A Mobile Crowdsensing Data Security Delivery Model Based on Tangle Network
-
摘要:
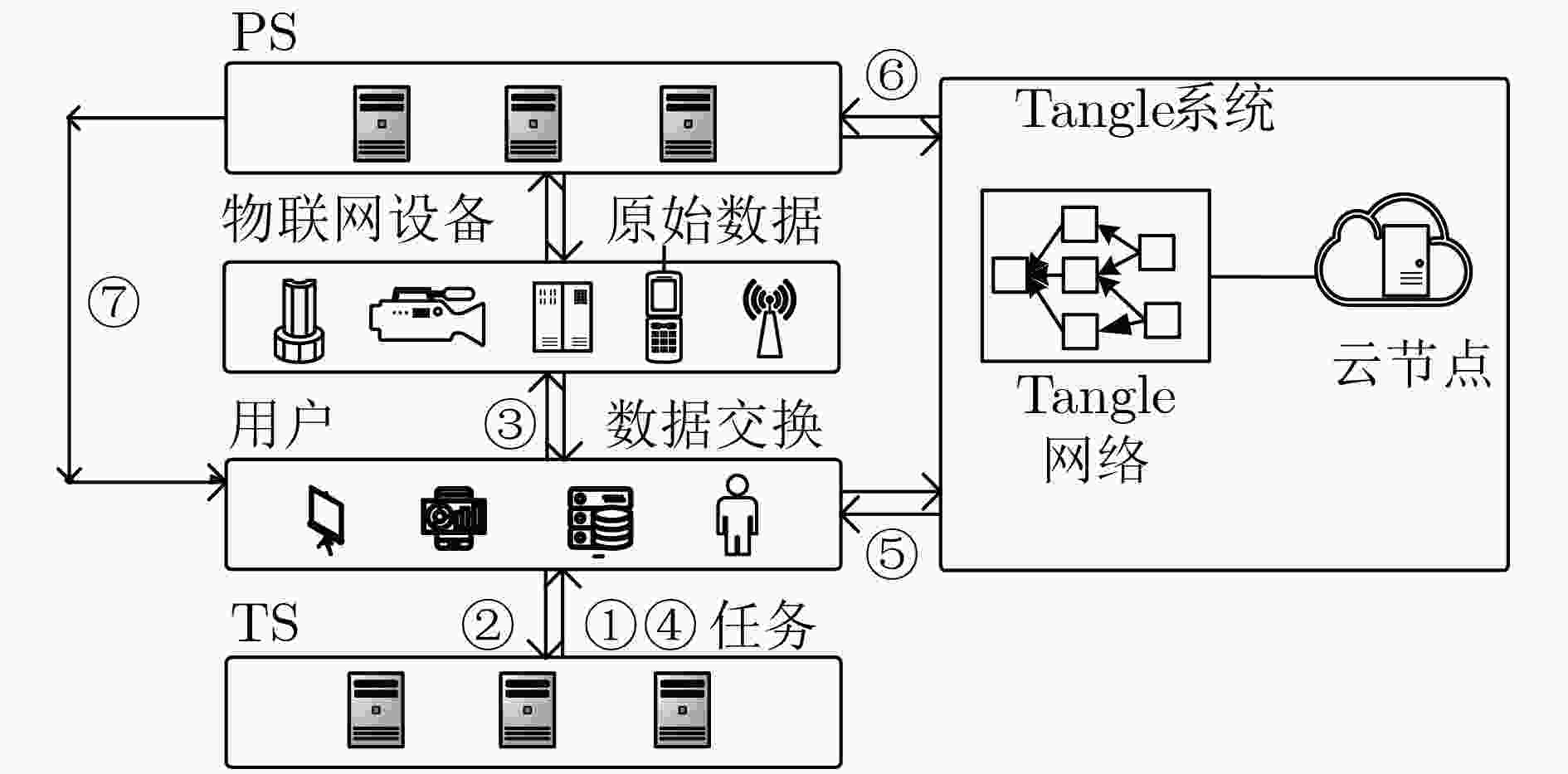
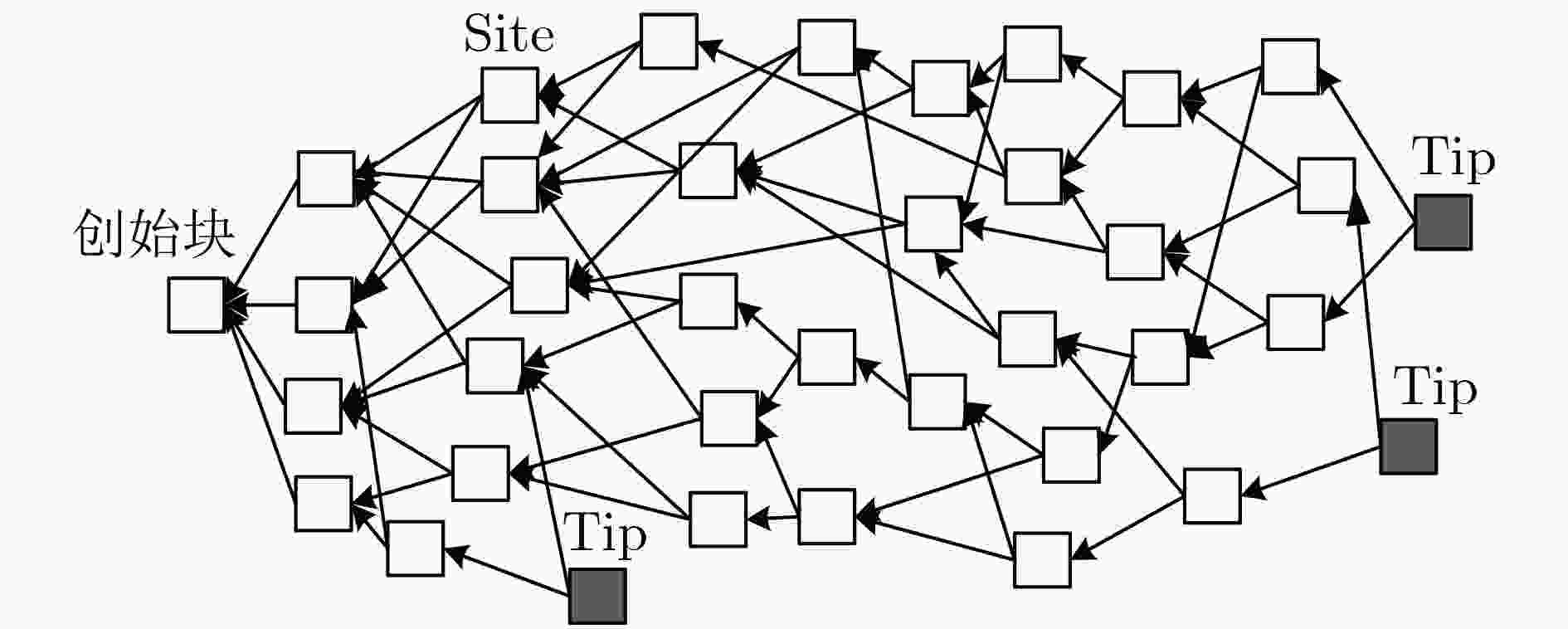
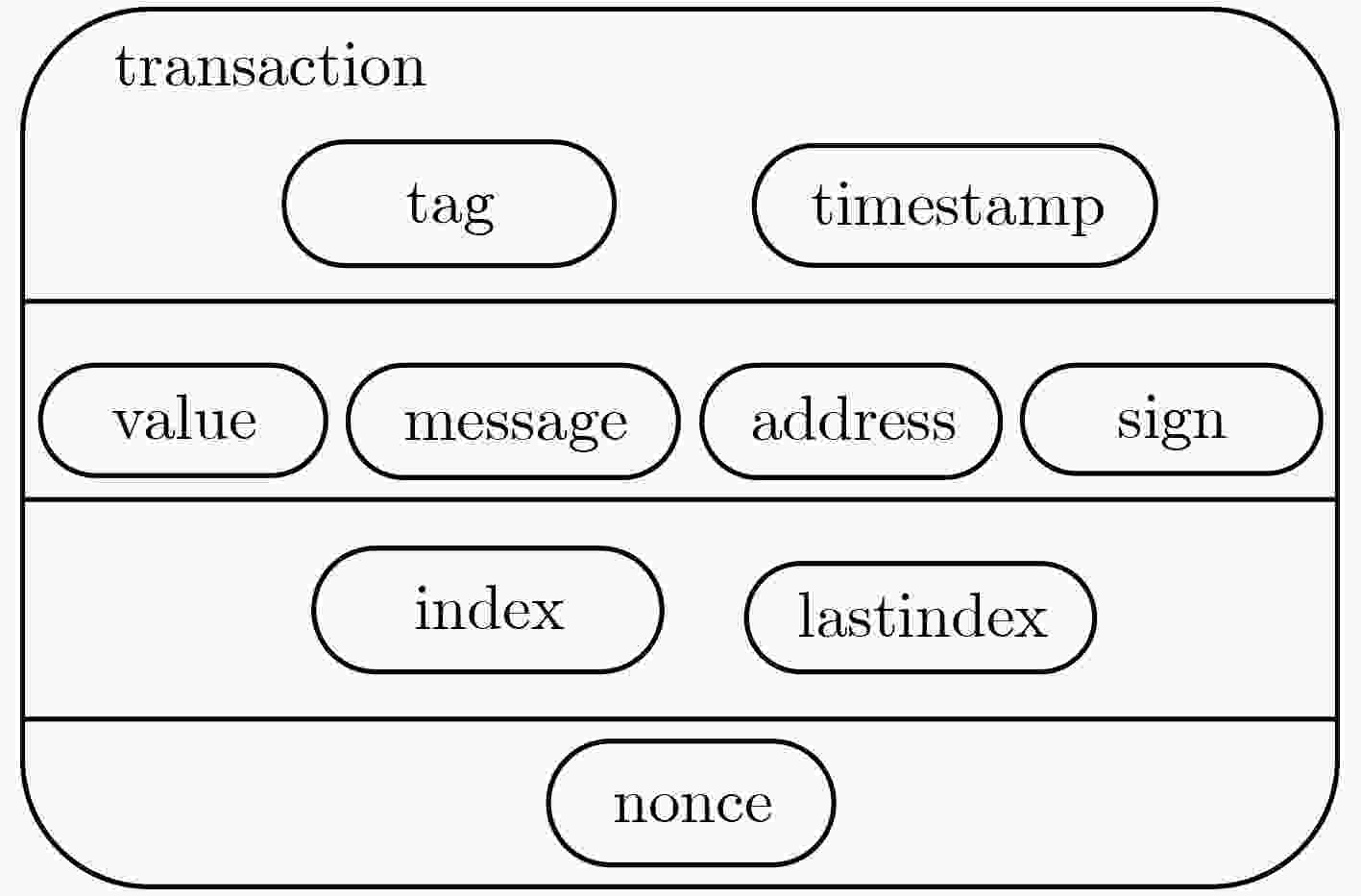
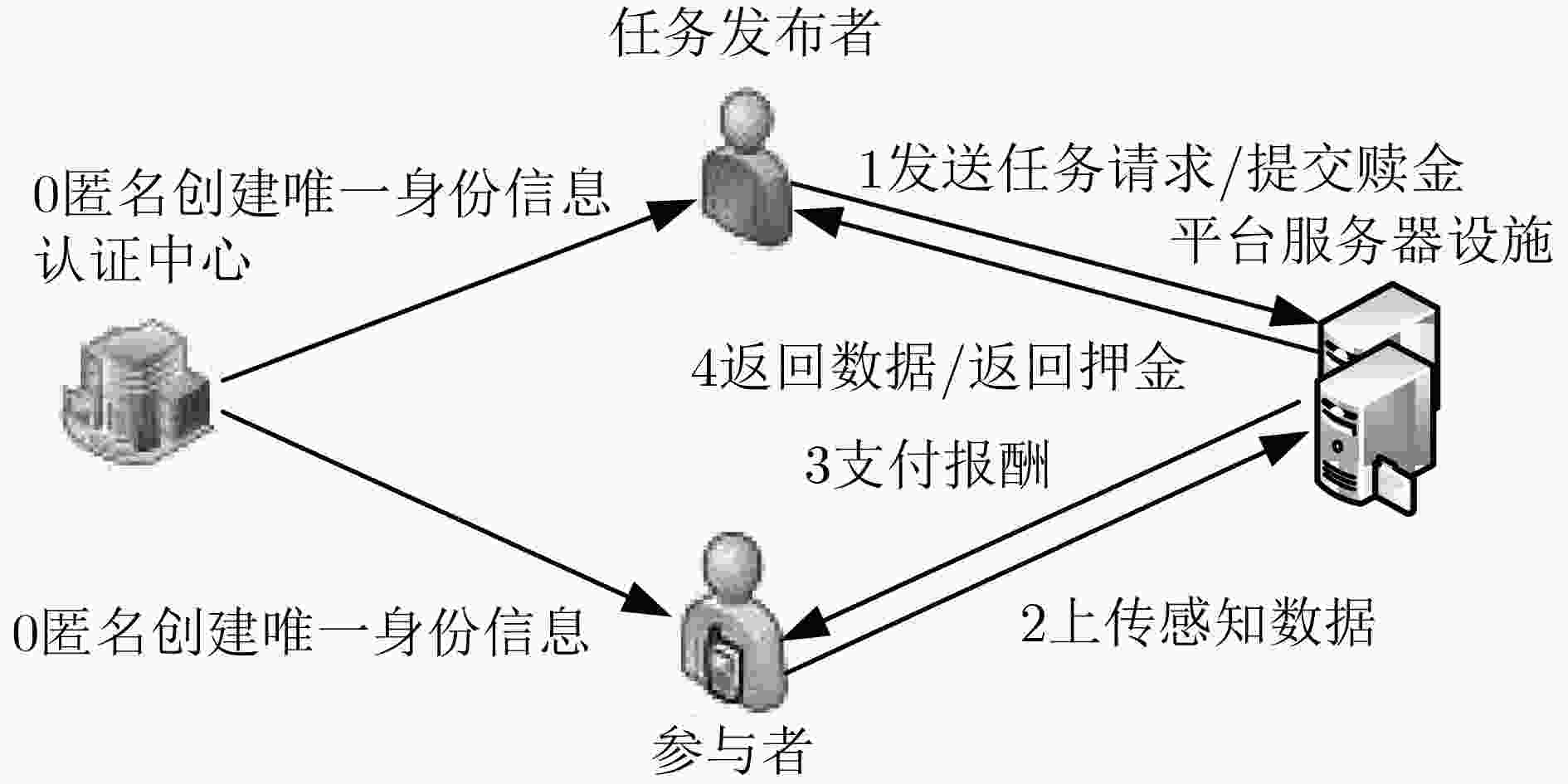
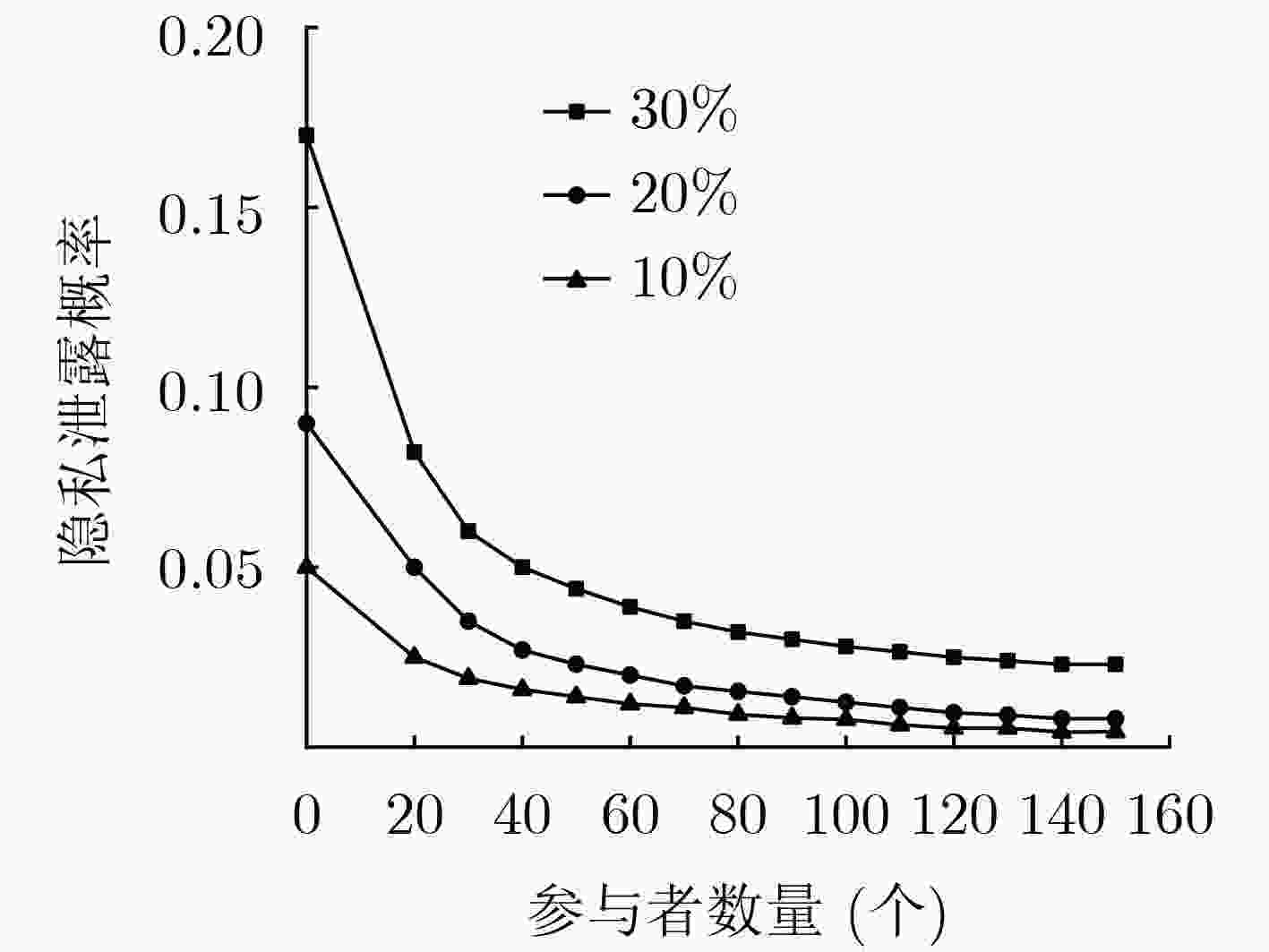
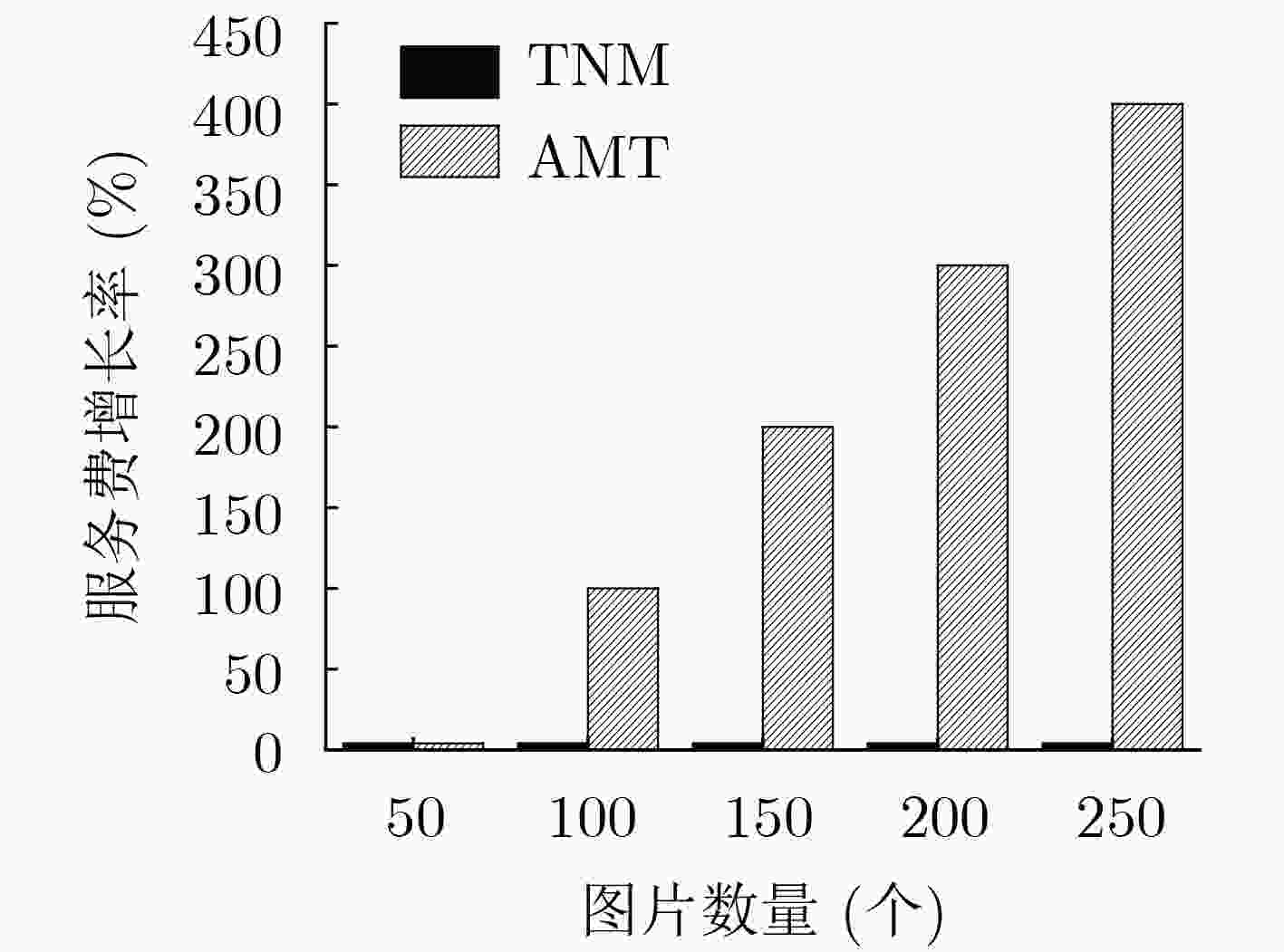
针对现有群智感知平台在数据和酬金交付过程中存在的安全风险和隐私泄露问题,该文提出一种基于Tangle网络的分布式群智感知数据安全交付模型。首先,在数据感知阶段,调用局部异常因子检测算法剔除异常数据,聚类获取感知数据并确定可信参与者节点。然后,在交易写入阶段,使用马尔科夫蒙特卡洛算法选择交易并验证其合法性,通过注册认证中心登记完成匿名身份数据上传,并将交易同步写入分布式账本。最后,结合Tangle网络的累计权重共识机制,当交易安全性达到阈值时,任务发布者可进行数据和酬金的安全交付。仿真试验表明,在模型保护用户隐私的同时,增强了数据和酬金的安全交付能力,相比现有感知平台降低了时间复杂度和任务发布成本。
Abstract:Considering the security risks and privacy leaks in the process of data and reward in the Mobile CrowdSensing (MCS), a distributed security delivery model based on Tangle network is proposed. Firstly, in the data perception stage, the local outlier factor detection algorithm is used to eliminate the anomaly data, cluster the perception data and determine the trusted participant. Then, in the transaction writing stage, Markov Monte Carlo algorithm is used to select the transaction and verify its legitimacy. The anonymous identity data is uploaded by registering with the authentication center, and the transaction is synchronously written to the distributed account book. Finally, combined with Tangle network cumulative weight consensus mechanism, when the security of transaction reaches its threshold, task publishers can safely deliver data and rewards. The simulation results show that the model not only protects user privacy, but also enhances the ability of secure delivery of data and reward. Compared with the existing sensing platform, the model reduces the time complexity and task publishing cost.
-
Key words:
- Mobile CrowdSensing (MCS) /
- Tangle network /
- Perceived data /
- Secure delivery
-
表 1 算法1:基于参与者选择的LOF算法
输入:参与者的位置信息集N, k近邻参数 输出:前k个数据的LOF (1) 计算任意数据点之间的欧式距离${\rm{disk}}(i,j)$; (2) 计算所有数据点和其前k个数据点间的距离${\rm{disk}}_k^{}(i)$; (3) 计算所有数据点的k距离邻居${N_K}(i)$; $ {N_K}(i) = \left\{ {\left. {i'} \right|} \right.i' \in N, $
$ \left.{\rm{dist}}(i,i') \le {\rm{dis}}{{\rm{t}}_k}(i) \right\}$(4) 计算所有数据点的局部可达密度${\rm{lr}}{{\rm{d}}_k}(i)$:
$\begin{array}{*{20}{l} }\quad\quad { {\rm{lr} }{ {\rm{d} }_k}(i) = \frac{ {\left\| {\left. { {N_K}(i)} \right\|} \right.} }{ {\displaystyle\sum\limits_{i' \in {N_k}(i)} { {\rm{reachdis} }{ {\rm{t} }_k}(i' \leftarrow i)} } } }\\\qquad { {\rm{reachdis} }{ {\rm{t} }_k}(i' \leftarrow i) = {\rm{max} }\left. {\left\{ { {\rm{dis} }{ {\rm{t} }_k}(i),{\rm{dist} }(i,i')} \right.} \right\} }\end{array}\;\;\;\;\;\;\;\;\quad\ \ \left( 1 \right)$(5) 计算${\rm{LO}}{{\rm{F}}_K}(i)$
$\begin{array}{*{20}{l}}\quad\quad\ \ {{\rm{LO}}{{\rm{F}}_K}(i) = \frac{{\displaystyle\sum\limits_{i' \in {N_K}(i)} {\frac{{{\rm{lr}}{{\rm{d}}_k}(i')}}{{{\rm{lr}}{{\rm{d}}_k}(i)}}} }}{{\left\| {\left. {{N_K}(i)} \right\|} \right.}} }\\\quad\quad \quad = {\displaystyle\sum\limits_{i' \in {N_K}(i)} {{\rm{lr}}{{\rm{d}}_k}(i') \cdot \sum\limits_{i' \in {N_K}(i)} {{\rm{reachdis}}{{\rm{t}}_k}(i' \leftarrow i)} } }\;\;\;\;\;\;\;\;\;\;\;\;\left( 2 \right)\end{array}$(6) 对${\rm{LO}}{{\rm{F}}_K}(i)$进行排序,剔除LOF高的数据。 表 2 算法2:基于MCMC的端点选择算法
输入:马尔可夫链状态转移矩阵Q,平稳分布$\pi (x)$,最大转移次数n1,选定时间间隔[W, 2W]及该间隔下的样本个数n2(此时的样本个数为
新到的交易所观察到的交易数目)。输出:两个最先走到Tip的粒子为新交易将验证的端点。 for t=0 to n1 + n2–1: (1) 初始化马尔可夫链${X_0} = {x_0}$; (2) 独立的在该选定的间隔中随机放入N个粒子定义为“Walker”; (3) 每个粒子根据定义的转移概率P随机的选出一条路径,向着Tip的方向进行游走。其中转移概率定义为:
$\qquad{P_{xy} } = \dfrac{ { { {\rm e}^{ - a({H_x} - {H_y})} } } }{ {\displaystyle\sum\limits_{z:x \leftarrow z} { { {\rm e}^{ - a({H_x} - {H_z})} } } } }\qquad\qquad\qquad\qquad\qquad\qquad\qquad\qquad\qquad\qquad\qquad\qquad\qquad\qquad\qquad\qquad\qquad\qquad\qquad\qquad\qquad\qquad\qquad \left( 3 \right)$其中,$a > 0$,为自定义参数,${H_x}$和${H_y}$为交易x和交易y的累计权重,转移后第t个时刻的马尔可夫链状态为${X_t} = {{{x}}_t}$,下一个交易可
能的状态为${y_{t + 1}} = {x_t}p(x|{x_t})$,此时$\pi (x) = ({x_{n1} },{x_{n1 + 1} },···,{x_{n1 + n2 - 1} })$。表 3 群智感知过程中的隐私泄露点
隐私泄露过程 隐私泄露位置 窃取隐私难易程度 参与者将采集数据上传至TS 参与者与TS通信的中间网络遭受中间人攻击 易 参与者与其他传感器交互 传感器设备 易 交易写入Tangle网络 Tangle网络 易 TS调用LOF算法 TS 中 TS指定获胜节点 TS 中 PS支付酬金 PS 中 表 4 Tangle网络处理数据的时间花销
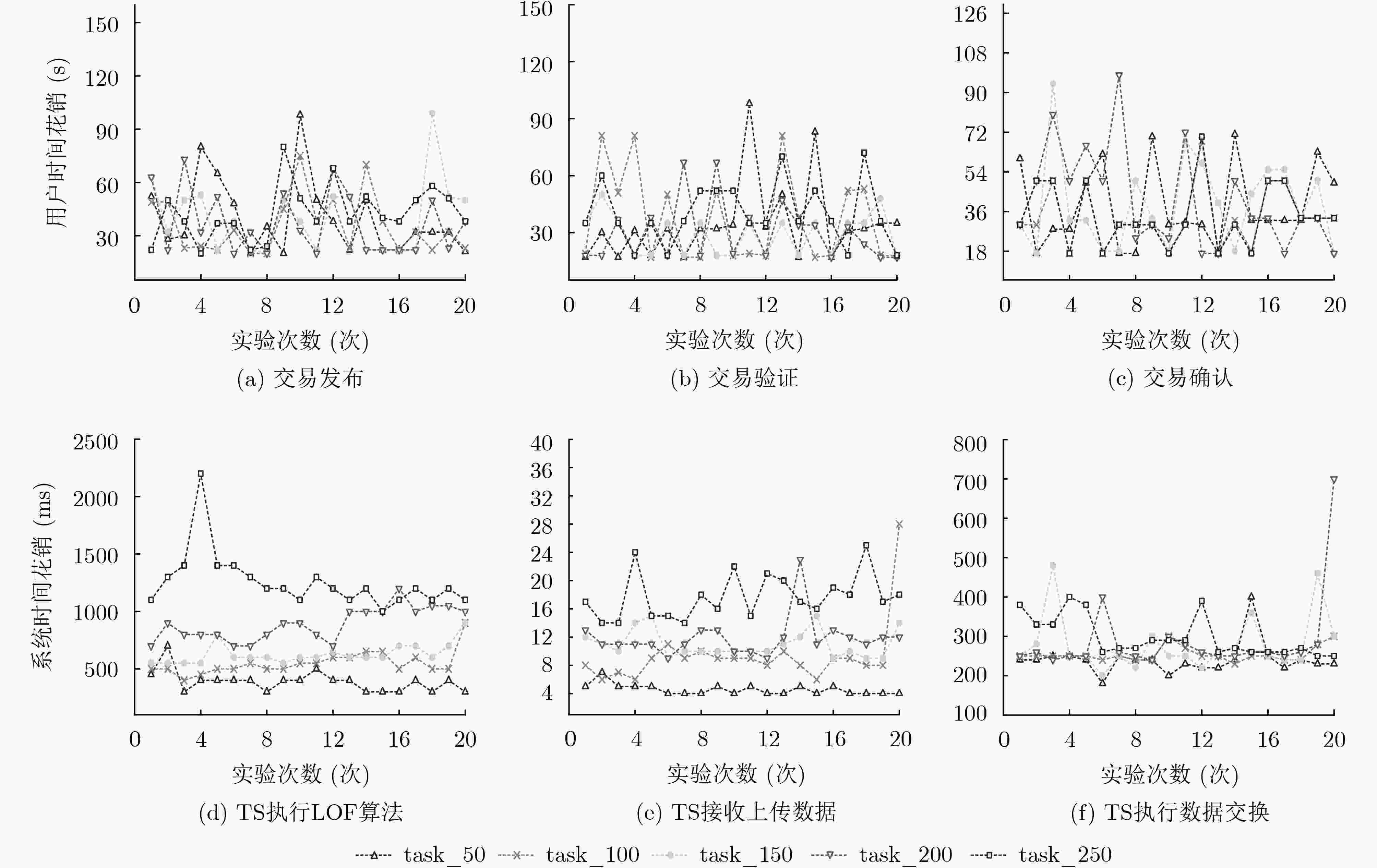
名称 任务发布 任务接收 交易上传 任务大小(kb) 处理时间(ms) 任务大小(kb) 处理时间(ms) 任务大小(kb) 处理时间(ms) Task_50 1179.59 489.40 1289.69 4.47 4.7945 245.67 Task_100 2356.45 620.43 2416.15 7.89 9.7255 245.69 Task_150 3552.86 722.71 3932.77 13.79 14.0229 245.65 Task_200 4841.76 905.32 4825.98 11.63 21.3921 245.67 Task_250 5761.84 1219.45 5832.97 18.23 25.7526 478.90 -
熊金波, 马蓉, 牛犇, 等. 移动群智感知中基于用户联盟匹配的隐私保护激励机制[J]. 计算机研究与发展, 2018, 55(7): 1359–1370. doi: 10.7544/issn1000-1239.2018.20180080XIONG Jinbo, MA Rong, NIU Ben, et al. Privacy protection incentive mechanism based on user-union matching in mobile crowdsensing[J]. Journal of Computer Research and Development, 2018, 55(7): 1359–1370. doi: 10.7544/issn1000-1239.2018.20180080 崔勇, 宋健, 缪葱葱, 等. 移动云计算研究进展与趋势[J]. 计算机学报, 2017, 40(2): 273–295. doi: 10.11897/SP.J.1016.2017.00273CUI Yong, SONG Jian, Miao Congcong, et al. Mobile cloud computing research progress and trends[J]. Chinese Journal of Computers, 2017, 40(2): 273–295. doi: 10.11897/SP.J.1016.2017.00273 何云华, 李梦茹, 李红, 等. 群智感知应用中基于区块链的激励机制[J]. 计算机研究与发展, 2019, 56(3): 544–554. doi: 10.7544/issn1000-1239.2019.20170670HE Yunhua, LI Mengru, LI Hong, et al. A blockchain based incentive mechanism for crowdsensing applications[J]. Journal of Computer Research and Development, 2019, 56(3): 544–554. doi: 10.7544/issn1000-1239.2019.20170670 HUANG Kuanlun, KANHERE S S, and HU Wen. Preserving privacy in participatory sensing systems[J]. Computer Communications, 2010, 33(11): 1266–1280. doi: 10.1016/j.comcom.2009.08.012 DONG Kai, GU Tao, TAO Xianping, et al. Privacy protection in participatory sensing applications requiring fine-grained locations[C]. The 16th IEEE International Conference on Parallel and Distributed Systems, Shanghai, China, 2010. doi: 10.1109/ICPADS.2010.127. CHRISTIN D, GUILLEMET J, REINHARDT A, et al. Privacy-preserving collaborative path hiding for participatory sensing applications[C]. The 8th IEEE International Conference on Mobile Ad-hoc and Sensor Systems, Valencia, Spain, 2011: 341–350. doi: 10.1109/MASS.2011.41. 徐哲, 李卓, 陈昕. 面向移动群智感知的多任务分发算法[J]. 计算机应用, 2017, 37(1): 18–23, 47. doi: 10.11772/j.issn.1001-9081.2017.01.0018XU Zhe, LI Zhuo, and CHEN Xin. Multi-task assignment algorithm for mobile crowdsensing[J]. Journal of Computer Applications, 2017, 37(1): 18–23, 47. doi: 10.11772/j.issn.1001-9081.2017.01.0018 CHRISTIN D, ROßKOPF C, HOLLICK M, et al. IncogniSense: An anonymity-preserving reputation framework for participatory sensing applications[J]. Pervasive and Mobile Computing, 2013, 9(3): 353–371. doi: 10.1016/j.pmcj.2013.01.003 RESTUCCIA F and DAS S K. FIDES: A trust-based framework for secure user incentivization in participatory sensing[C]. IEEE International Symposium on A World of Wireless, Mobile and Multimedia Networks 2014, Sydney, Australia, 2014: 1–10. CHANG S H, CHEN Y S, and CHENG S M. Detection of Sybil attacks in participatory sensing using cloud based trust management system[C]. 2013 International Symposium on Wireless and Pervasive Computing, Taipei, China, 2013: 1–6. doi: 10.1109/ISWPC.2013.6707448. LI Ming, WENG Jian, YANG Anjia, et al. CrowdBC: A blockchain-based decentralized framework for crowdsourcing[J]. IEEE Transactions on Parallel and Distributed Systems, 2019, 30(6): 1251–1266. doi: 10.1109/TPDS.2018.2881735 LU Yuan, TANG Qiang, and WANG Guiling. ZebraLancer: Crowdsource knowledge atop open blockchain, privately and anonymously[J]. arXiv: 1803.01256v4, 2018. 严云洋, 瞿学新, 朱全银, 等. 基于离群点检测的分类结果置信度的度量方法[J]. 南京大学学报: 自然科学, 2019, 55(1): 102–109. doi: 10.13232/j.cnki.jnju.2019.01.010YAN Yunyang, QU Xuexin, ZHU Quanyin, et al. Confidence measure method of classification results based on outlier detection[J]. Journal of Nanjing University:Natural Science, 2019, 55(1): 102–109. doi: 10.13232/j.cnki.jnju.2019.01.010 张俊松, 甘勇, 贺蕾. 群智感知环境下支持激励机制实施的匿名身份认证协议研究[J]. 小型微型计算机系统, 2018, 39(7): 1522–1526. doi: 10.3969/j.issn.1000-1220.2018.07.027ZHANG Junsong, GAN Yong, and HE Lei. Anonymous authentication protocol for supporting incentive mechanism in crowd sensing[J]. Journal of Chinese Computer Systems, 2018, 39(7): 1522–1526. doi: 10.3969/j.issn.1000-1220.2018.07.027 JUNG T, LI Xiangyang, and WAN Meng. Collusion-tolerable privacy-preserving sum and product calculation without secure channel[J]. IEEE Transactions on Dependable and Secure Computing, 2015, 12(1): 45–57. doi: 10.1109/TDSC.2014.2309134 -





 下载:
下载:


 下载:
下载:
