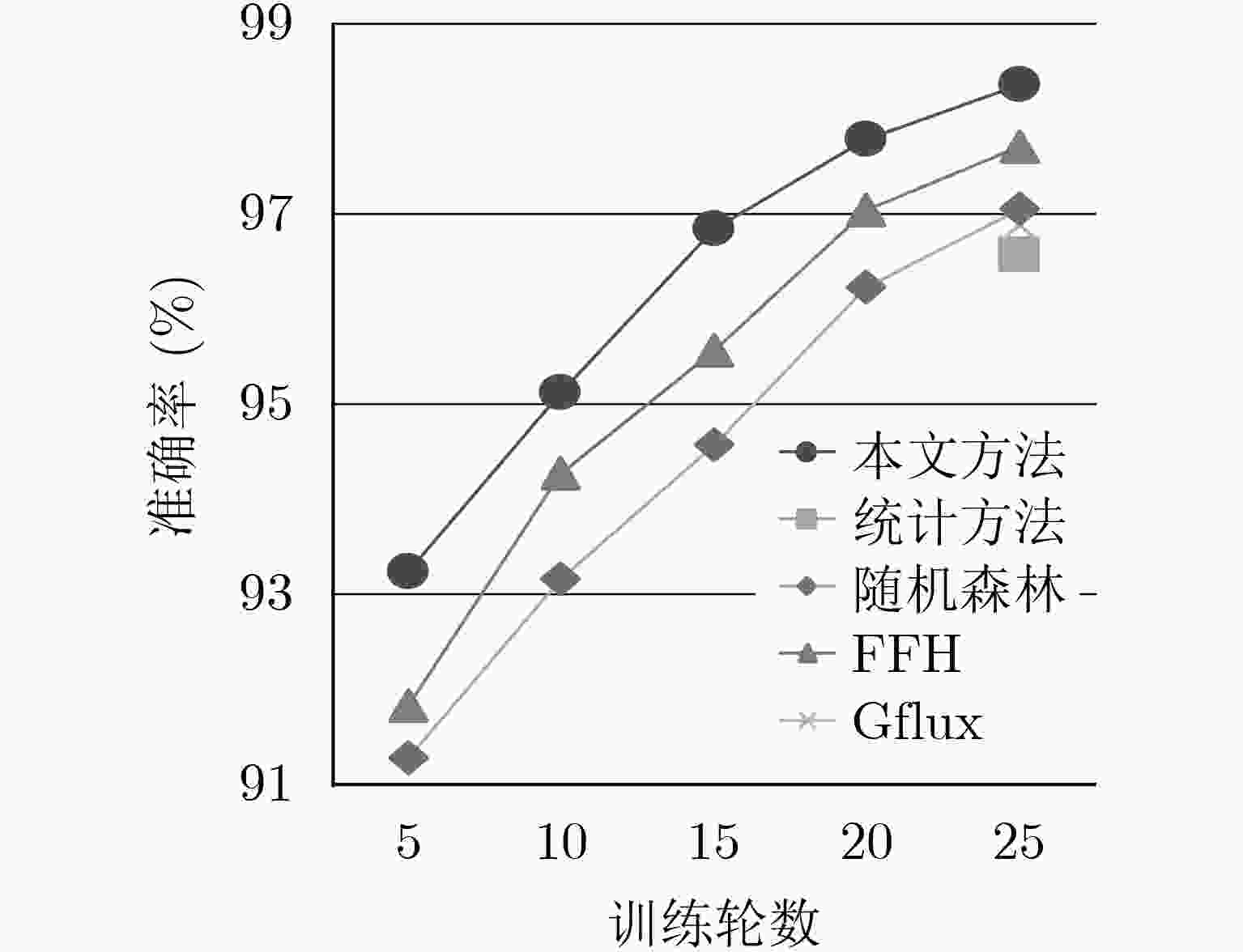
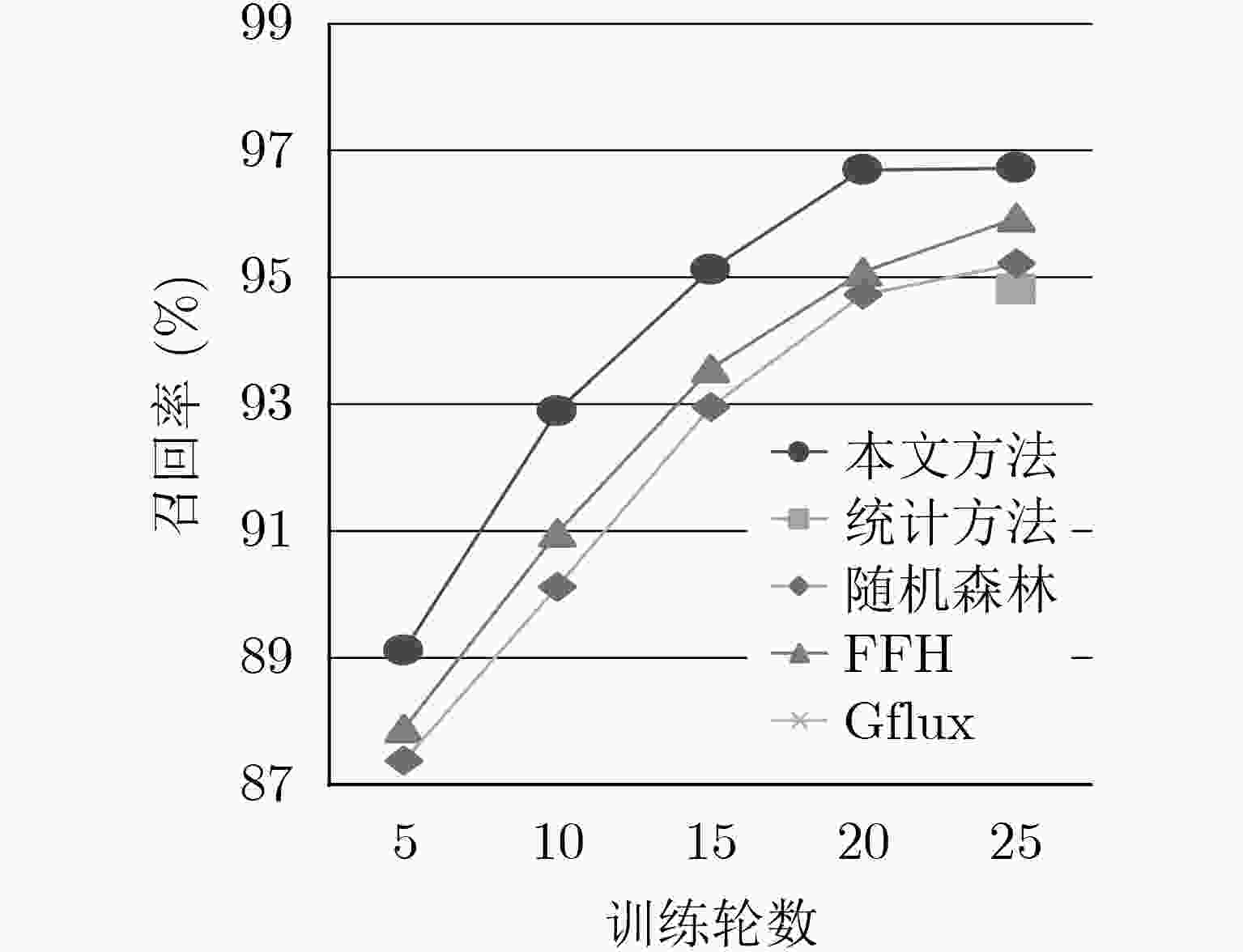
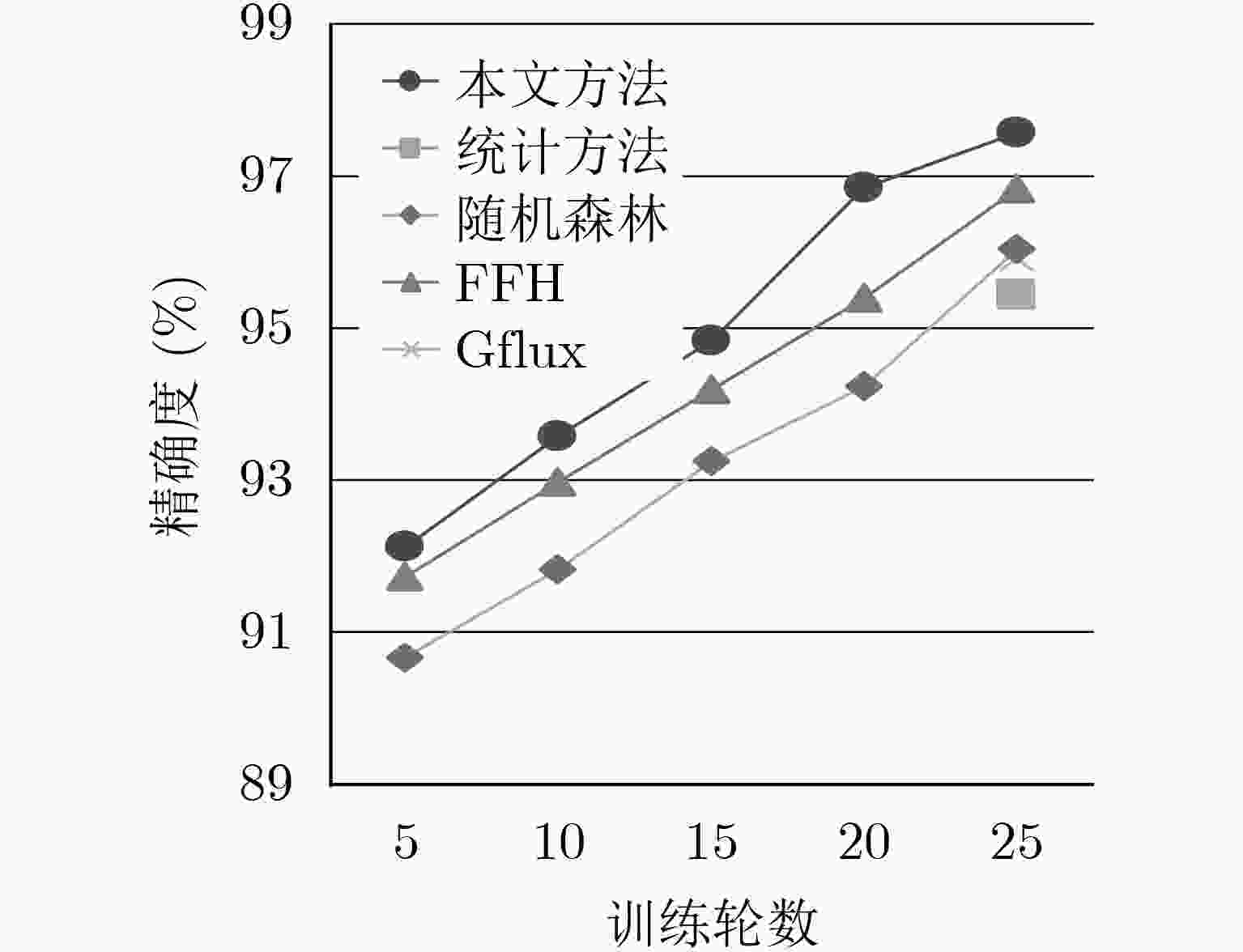
僵尸网络已成为网络空间安全的主要威胁之一,虽然目前可通过逆向工程等技术来对其进行检测,但是使用了诸如fast-flux等隐蔽技术的僵尸网络可以绕过现有的安全检测并继续存活。现有的fast-flux僵尸网络检测方法主要分为主动和被动两种,前者会造成较大的网络负载,后者存在特征值提取繁琐的问题。因此为了有效检测fast-flux僵尸网络并解决传统检测方法中存在的问题,该文结合卷积神经网络和循环神经网络,提出了基于流量时空特征的fast-flux僵尸网络检测方法。结合CTU-13和ISOT公开数据集的实验结果表明,该文所提检测方法和其他方法相比,准确率提升至98.3%,召回率提升至96.7%,精确度提升至97.5%。
Abstract:Botnets have become one of the main threats to cyberspace security. Although they can be detected by techniques such as reverse engineering, botnets using covert technologies such as fast-flux can successfully bypass existing security detection and continue to survive. The existing fast-flux botnet detection methods are mainly divided into active and passive, the former will cause a large network load, and the latter has the problem of cumbersome feature value extraction. In order to effectively detect fast-flux botnets and alleviate the problems in traditional detection methods, a fast-flux botnet detection method based on spatiotemporal features of network traffic is proposed, combined with convolutional neural networks and recurrent neural network models, the fast-flux botnet is detected from both spatial and temporal dimensions. Experiments performed on the CTU-13 and ISOT public data sets show that compared with other methods, the accuracy rate of the proposed method is 98.3%, the recall rate is 96.7%, and the accuracy is 97.5%.
-
Key words:
- Botnet /
- Fast-flux /
- Convolutional Neural Network (CNN) /
- Recurrent Neural Network (RNN)
-
表 1 实验硬件环境参数表
硬件 具体参数 服务器 戴尔PowerEdge R730XD 内存 4个金士顿16 GB 处理器 2个英特尔E5-2630 硬盘 东芝2 TB 表 2 实验软件环境参数表
软件 版本 操作系统 Cenos7 编译器 IntelliJ Idea GCC 5.2.1 TensorFlow 1.1.1 表 3 数据集组成表
数据类型 CTU-13 ISOT数据集 自收集 良性DNS流量 5133 0 2874 Fast-FluxDNS流量 4229 4003 0 -
OR K, RAVIV P, and GUY M. Digging deeper-an in-depth analysis of a fast flux network[EB/OL]. https://www.akamai.com/cn/zh/multimedia/documents/white-paper/digging-deeper-in-depth-analysis-of-fast-flux-network.pdf, 2017. 蒋鸿玲, 邵秀丽, 李耀芳. 基于MapReduce的僵尸网络在线检测算法[J]. 电子与信息学报, 2013, 35(7): 1732–1738.JIANG Hongling, SHAO Xiuli, and LI Yaofang. Online botnet detection algorithm using MapReduce[J]. Journal of Electronics &Information Technology, 2013, 35(7): 1732–1738. ZANG Xiaodong, GONG Jian, MO Shaohuang, et al. Identifying fast-flux botnet with AGD names at the upper DNS hierarchy[J]. IEEE Access, 2018, 6: 69713–69727. doi: 10.1109/ACCESS.2018.2880884 AL-DUWAIRI B, AL-HAMMOURI A, ALDWAIRI M, et al. GFlux: A google-based system for Fast Flux detection[C]. 2015 IEEE Conference on Communications and Network Security (CNS), Florence, Italy, 2015: 755–756. doi: 10.1109/CNS.2015.7346920. ALIEYAN K, ANBAR M, ALMOMANI A, et al. Botnets detecting attack based on DNS features[C]. 2018 International Arab Conference on Information Technology (ACIT), Werdanye, Lebanon, 2018: 1–4. doi: 10.1109/ACIT.2018.8672582. ALMOMANI A. Fast-flux hunter: A system for filtering online fast-flux botnet[J]. Neural Computing and Applications, 2018, 29(7): 483–493. doi: 10.1007/s00521-016-2531-1 Al NAWASRAH A. Fast flux botnet detection based on adaptive dynamic evolving spiking neural network[D]. [Ph.D. dissertation], University of Salford, 2018. JIANG Cibin and LI J S. Exploring global IP-usage patterns in fast-flux service networks[J]. Journal of Computers, 2017, 12(4): 371–380. WANG Zhi, QIN Meilin, CHEN Mengqi, et al. Hiding fast flux botnet in plain email sight[C]. SecureComm 2017 International Workshops on Security and Privacy in Communication Networks, Niagara Falls, Canada, 2017: 182–197. REIMERS A C, BRUGGEMAN F J, OLIVIER B G, et al. Fast flux module detection using matroid theory[J]. Journal of Computational Biology, 2015, 22(5): 414–424. doi: 10.1089/cmb.2014.0141 ERQUIAGA M J, CATANIA C, and GARCÍA S. Detecting DGA malware traffic through behavioral models[C]. 2016 IEEE Biennial Congress of Argentina (ARGENCON), Buenos Aires, Argentina, 2016: 1–6. doi: 10.1109/ARGENCON.2016.7585238. TORABI S, BOUKHTOUTA A, ASSI C, et al. Detecting internet abuse by analyzing passive DNS traffic: A survey of implemented systems[J]. IEEE Communications Surveys & Tutorials, 2018, 20(4): 3389–3415. doi: 10.1109/COMST.2018.2849614 HSU F H, WANG C S, HSU C H, et al. Detect fast-flux domains through response time differences[J]. IEEE Journal on Selected Areas in Communications, 2014, 32(10): 1947–1956. doi: 10.1109/JSAC.2014.2358814 CELIK Z B and MCDANIEL P. Extending detection with privileged information via generalized distillation[C]. 2018 IEEE Security and Privacy Workshops (SPW), San Francisco, USA, 2018: 83–88. doi: 10.1109/SPW.2018.00021. CHEN Wenlin, CHEN Yixin, and WEINBERGER K Q. Fast flux discriminant for large-scale sparse nonlinear classification[C]. The 20th ACM SIGKDD International Conference on Knowledge Discovery and Data Mining, New York, 2014: 621–630. 田生伟, 周兴发, 禹龙, 等. 基于双向LSTM的维吾尔语事件因果关系抽取[J]. 电子与信息学报, 2018, 40(1): 200–208. doi: 10.11999/JEIT170402TIAN Shengwei, ZHOU Xingfa, YU Long, et al. Causal relation extraction of Uyghur events based on bidirectional Long Short-term Memory model[J]. Journal of Electronics &Information Technology, 2018, 40(1): 200–208. doi: 10.11999/JEIT170402 CTU University. MCFP Dataset-Malware Capture facility project[EB/OL]. https://mcfp.weebly.com/mcfp-dataset.html, 2018. University of Victoria. ISOT Botnet dataset[EB/OL]. https://www.uvic.ca/engineering/ece/isot/datasets/index.php, 2010. LOMBARDO P, SAELI S, BISIO F, et al. Fast flux service network detection via data mining on passive DNS traffic[C]. The 21st International Conference on Information Security, Guildford, UK, 2018: 463–480. doi: 10.1007/978-3-319-99136-8_25. CHAHAL P S and KHURANA S S. TempR: Application of stricture dependent intelligent classifier for fast flux domain detection[J]. International Journal of Computer Network and Information Security, 2016, 8(10): 37–44. doi: 10.5815/ijcnis.2016.10.05 -





 下载:
下载:



 下载:
下载:
