A Service Function Chain Deployment Method Against Side Channel Attack
-
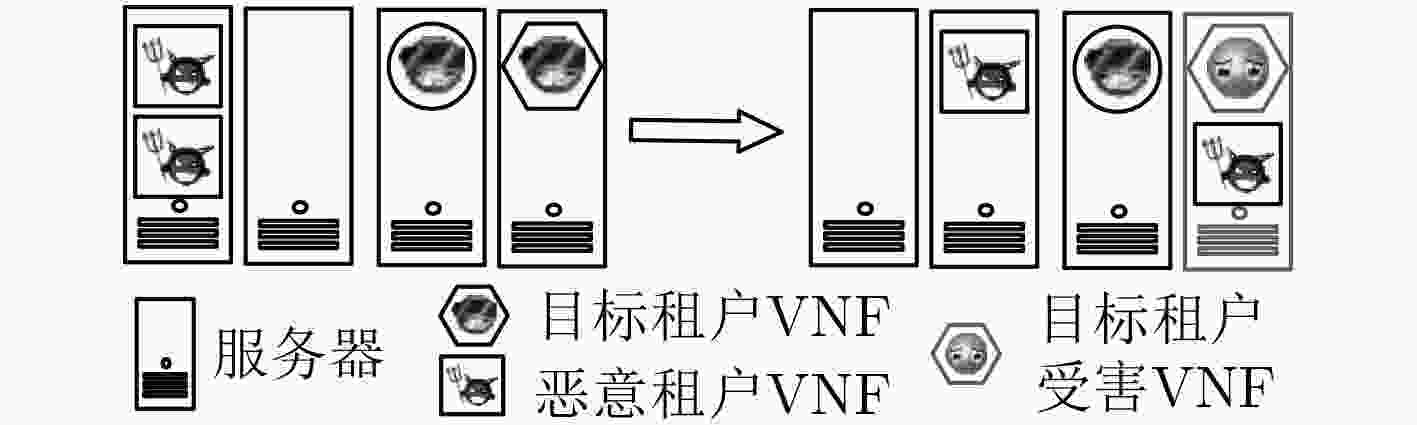
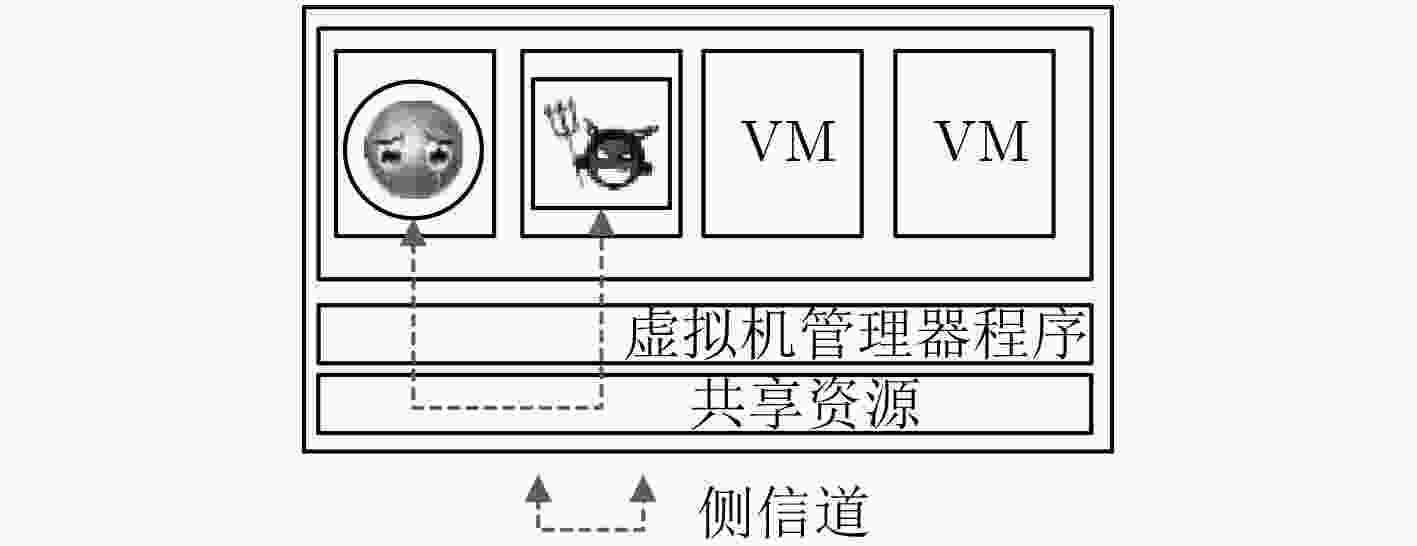
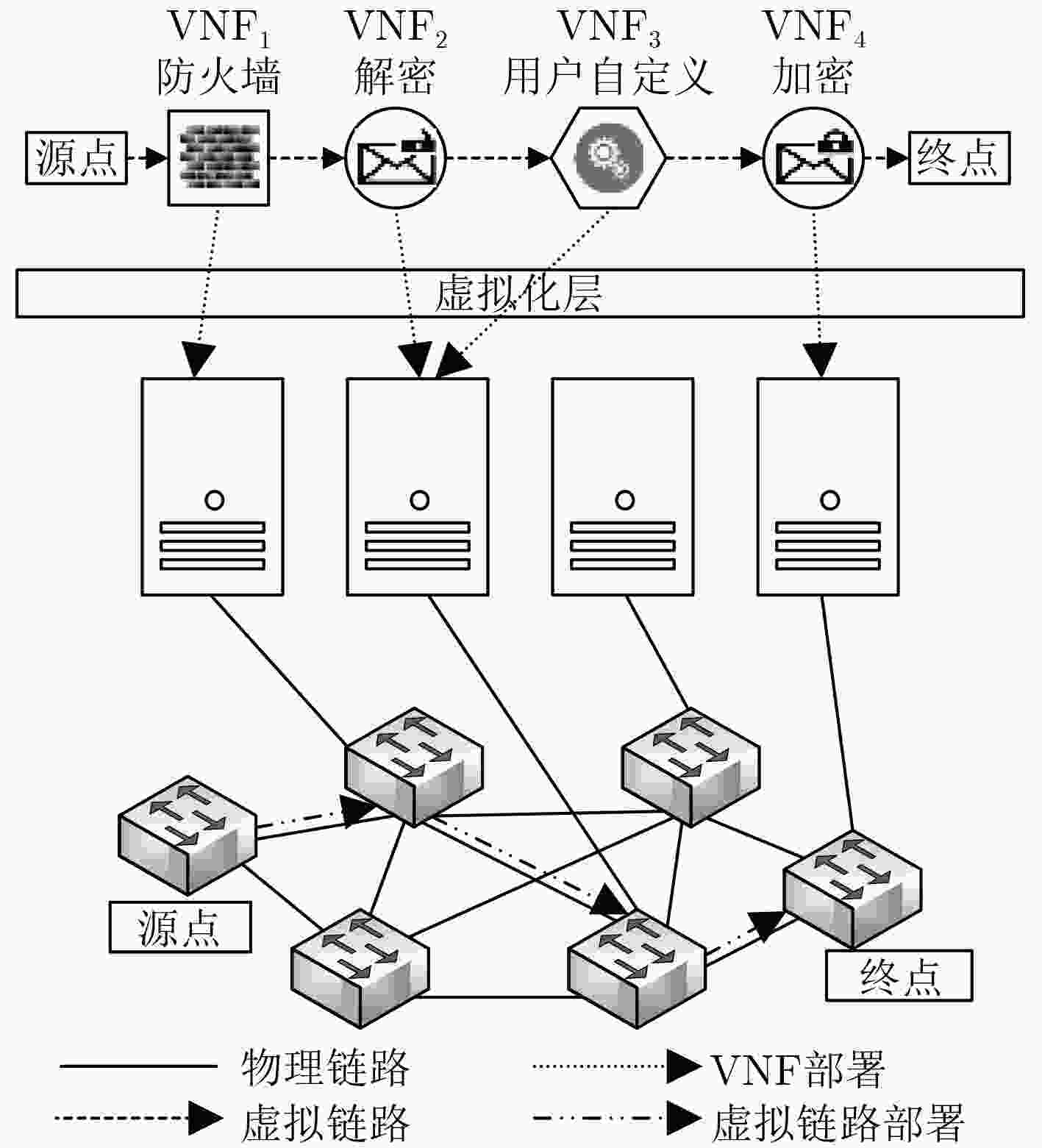
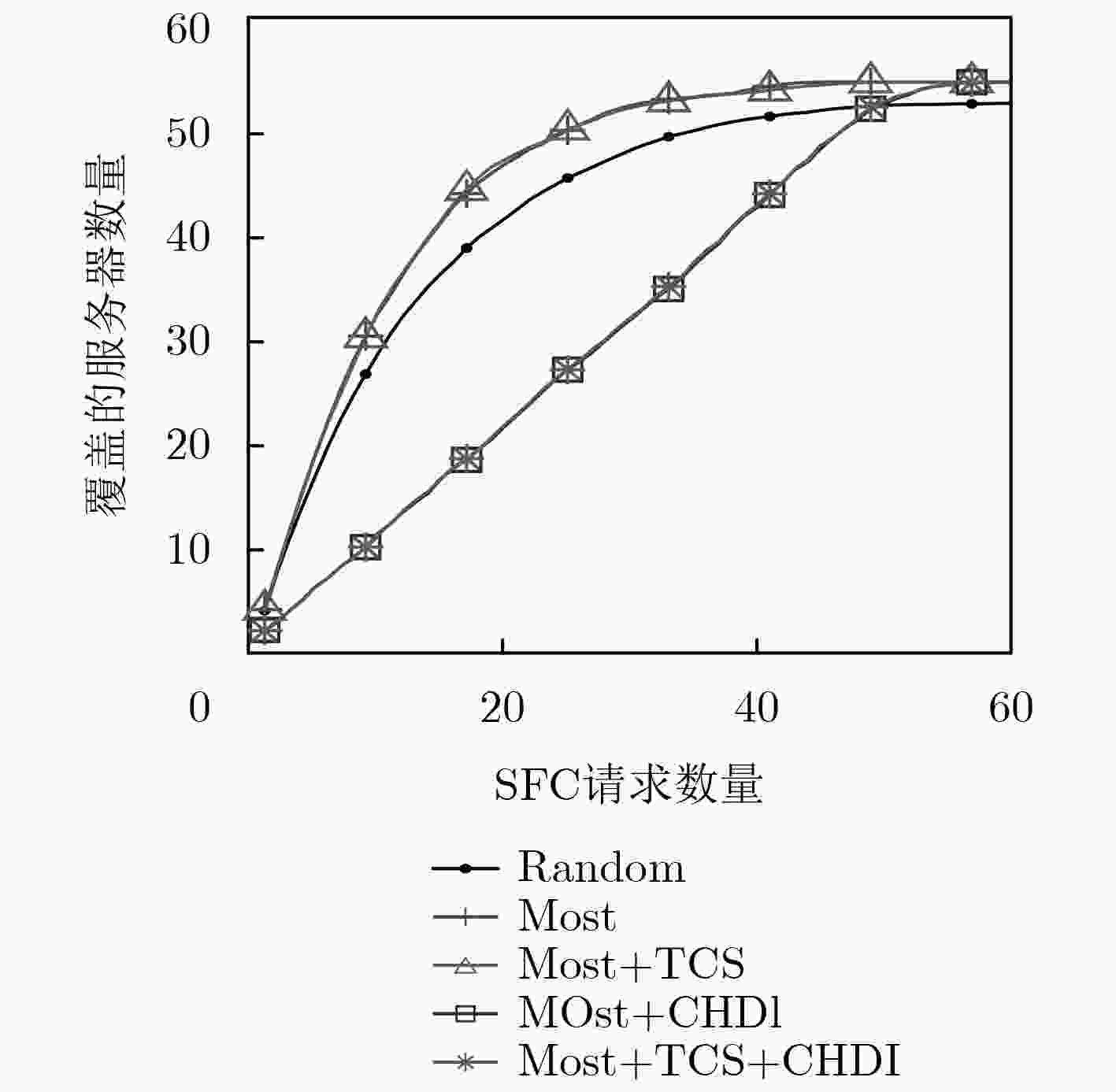
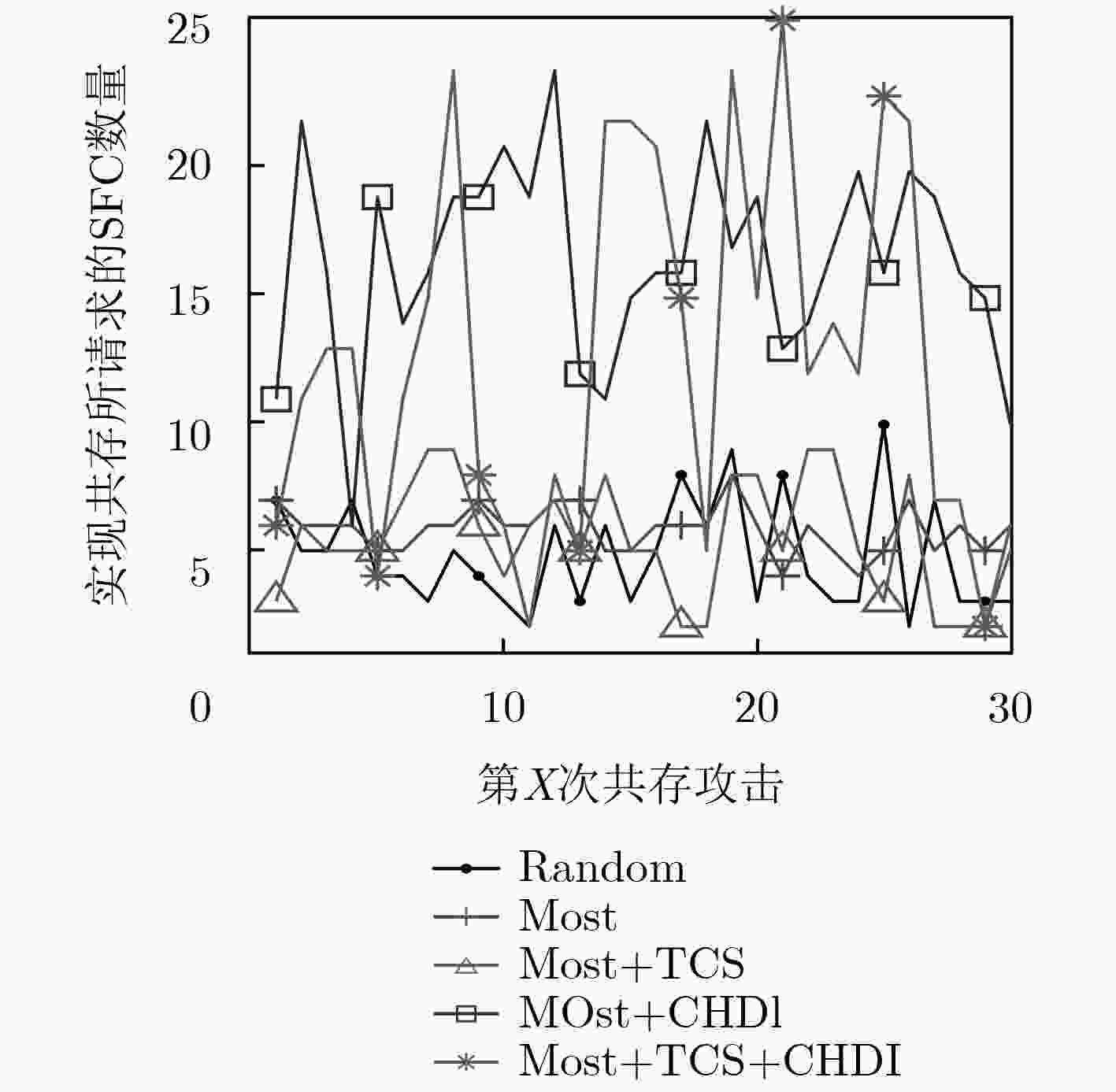
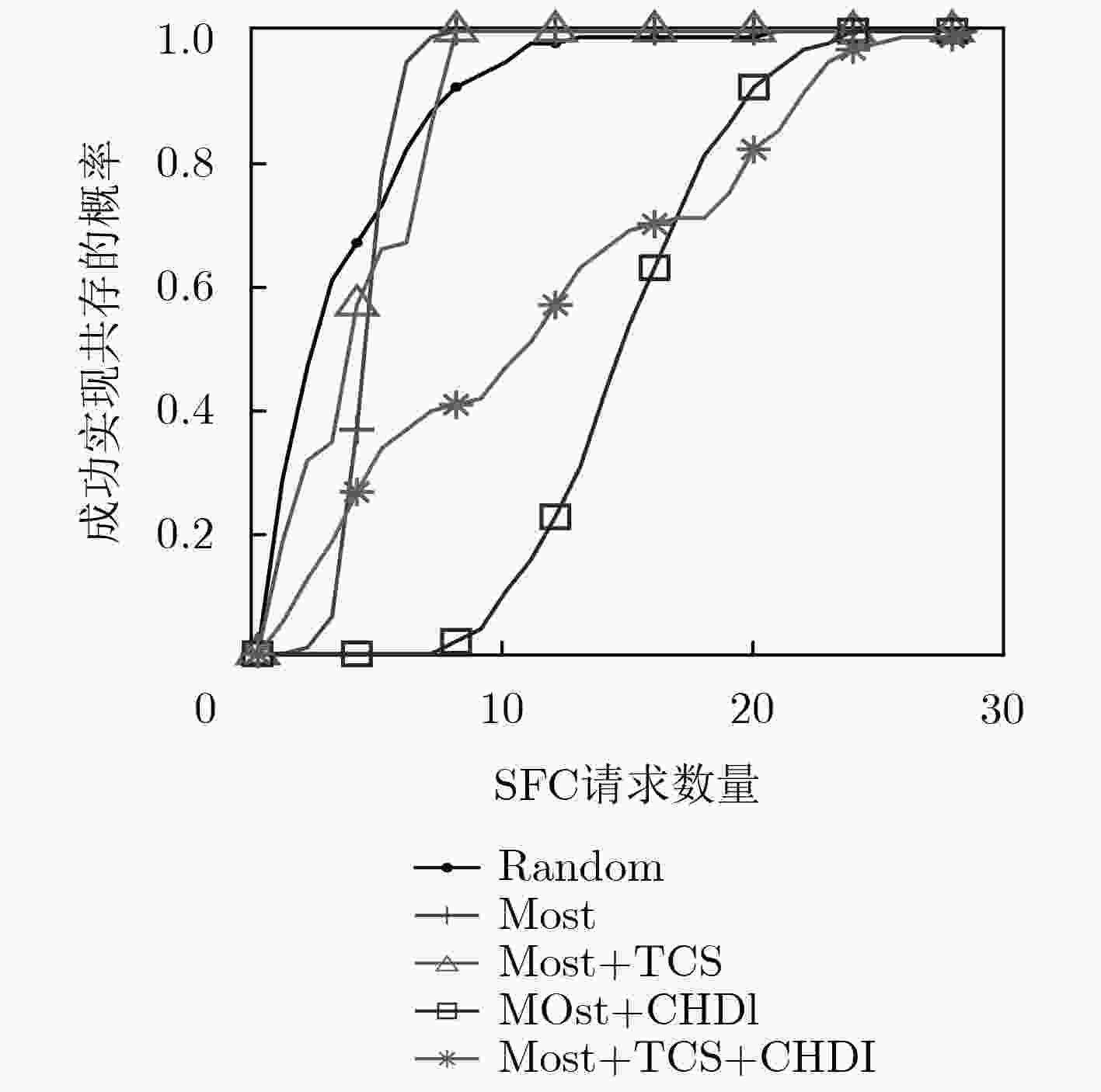
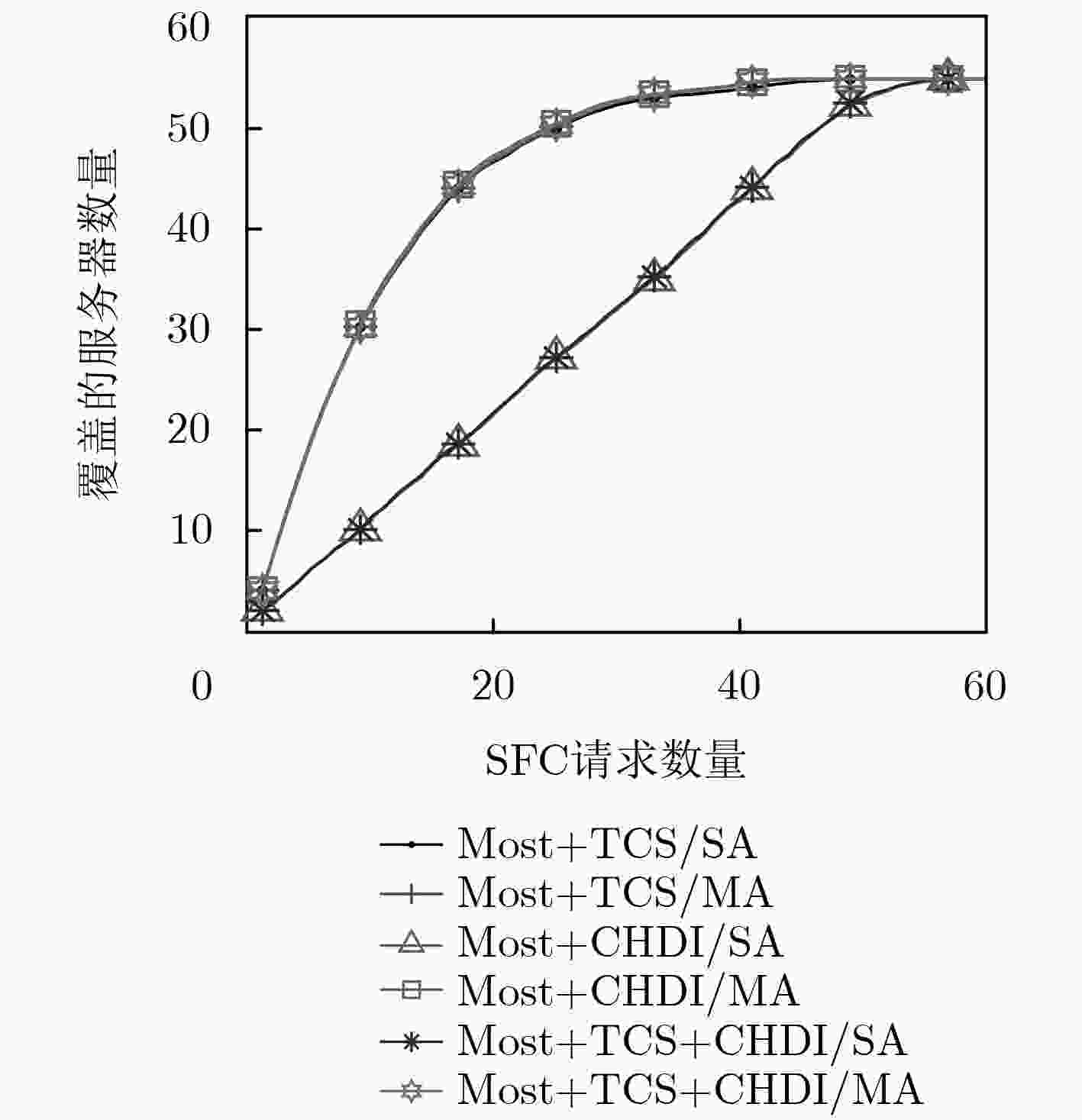
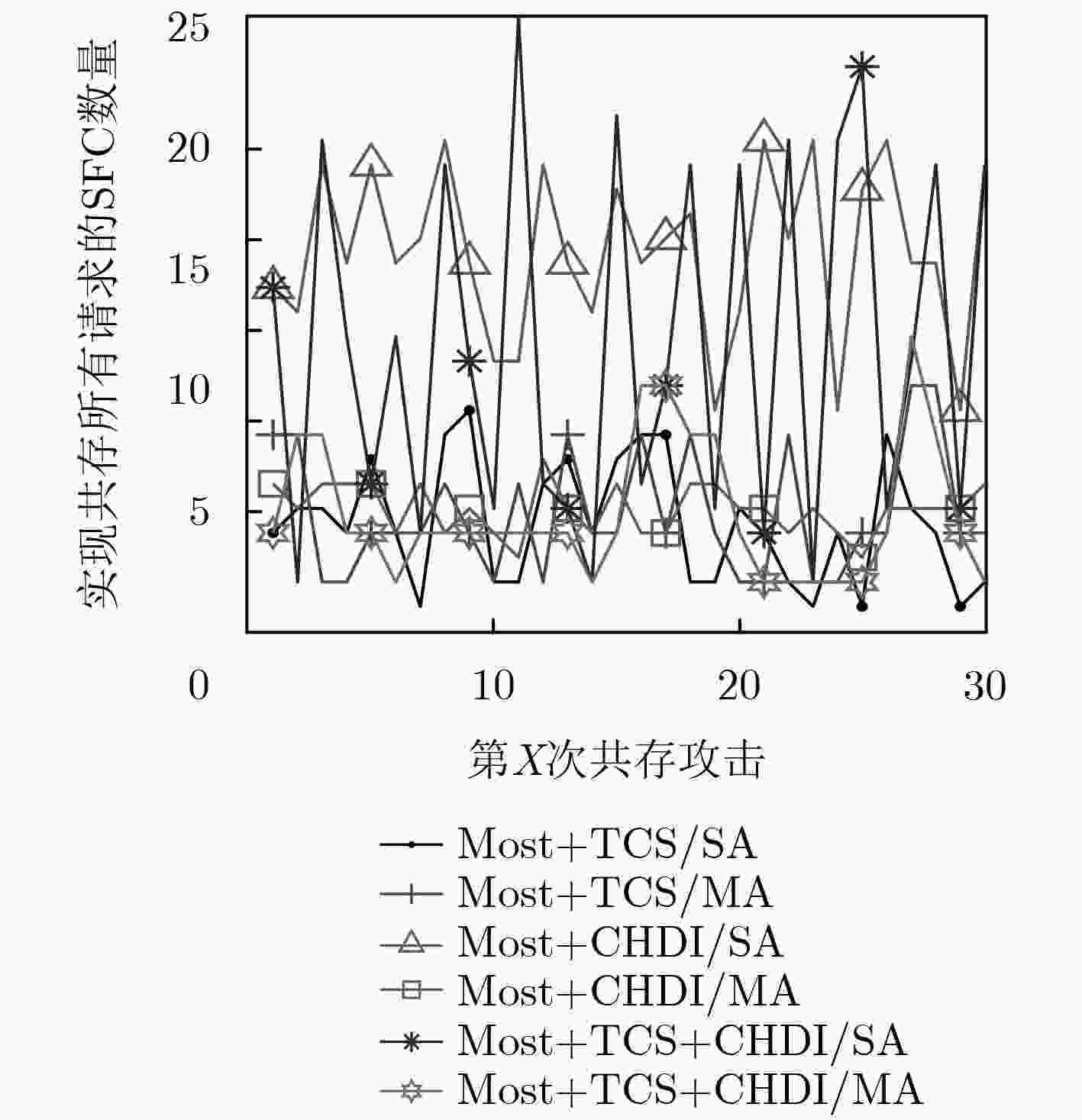
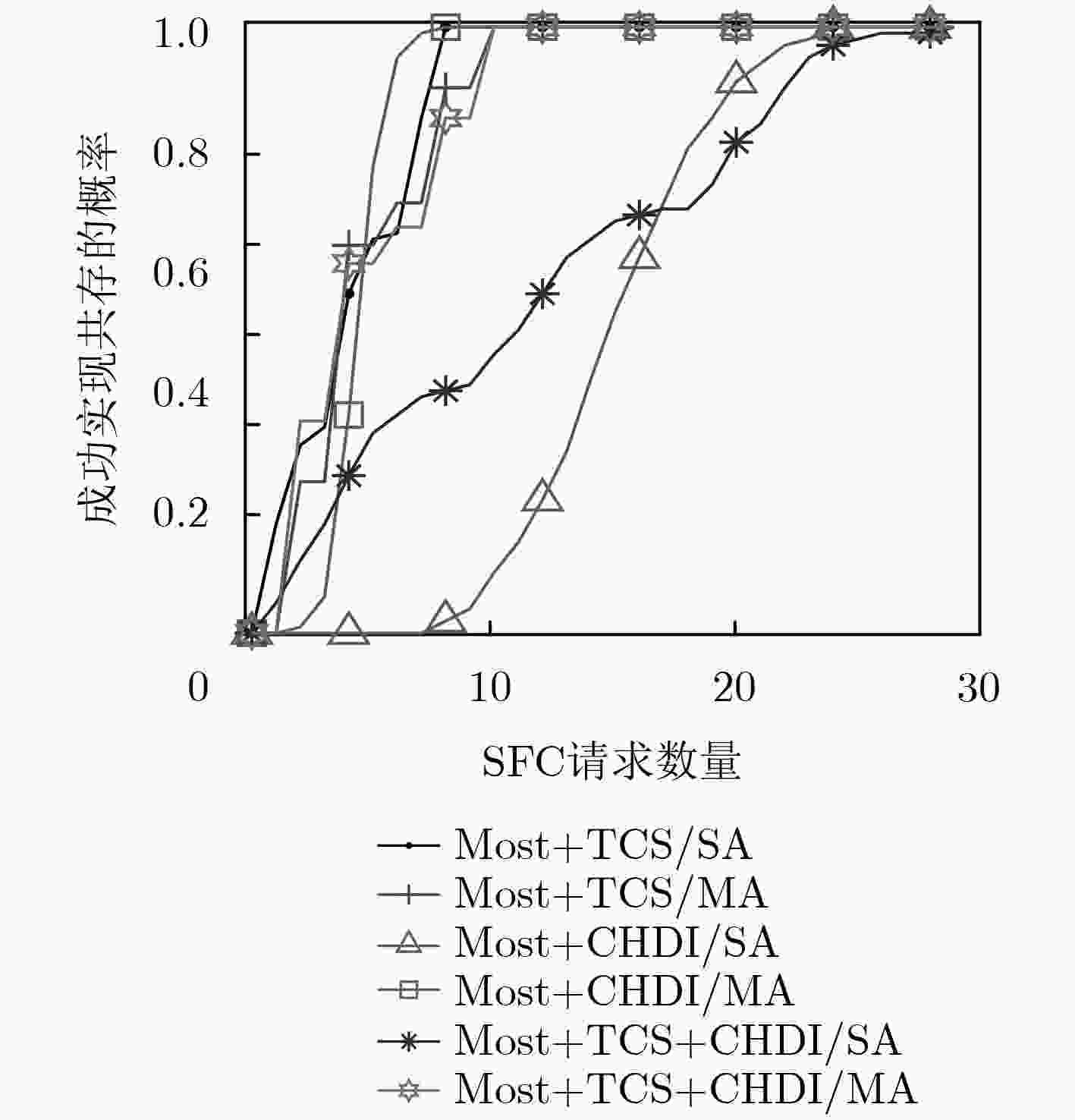
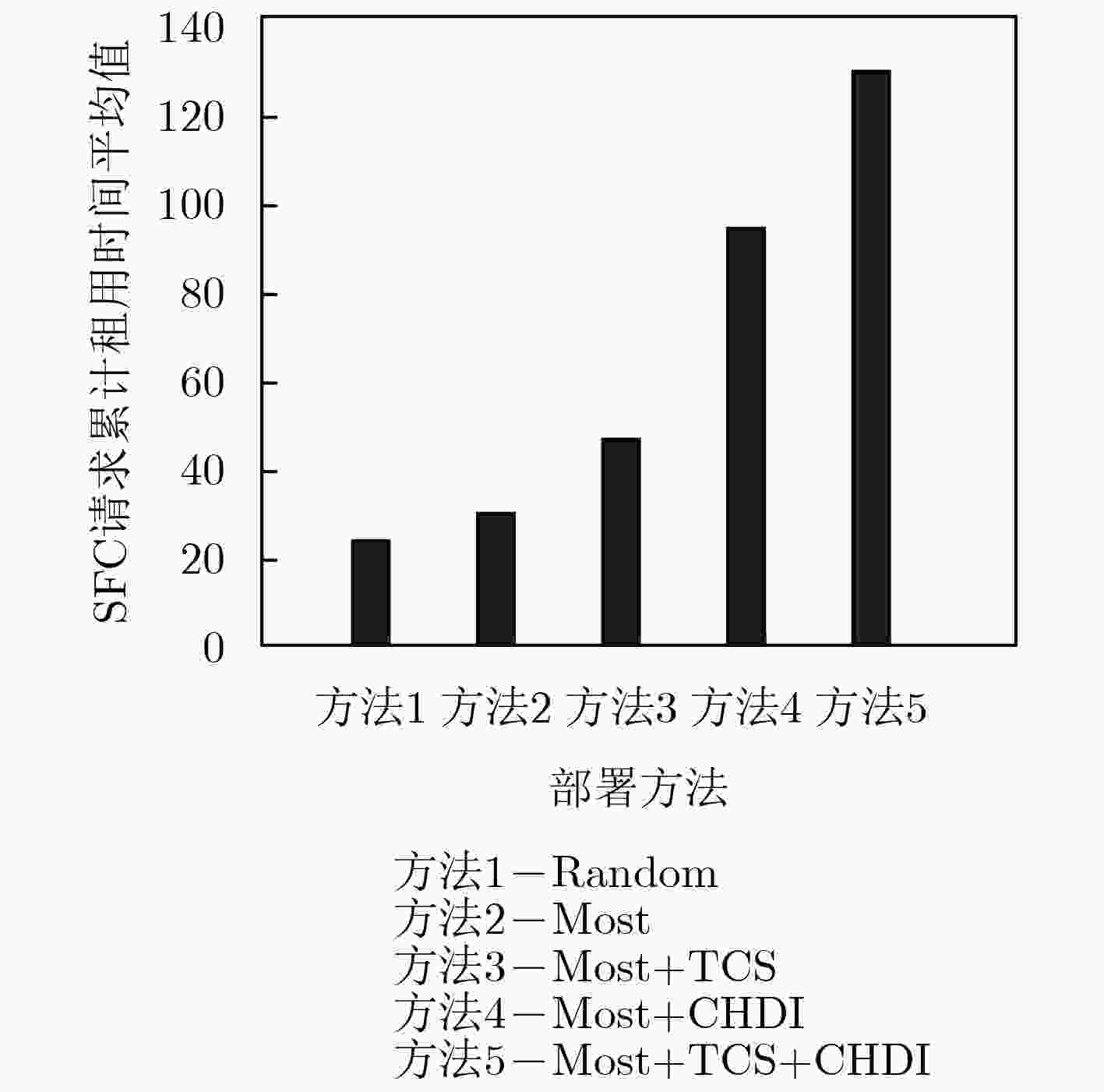
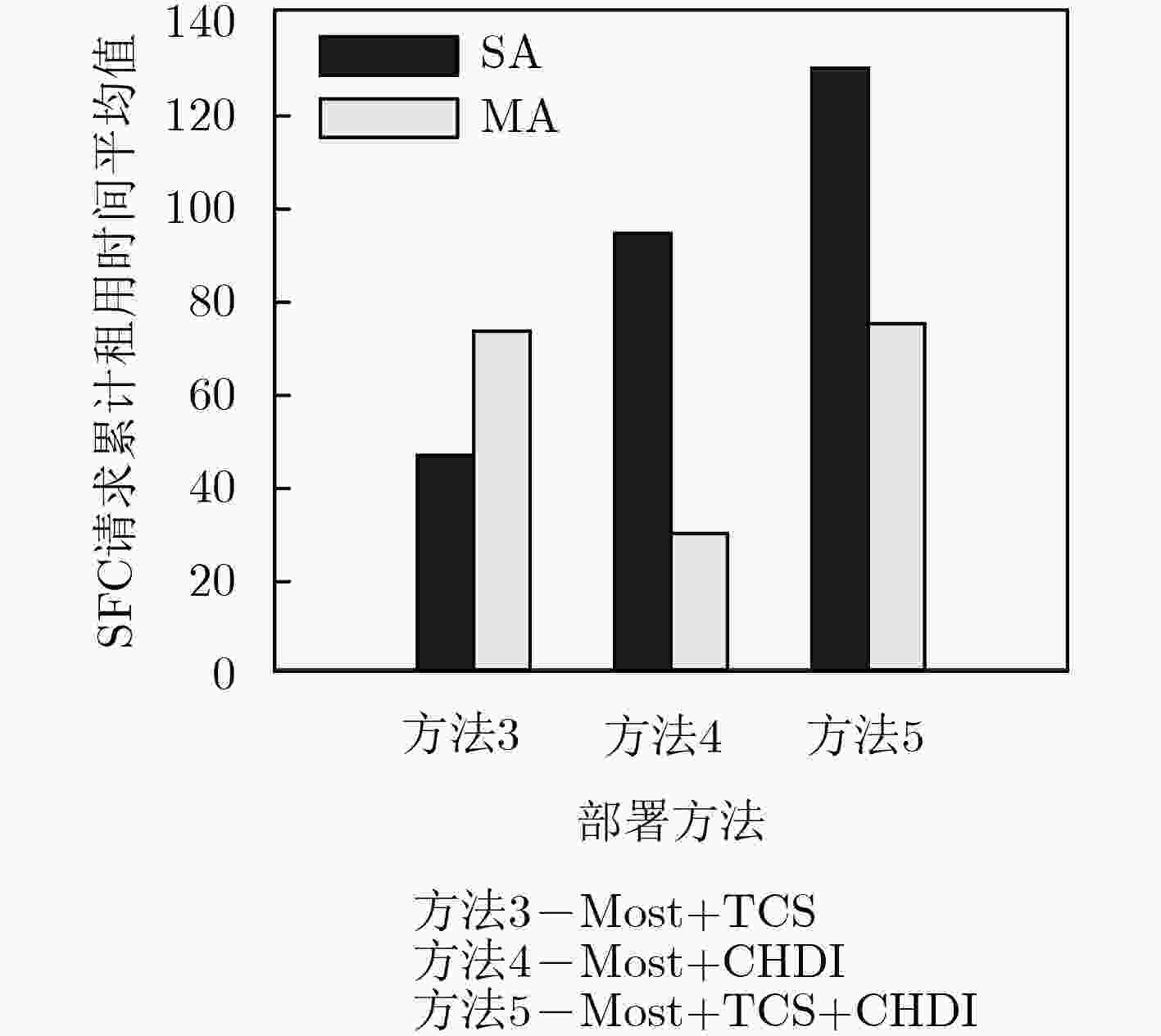
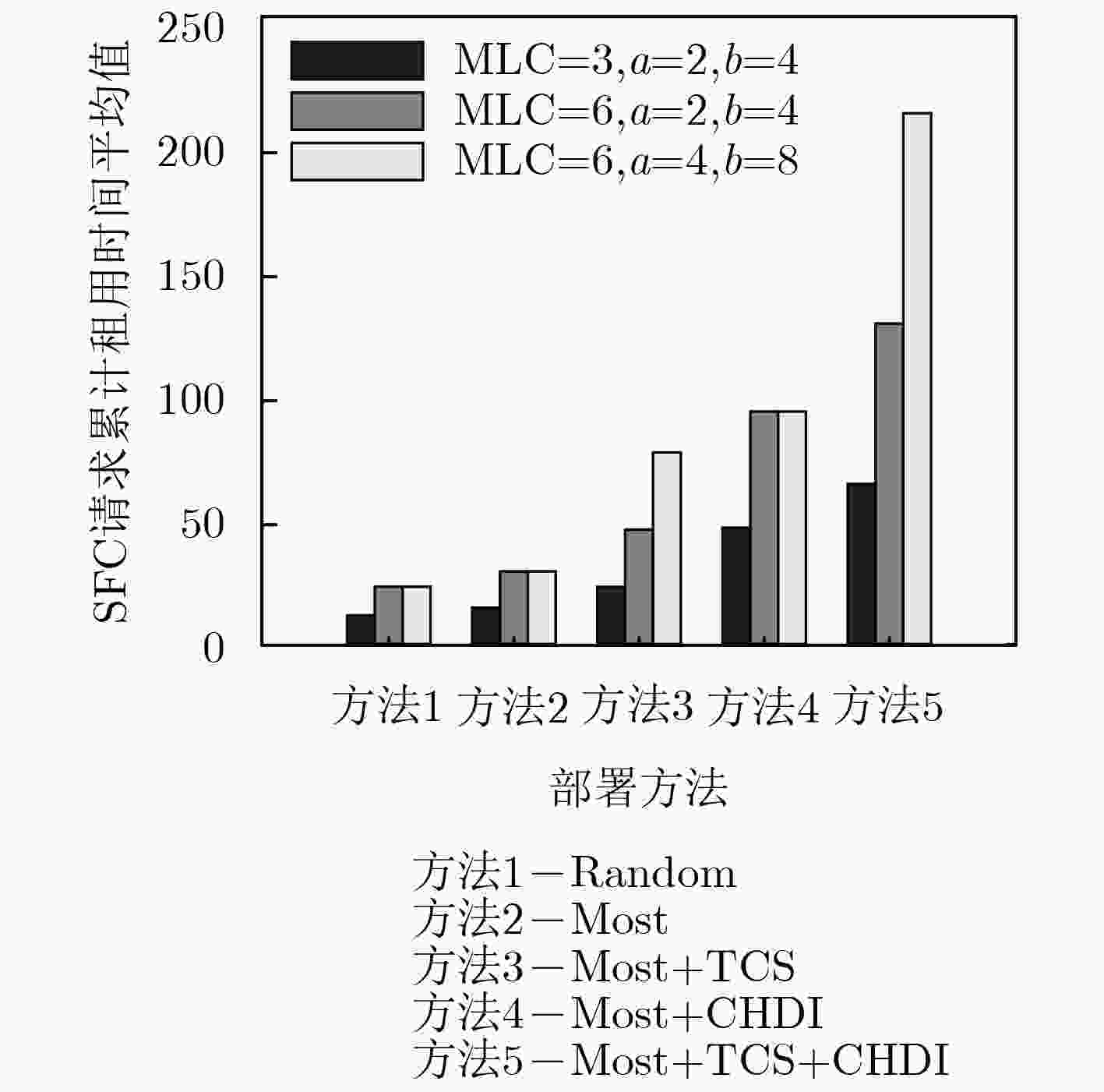
摘要: 侧信道攻击是当前云计算环境下多租户间信息泄露的主要途径,针对现有服务功能链(SFC)部署方法未充分考虑多租户环境下虚拟网络功能(VNF)面临的侧信道攻击问题,该文提出一种抗侧信道攻击的服务功能链部署方法。引入基于时间均值的租户分类策略以及结合历史信息的部署策略,在满足服务功能链资源约束条件下,以最小化租户所能覆盖的服务器数量为目标建立相应的优化模型,并设计了基于贪婪选择的部署算法。实验结果表明,与其他部署方法相比,该方法显著提高了恶意租户实现共存的难度与代价,降低了租户面临的侧信道攻击风险。Abstract: Side channel attack is the primary way to leak information between tenants in current cloud computing environment. However, existing Service Function Chain (SFC) deployment methods do not fully consider the side channel attack problem faced by the Virtual Network Function (VNF) in the multi-tenant environment. A SFC deployment method is proposed against side channel attack. A tenant classification strategy based on average time and a deployment strategy considering historical information are introduced. Under the resource constraints of the SFC, the optimization model is established with the goal of minimizing the number of servers that the tenant can cover. And a deployment algorithm is designed based on the greedy choice. The experimental results show that, compared with other deployment methods, this method can significantly improve the difficulty and cost of malicious tenant to realize co-residence, and reduces the risk of side channel attack faced by tenants.
-
表 1 基于租户分类和历史信息的部署算法
输入:服务功能链请求信息$r$ 输出:请求$r$的部署方案 (1) #租户分类 (2)计算平均运行时间${\rm{AVG}}_\eta ^{}$,确定请求所属租户${\eta ^r}$的分类XT; (3)依据分类结果,确定可部署服务器集合$\bar N_{}^{{\rm{XT}}}$以及租户${\eta ^r}$在该
区域已占用的服务器集合$\bar N_{{\eta ^r}}^{{\rm{XT}}}$;(4) #VNF部署 (5) SFCdpsucc=0, nodedpsucc=0#设置部署成败状态标志; (6) For each ${\rm{VNF}}_i^{\rm{r}}$in $\psi _{}^r$#遍历SFC请求中所有的m个VNF; (7) 筛选出$\bar N_{}^{{\rm{XT}}},\bar N_{{\eta ^r}}^{{\rm{XT}}}$中支持该类型VNF且剩余资源足够的
服务器集合$\bar N_{{\rm{VNF}}_i^{{r}}}^{{\rm{XT}}},\bar N_{{\eta ^r},{\rm{VNF}}_i^{{r}}}^{{\rm{XT}}}$;(8) If $\bar N_{{\eta ^r},{\rm{VNF}}_i^r}^{{\rm{XT}}}$不为空,则从中选取剩余资源最多的服务器
节点部署${\rm{VNF}}_i^r$;(9) If $\bar N_{{\eta ^r},{\rm{VNF}}_i^r}^{{\rm{XT}}}$为空,则从$\bar N_{{\rm{VNF}}_i^r}^{{\rm{XT}}}$中选取剩余资源最多的服
务器节点部署${\rm{VNF}}_i^r$;(10) 记录${\rm{VNF}}_i^r$所部属的服务器节点$n_i^r$,并对节点$n_i^r$资源
余量和$\bar N_{{\eta ^r}}^{{\rm{XT}}}$进行预更新;(11) If $\psi _{}^r$中所有的VNF均找到可部署服务器节点; (12) nodesucc=1,并对相关服务器节点资源余量和$\bar N_{{\eta ^r}}^{{\rm{XT}}}$进
行更新。(13) #虚拟链路部署 (14) linkdpsucc=0#设置链路部署成败状态标志; (15) If nodedpsucc==1; (16) For each $l_{i,i + 1}^r$ in $L_{}^r$#遍历该SFC请求中所有的虚拟
链路;(17) 确定节点$n_i^r$与$n_{i + 1}^r$之间带宽余量足够的可用链
路集合$\bar L_{n_i^r,n_{i + 1}^r}^{}$;(18) 从中筛选出部署代价$B_{\cos t}^r$最小的链路集合#存
在多条同等长度的链路;(19) 从中选取带宽资源余量最大的链路; (20) 记录所使用的链路,并对链路资源余量进行预
更新;(21) If $L_{}^r$中所有的虚拟链路找到可部署的物理链路; (22) linkdpsucc=1,并对相关物理链路资源余量进
行更新;(23) If (nodedpsucc and linkdpsucc)==1; (24) SFCdpsucc=1#该SFC请求部署成功; 表 2 VNF资源需求系数
VNF类型 NAT Firewall Proxy IDS UD_1 UD_2 UD_3 UD_4 计算资源需求/(单位带宽) 1 2 2 6 1 2 3 4 -
MEDHAT A M, TALEB T, ELMANGOUSH A, et al. Service function chaining in next generation networks: State of the art and research challenges[J]. IEEE Communications Magazine, 2017, 55(2): 216–223. doi: 10.1109/MCOM.2016.1600219RP 周伟林, 杨芫, 徐明伟. 网络功能虚拟化技术研究综述[J]. 计算机研究与发展, 2018, 55(4): 675–688. doi: 10.7544/issn1000-1239.2018.20170937ZHOU Weilin, YANG Yuan, and XU Mingwei. Network function virtualization technology research[J]. Journal of Computer Research and Development, 2018, 55(4): 675–688. doi: 10.7544/issn1000-1239.2018.20170937 BO Yi, WANG Xingwei, LI Keqin, et al. A comprehensive survey of Network Function Virtualization[J]. Computer Networks, 2018, 133: 212–262. doi: 10.1016/j.comnet.2018.01.021 袁泉, 汤红波, 黄开枝, 等. 基于Q-learning算法的vEPC虚拟网络功能部署方法[J]. 通信学报, 2017, 38(8): 172–182. doi: 10.11959/j.issn.1000-436x.2017173YUAN Quan, TANG Hongbo, HUANG Kaizhi, et al. Deployment method for vEPC virtualized network function via Q-learning[J]. Journal on Communications, 2017, 38(8): 172–182. doi: 10.11959/j.issn.1000-436x.2017173 GHAZNAVI M, KHAN A, SHAHRIAR N, et al. Elastic virtual network function placement[C]. Proceedings of the IEEE 4th International Conference on Cloud Networking, Niagara Falls, Canada, 2015: 1–7. MIJUMBI R, HASIJA S, DAVY S, et al. Topology-aware prediction of virtual network function resource requirements[J]. IEEE Transactions on Network and Service Management, 2017, 14(1): 106–120. doi: 10.1109/TNSM.2017.2666781 陈卓, 冯钢, 刘蓓, 等. 运营商网络中面向资源碎片优化的网络服务链构建策略[J]. 电子与信息学报, 2018, 40(4): 763–769. doi: 10.11999/JEIT170641CHEN Zhuo, FENG Gang, LIU Bei, et al. Construction policy of network service chain oriented to resource fragmentation optimization in operator network[J]. Journal of Electronics &Information Technology, 2018, 40(4): 763–769. doi: 10.11999/JEIT170641 QU Long, ASSI C, SHABAN K, et al. A reliability-aware network service chain provisioning with delay guarantees in NFV-enabled enterprise datacenter networks[J]. IEEE Transactions on Network and Service Management, 2017, 14(3): 554–568. doi: 10.1109/TNSM.2017.2723090 FIROOZJAEI M D, JEONG J, KO H, et al. Security challenges with network functions virtualization[J]. Future Generation Computer Systems, 2017, 67: 315–324. doi: 10.1016/j.future.2016.07.002 梁鑫, 桂小林, 戴慧珺, 等. 云环境中跨虚拟机的Cache侧信道攻击技术研究[J]. 计算机学报, 2017, 40(2): 317–336. doi: 10.11897/SP.J.1016.2017.00317LIANG Xin, GUI Xiaolin, DAI Huijun, et al. Cross-VM cache side channel attacks in cloud: A survey[J]. Chinese Journal of Computers, 2017, 40(2): 317–336. doi: 10.11897/SP.J.1016.2017.00317 ZHANG Xu, WANG Haining, and WU Zhenyu. A measurement study on co-residence threat inside the cloud[C]. Proceedings of the 24th USENIX Conference on Security Symposium, Washington, USA, 2015: 929–944. ATYA A O F, QIAN Zhiyun, KRISHNAMURTHY S V, et al. Malicious co-residency on the cloud: Attacks and defense[C]. Proceedings of IEEE Conference on Computer Communications, Atlanta, USA, 2017: 1–9. 赵硕, 季新生, 毛宇星, 等. 基于安全等级的虚拟机动态迁移方法[J]. 通信学报, 2017, 38(7): 165–174. doi: 10.11959/j.issn.1000-436x.2017091ZHAO Shuo, JI Xinsheng, MAO Yuxing, et al. Research on dynamic migration of virtual machine based on security level[J]. Journal on Communications, 2017, 38(7): 165–174. doi: 10.11959/j.issn.1000-436x.2017091 ZHANG Tianwei, ZHANG Yinqian, and LEE R B. CloudRadar: A real-time side-channel attack detection system in clouds[C]. Proceedings of 19th International Symposium on Research in Attacks, Intrusions, and Defenses, Paris, France, 2016: 118–140. NOSHY M, IBRAHIM A, and ALI H A. Optimization of live virtual machine migration in cloud computing: A survey and future directions[J]. Journal of Network and Computer Applications, 2018, 110: 1–10. doi: 10.1016/j.jnca.2018.03.002 LIU Shuhao, CAI Zhiping, XU Hong, et al. Towards security-aware virtual network embedding[J]. Computer Networks, 2015, 91: 151–163. doi: 10.1016/j.comnet.2015.08.014 HAN Yi, CHAN J, ALPCAN T, et al. Using virtual machine allocation policies to defend against co-resident attacks in cloud computing[J]. IEEE Transactions on Dependable and Secure Computing, 2017, 14(1): 95–108. doi: 10.1109/TDSC.2015.2429132 HAN Yi, ALPCAN T, CHAN J, et al. A game theoretical approach to defend against co-resident attacks in cloud computing: Preventing co-residence using semi-supervised learning[J]. IEEE Transactions on Information Forensics and Security, 2016, 11(3): 556–570. doi: 10.1109/TIFS.2015.2505680 LI Defang, HONG Peilin, XUE Kaiping, et al. Virtual network function placement considering resource optimization and SFC requests in cloud datacenter[J]. IEEE Transactions on Parallel and Distributed Systems, 2018, 29(7): 1664–1677. doi: 10.1109/TPDS.2018.2802518 BARI F, CHOWDHURY S R, AHMED R, et al. Orchestrating virtualized network functions[J]. IEEE Transactions on Network and Service Management, 2016, 13(4): 725–739. doi: 10.1109/TNSM.2016.2569020 -





 下载:
下载:


 下载:
下载:
