An Encryption Transmission Scheme for Industrial Control System
-
摘要:
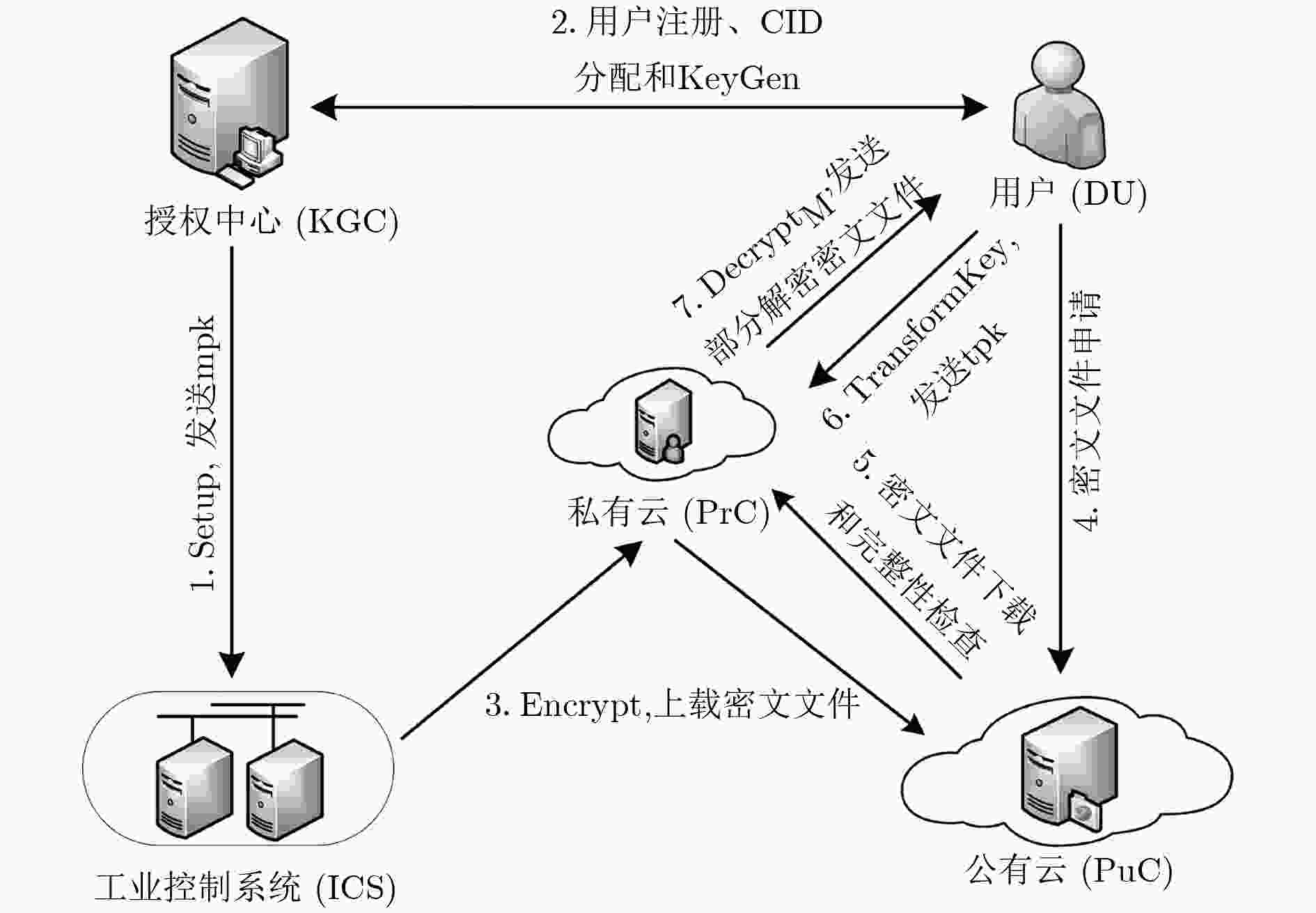
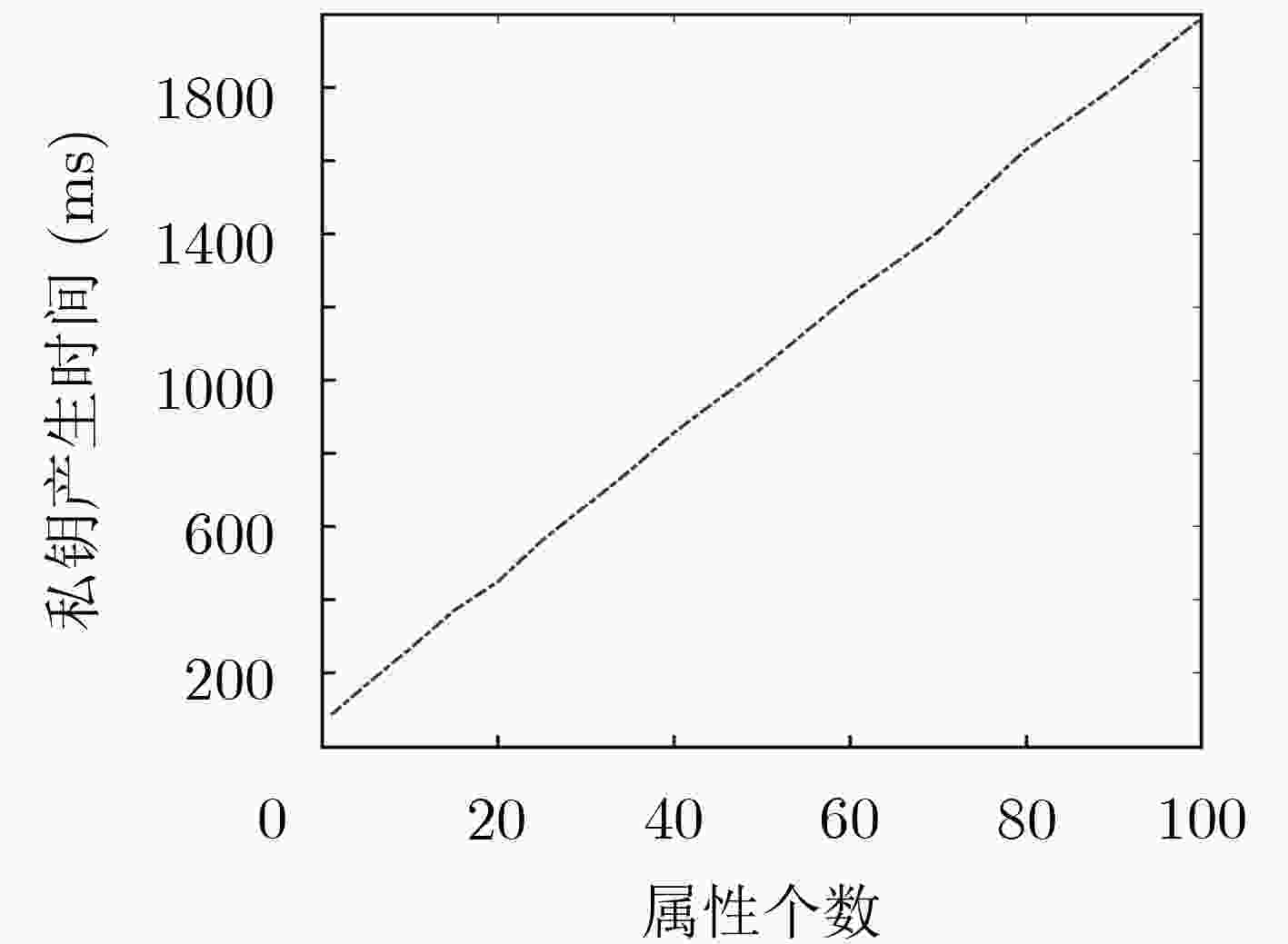
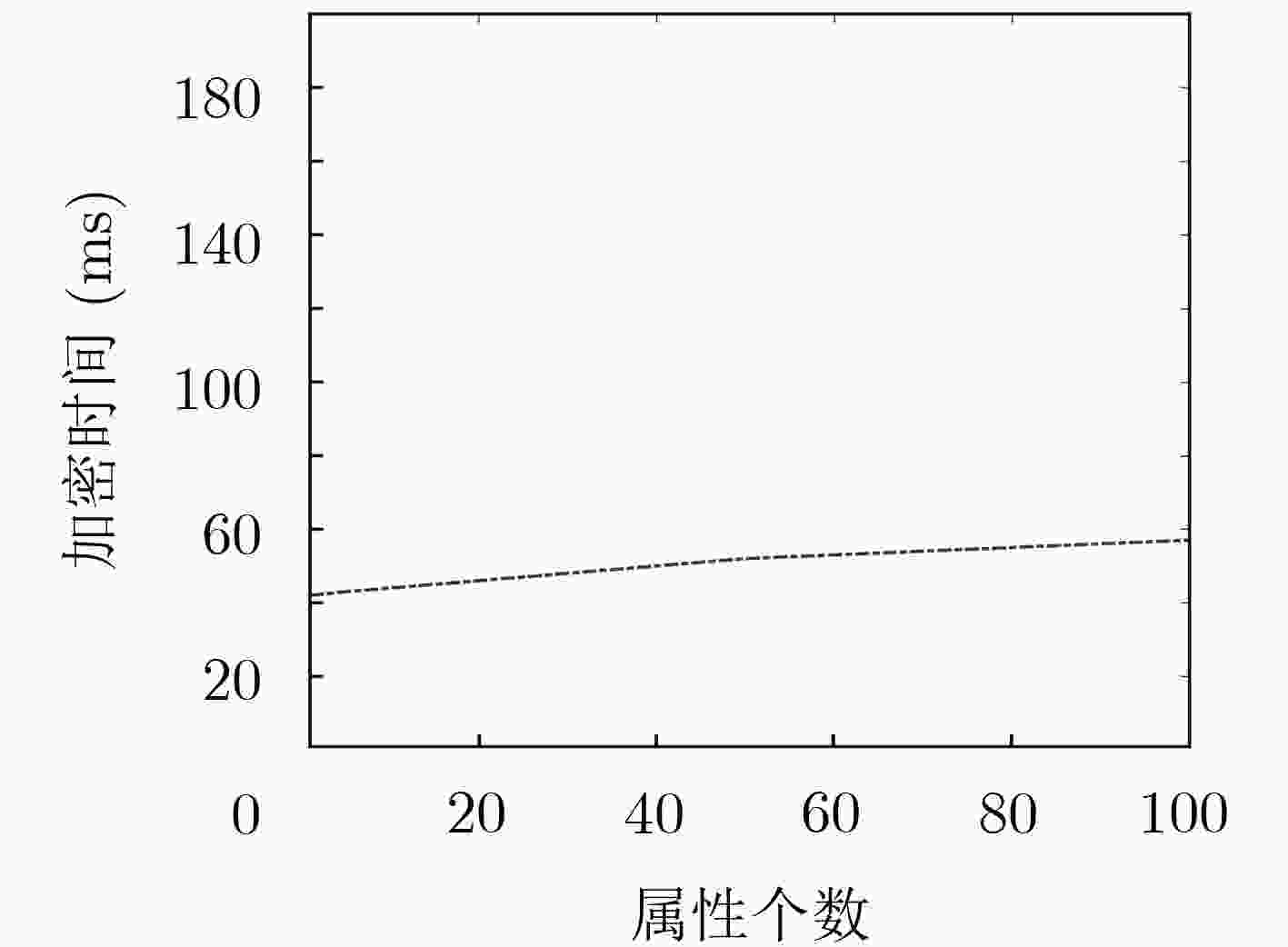
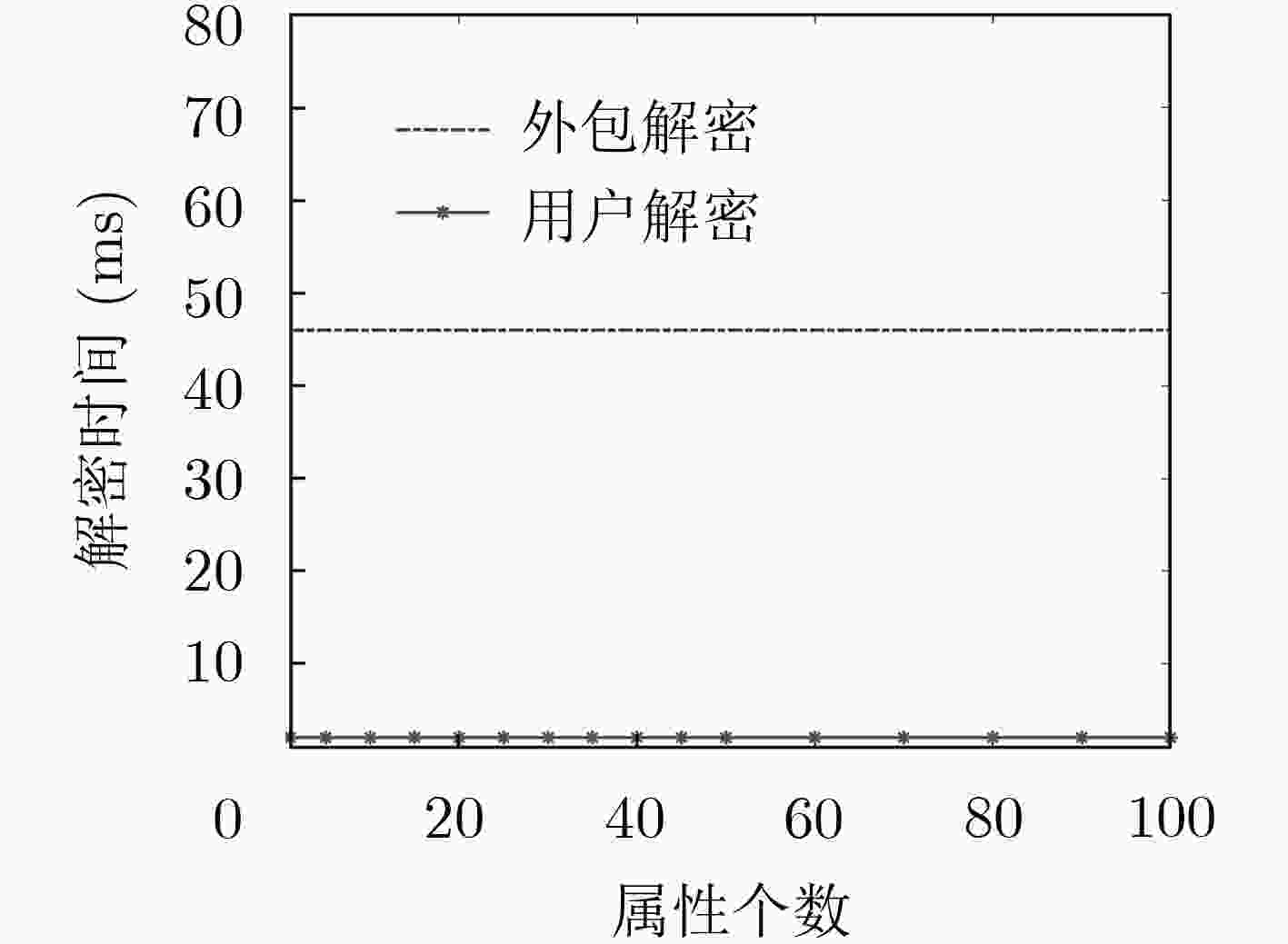
随着工业物联网(IoT)、云计算等信息技术与工业控制系统(ICS)的整合,工业数据的安全正面临着极大风险。为了能在这样一个复杂的分布式环境中保护数据的机密性和完整性,该文采用基于属性的加密(ABE)算法,设计一种集数据加密、访问控制、解密外包、数据验证为一体的通信方案,同时具有密文长度恒定的特点。最后,从正确性、安全性和性能开销3个方面对方案进行详细的分析,并通过仿真验证得出该算法具有低解密开销的优势。
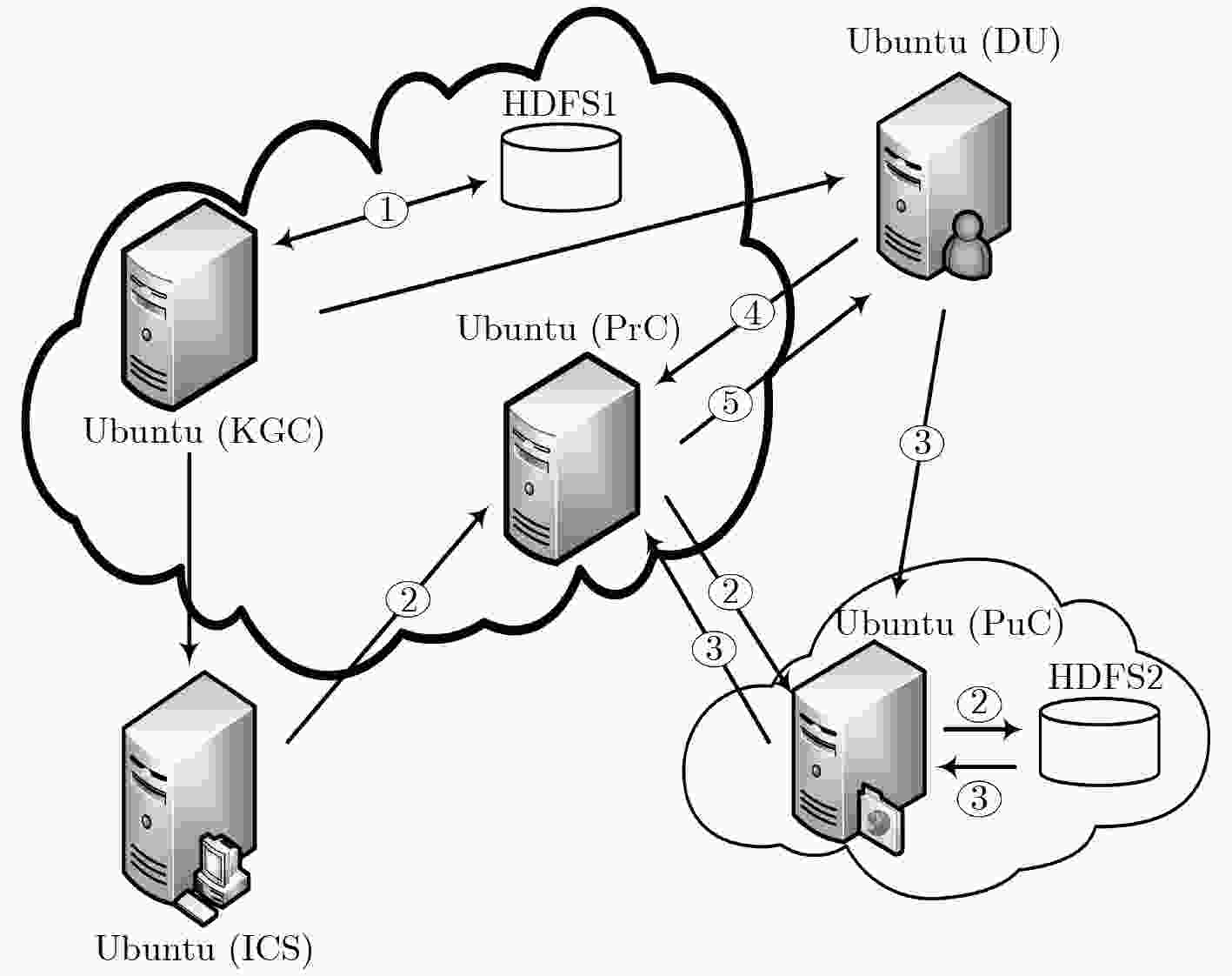
Abstract:With the integration of information technology such as industrial Internet of Things (IoT), cloud computing and Industrial Control System (ICS), the security of industrial data is at enormous risk. In order to protect the confidentiality and integrity of data in such a complex distributed environment, a communication scheme is proposed based on Attribute-Based Encryption (ABE) algorithm, which integrates data encryption, access control, decryption outsourcing and data verification. In addition, it has the characteristics of constant ciphertext length. Finally, the scheme is analyzed in detail from three aspectsie correctness, security and performance overhead. The simulation results show that the algorithm has the advantage of low decryption overhead.
-
表 1 方案性能比较
方案 是否外包解密 是否密文定长 是否可验证 私有云端密文长度 用户端密文长度 文献[16] 否 是 否 – $4\left| {{G_1}} \right|$ 文献[18] 是 否 对称密钥 $\left( {n + 2} \right)\left| {{G_1}} \right| + \left| {{G_T}} \right|$ $\left( {n + 2} \right)\left| {{G_1}} \right|$ 文献[19] 是 否 密文 $3\left| {{G_1}} \right| + \left| {{G_T}} \right|+2n\left| {{Z_p}} \right|$ $2\left| {{G_T}} \right|$ 本文方案 是 是 对称密钥/密文 $2\left| {{G_1}} \right| + \left| {{G_T}} \right|$ $\left| {{G_T}} \right|$ -
SAJID A, ABBAS H, and SALEEM K. Cloud-assisted IoT-based SCADA systems security: A review of the state of the art and future challenges[J]. IEEE Access, 2016, 4: 1375–1384. doi: 10.1109/ACCESS.2016.2549047 TRAUTMAN L J and ORMEROD P. Industrial cyber vulnerabilities: Lessons from stuxnet and the internet of things[J]. University of Miami Law Review, 2017, 72: 761–826. doi: 10.2139/ssrn.2982629 BABU B, IJYAS T, MUNEER P, et al. Security issues in SCADA based industrial control systems[C]. The 2nd International Conference on Anti-Cyber Crimes, Abha, Saudi Arabia, 2017: 47–51. doi: 10.1109/Anti-Cybercrime.2017.7905261. KRIAA S, PIETRE-CAMBACEDES L, BOUISSOU M, et al. A survey of approaches combining safety and security for industrial control systems[J]. Reliability Engineering & System Safety, 2015, 139: 156–178. doi: 10.1016/j.ress.2015.02.008 周小锋, 陈秀真. 面向工业控制系统的灰色层次信息安全评估模型[J]. 信息网络安全, 2014(1): 15–20. doi: 10.3969/j.issn.1671-1122.2014.01.004ZHOU Xiaofeng and CHEN Xiuzhen. Gray analytical hierarchical assessment model for Industry control system security[J]. Netinfo Security, 2014(1): 15–20. doi: 10.3969/j.issn.1671-1122.2014.01.004 HALAS M, BESTAK I, ORGON M, et al. Performance measurement of encryption algorithms and their effect on real running in PLC networks[C]. The 35th International Conference on Telecommunications and Signal Processing, Prague, Czech Republic, 2012: 161–164. doi: 10.1109/TSP.2012.6256273. LI Xing, LIU Mengxiang, ZHANG Rui, et al. Demo abstract: An industrial control system testbed for the encrypted controller[C]. The 9th ACM/IEEE International Conference on Cyber-Physical Systems, Porto, Portugal, 2018: 343–344. doi: 10.1109/ICCPS.2018.00045. 李兴. 工业控制系统加密控制器实验平台及方法研究[D]. [硕士论文], 浙江大学, 2018.LI Xing. Industrial control systems testbed and method study of the encrypted controller[D]. [Master dissertation], Zhejiang University, 2018. CHEMINOD M, DURANTE L, and VALENZANO A. Review of security issues in industrial networks[J]. IEEE Transactions on Industrial Informatics, 2013, 9(1): 277–293. doi: 10.1109/tii.2012.2198666 SAHAI A and WATERS B. Fuzzy identity-based encryption[C]. The 24th Annual International Conference on the Theory and Applications of Cryptographic Techniques, Aarhus, Denmark, 2005: 457–473. doi: 10.1007/11426639_27. BETHENCOURT J, SAHAI A, and WATERS B. Ciphertext-policy attribute-based encryption[C]. 2007 IEEE Symposium on Security and Privacy, Berkeley, USA, 2007: 321–334. RUJ S and NAYAK A. A decentralized security framework for data aggregation and access control in smart grids[J]. IEEE Transactions on Smart Grid, 2013, 4(1): 196–205. doi: 10.1109/TSG.2012.2224389 GUAN Zhitao, LI Jing, WU Longfei, et al. Achieving efficient and secure data acquisition for cloud-supported internet of things in smart grid[J]. IEEE Internet of Things Journal, 2017, 4(6): 1934–1944. doi: 10.1109/JIOT.2017.2690522 DAS P K, NARAYANAN S, SHARMA N K, et al. Context-sensitive policy based security in internet of things[C]. 2016 IEEE International Conference on Smart Computing, Louis, USA, 2016: 1–6. doi: 10.1109/SMARTCOMP.2016.7501684. CHAUDHARY R, AUJLA G S, GARG S, et al. SDN-enabled multi-attribute-based secure communication for smart grid in IIoT environment[J]. IEEE Transactions on Industrial Informatics, 2018, 14(6): 2629–2640. doi: 10.1109/TII.2018.2789442 DOSHI N and JINWALA D. Constant ciphertext length in CP-ABE[EB/OL]. https: //eprint.iacr.org/2012/500.pdf, 2012. 王建华, 王光波, 徐旸, 等. 解密成本为常数的具有追踪性的密文策略属性加密方案[J]. 电子与信息学报, 2018, 40(4): 802–810. doi: 10.11999/JEIT170198WANG Jianhua, WANG Guangbo, XU Yang, et al. Traceable ciphertext-policy attribute-based encryption scheme with constant decryption costs[J]. Journal of Electronics &Information Technology, 2018, 40(4): 802–810. doi: 10.11999/JEIT170198 QIN Baodong, DENG R H, LIU Shengli, et al. Attribute-based encryption with efficient verifiable outsourced decryption[J]. IEEE Transactions on Information Forensics and Security, 2015, 10(7): 1384–1393. doi: 10.1109/TIFS.2015.2410137 YANG Yang, LIU Ximeng, and DENG R H. Lightweight break-glass access control system for healthcare internet-of-things[J]. IEEE Transactions on Industrial Informatics, 2017, 14(8): 3610–3617. doi: 10.1109/TII.2017.2751640 -





 下载:
下载:


 下载:
下载:
